The TL;DR
Are you wondering what the best Bluetooth scanner is? Or what the most commonly used Bluetooth software is? We’ve wondered that too. We’ve examined several, compared features and capabilities, and discovered that while the best appears to be the Nordic Semiconductor nRF-51DK, a number of selections exist that give good results for different situations. A solid strategy is to have multiple choices while focusing on the best one for the situation at hand.
Background
The idea of approaching IoT investigation with Bluetooth probing and sniffing is twofold. The first is to simply check to make sure the attack surface of Bluetooth is safe. The second is to assist in other areas of an IoT investigation, such as finding input points that could help map out attack vectors or identify how device information is leaked that could allow for easy tracking of an individual or their expensive new IoT device (or both).
Duo Labs has done research on multiple IoT devices that use Bluetooth, and like many people, we are left scratching our heads at how good or bad some of the testing tools are. Unfortunately, to perform every Bluetooth probe and scan perfectly requires a high dollar investment, so most of us are left with the choice of figuring out the best tool for the job.
There is nothing more frustrating than having a testing tool that is inconsistent, or one that does only one thing better than every other tool while performing additional tasks mediocre at best. Finding consistency when scanning and probing is hard, and this is in part due to the nature of Bluetooth itself - it is a frequency-hopping set of protocols stacked on top of each other that transmits data at a signal much weaker than Wi-Fi.
As a result, some hardware tools in certain environments do not perform well or consistently. Some hardware tools are specifically tailored to excel in specific environments only. And some do weird things like deliver that one thing - that single thing you wished every tool you had would do as well.
So we looked at tools with several different areas in mind:
- Lab work, including sniffing and probing
- Field work, with both the ability to quickly find close-range targets as well as longer range targets using more sophisticated hardware with larger antennas
- Programmability, for the serious hacker doing serious experimentation.
We’ll touch a bit on platforms versus the tools that run on them, and speak about which tools work best on which platform. The platform choice list isn’t going to be comprehensive, but should cover enough to get you going and thinking. Normally, we’d specify our overall strategy for examining these tools with some type of guidelines, but in this case, we will stick to pointing out strengths and weaknesses - with an emphasis on strengths in terms of a good tool to have in a researcher’s toolbox.
Laptops
Before we get to applications on the computer, we need to discuss the computer itself- we’ll assume that users will choose a laptop over a desktop system. Bluetooth, by nature, implies mobility, and chasing it down via a mobile platform makes the most sense. With Bluetooth and Wi-Fi issues around IoT, the idea of “field work” makes sense, so your platform should do the same.
You can use any operating system (OS) you want - all will involve limitations to some degree.
| OS | Pro | Con |
|---|---|---|
| Windows | - Mature drivers - Most high-end ($$) software packages are supported on Windows only | - Lack of quality freeware choices |
| macOS | - More freeware choices than Windows | - Many software utilities are ports, some with features removed or unsupported for macOS |
| Linux | - Large selection of high-quality open-sourced choices of utilities - Many hardware solutions are better (or only) supported on Linux flavors | - Lack of GUI interfaces in many utilities - Lack of consistent output formats - Driver support is sometimes lacking, partially dependent on the laptop hardware itself |
On software alone, Linux comes out way ahead, especially if you are a command-line kind of hacker, but the driver support is an issue. This is that phenomena where you buy the HP or Dell laptop with Windows pre-installed, and then wipe it to install Linux - only to find that the Linux drivers for interacting with the hardware are somewhat generic.
The Windows drivers are usually written by the laptop vendor to ensure they work perfectly with their hardware. You can find this for Linux if you purchase your laptop from a company that ships their hardware with Linux and Linux only, and writes their own custom drivers for their hardware.
This is why System 76 is such a great choice, as they develop and maintain their own drivers for Ubuntu, which is the only operating system they ship with. As a result, their interaction with both Bluetooth and Wi-Fi is very high quality, and questionable wireless tools become a lot more stable and useful.
 Figure 1. The System76 Galago Pro. Lightweight with customized drivers to talk to their hardware.
