Duo's Trusted Access Solution
Trust Every User With
Two-Factor Authentication
Verify the identity of your users with two-factor authentication and the health of their devices before they connect to the apps you want them to access.
Try Duo for FreeWhat You Get With Duo:
Sign up for a free 30-day trial to get full access to the features of our Trusted Access suite and start securing your users in minutes.
That includes everything in Duo MFA:
- Protect logins with two-factor authentication and easily enroll and manage users
- Automate the management of your Duo solution (i.e. admin APIs)
- Get an overview of device security hygiene
- Protect on-premises apps and federated cloud apps

Plus Advanced Duo Access Features:
- Enforce role-based access policies
- Identify users vulnerable to phishing attacks
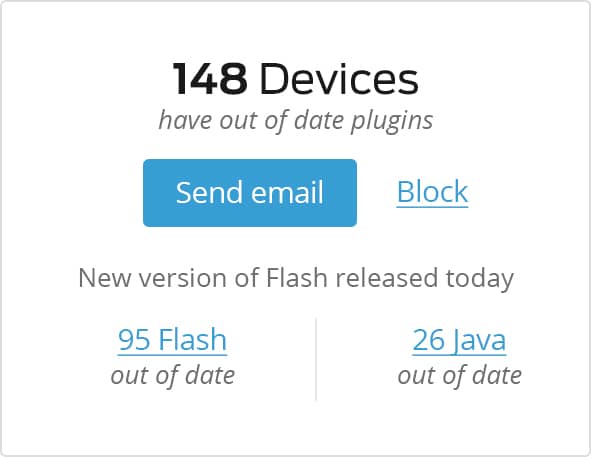
- Monitor and identify risky devices
- Control what endpoints can access apps based on device hygiene
- Automatically encourage users to update their own devices
- Native support for protecting all cloud apps
Learn more in Duo’s Pricing.
Duo’s London, U.K. location also provides all European customers with sales and technical support services during European hours, and extended technical support hours from other offices around the world.
-
After testing a couple of options, Duo stood out like a Rolls Royce in comparison to a Mini. It’s a standout product that has the wow factor and - as someone with ten years’ experience of working with dual factor authentication - I knew instantly that I need look no further.
— Richard Gough, Group IT Operations and Security Manager, Punter Southall -
Duo's just been really simple, straightforward, and it hasn't got in the way of what we've been trying to do.
— Richard Fuller, Linux and Information Security Team Leader, University of York -
“What particularly impressed us was the simplicity of the cloud-based system which meant that users were actually able to enroll themselves onto the system, removing the burden on IT support.”
— Giacomo Collini, Director of Information Security, King.com