Figure 1. The System76 Galago Pro. Lightweight with customized drivers to talk to their hardware.
While it is entirely a personal choice, we feel that running Ubuntu on vendor-supported hardware is a solid way to go, and from the experience of using all three operating systems in a research capacity, this seems to deliver really consistent results - especially with Bluetooth.
Don’t get us wrong, there may be features offered on other laptops that you can’t live without, like a specific keyboard that could outweigh other advantages, but speaking directly to Bluetooth and wireless protocols in general, you might be a leg up with Linux on a system designed with Linux in mind.
A word on Kali Linux: if your need is for an all-around research/penetration test system, this is a decent choice, but bear in mind that the selection of apps for Kali are geared more toward pentesting. For example, many of the Bluetooth utilities on Kali are for attacking and are often written for a single exploit (or class of exploits), and many of these exploits have been patched in modern systems.
Bluetooth Hardware Devices
There are tons of decent add-on hardware choices when it comes to Bluetooth. When we say add-on hardware choices, we are typically referring to USB devices that provide features and capabilities that the built-in Bluetooth in your laptop doesn't have. As previously stated, we don’t recommend a single one over another; we recommend using multiple, specialized devices. If that sounds like we are suggesting more than one, it is because that’s quite possibly the direction you will be headed.
The main thing to keep in mind is that the device should support modern Bluetooth - so if you see something like “Classic Bluetooth and Bluetooth Low Energy” or version 4.0 or later, you should be good. Both “flavors” were combined with version 4.0 of the Bluetooth spec, so it should support both if it is fully 4.0 or later. As of this writing, most IoT that supports Bluetooth also supports 4.0 or later.
Some IoT devices will refer to using LE, BLE, BTLE, or some other variance of the name for “Bluetooth Low Energy” - but again, if your USB plugin device supports 4.0 or later, you should be fine.
If any device claims to support Bluetooth 5.x, great - just make sure that extra care was used to cover some of the nuances of 5. Version 5 comes with greater speed, different battery usage, and so on, so make sure the device is truly supporting 5 from the firmware and isn’t just tweaked 4.x hardware that cannot take full advantage of something like higher performance while using less power.
Small Dongles
There are tons of choices when it comes to simple dongles. Even older ones like the SMK-Link Nano are probably fine. The main disadvantage is lack of decent support on macOS, and weird Windows support. Starting with Windows 8 there were changes made to the Bluetooth drivers, so some dongles will work fine up through Windows 7 only, whereas others only support Windows 8 and newer. If your choice is Linux, most will work with the normal Bluetooth drivers, such as Bluez, and should handle tasks like scanning with ease.
 Figure 2. SMK-Link Nano. Check the bottom of your computer bag, you might own one with no knowledge of how you got it.
Figure 2. SMK-Link Nano. Check the bottom of your computer bag, you might own one with no knowledge of how you got it.
Dongles in this class are not a great choice for sniffing, unless you are using Wireshark to sniff from the dongle while you are using a tool to do probing with the same dongle. Basic promiscuous sniffing capabilities with these dongles is usually nonexistent. Their strengths are in their ability to offer slightly better performance during basic scans for Bluetooth devices in the immediate area; for anything beyond that, you’re lucky if you get stable and consistent results. If you’re not getting any better performance out of them than the Bluetooth hardware built into the laptop, you might as well skip it.
Larger Devices
A more stable device is the Sena UD-100 which is a great USB device.
 Figure 3. Sena UD100 with included stubby antenna.
Figure 3. Sena UD100 with included stubby antenna.
While it comes with a small antenna, opting for some of the accessories like a dipole and a patch antenna can greatly extend the range of the device - for example, the patch antenna can increase the range up to a kilometer. Again, pay attention to expected drivers on Windows, and on Linux there should be no issue.
 Figure 4. This dipole antenna on the UD100 gives it a range of about half a kilometer (line of sight).
Figure 4. This dipole antenna on the UD100 gives it a range of about half a kilometer (line of sight).
The big pluses with this setup is that even the larger antenna (when detached) fits neatly in a bag and substantially increases the range.The Sena UD100 is a solid USB Bluetooth device that works way better than the built-in hardware. For both scanning and probing, this is a rock star. However, the biggest minus is that it is hardly stealthy. Expect the possibility of being approached at a coffee shop by curious “normals” wanting to know what it is (a good diversion answer is “wireless broken, temporary fix until I can get it to the shop”).
Ubertooth
Entire presentations have been done around Ubertooth, and while it has its strengths, it also has limitations. When it works, it works decently and will help get you data that is generally fairly hard to get otherwise. But getting to that point is rather difficult. Expect dropped packets and a lot of restarts of whatever Bluetooth activity you are trying to capture, because getting a complete picture of what is happening Bluetooth-wise will take some patience - especially if you try sniffing.
As we talked about earlier, Bluetooth operates by hopping through frequencies within a specific range, or spectrum. Ubertooth is being stepped through this “chasing” in the spectrum via software, and due to various environmental factors and clocks not staying perfectly in sync, packets can get dropped and even part or an entire exchange can happen that the Ubertooth completely misses.
Being that it is programmable is definitely a plus, and all of the software utilities - including firmware - are open-source. You can hook up a more powerful dipole antenna and get better range out of it in a field setting, but frankly, the Ubertooth performs best in a controlled lab environment.
Nordic Semiconductor
The Nordic Semiconductor nRF51-DK device is a pretty good Bluetooth transmitter and receiver, with the sniffing abilities working better than expected. Like the Ubertooth, it is programmable, but the out-of-the-box firmware is fine for most quick hacker work, including sniffing.
The range is limited, but the quality is high. Nordic Semiconductor supplies a lot of the chips and hardware solutions in IoT, so they tend to make inexpensive hardware to help developers test their creations.
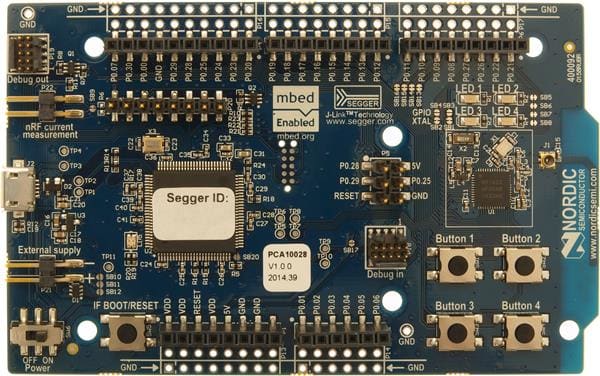 Figure 5. The Nordic Semiconductor nRF51-DK. This thing was made for serious developers and hackers alike.
Figure 5. The Nordic Semiconductor nRF51-DK. This thing was made for serious developers and hackers alike.
While the Ubertooth might have a slight advantage as far as distance goes, this is a great USB device for the lab. Due to the amount of designers and developers building IoT devices and writing IoT software for the various chipsets that Nordic Semiconductor makes, the community support for this device is rapidly growing. Expect this (and the newer model as of this writing, the nRF52-DK) to become the hacker’s favorite choice due to the wide open platform.
High-End Hardware
We don’t recommend this unless you are seriously hardcore and you have a huge budget, but if you are willing to spend the cash, you can get perfect Bluetooth captures. For example, the Ellisys Bluetooth Explorer is excellent, but retails for $17,500 USD. There are other companies selling high-end devices as well, but you get the idea - $17,500 is the starting point and prices go up from there.
 Figure 6. The Ellisys Bluetooth Explorer BEX400 does both Bluetooth and Wi-Fi sniffing at the same time.
Figure 6. The Ellisys Bluetooth Explorer BEX400 does both Bluetooth and Wi-Fi sniffing at the same time.
Why do these high-end tools cost so much? Because they work so well. The dongles we’ve mentioned can be used for sniffing, but they are basically chasing the Bluetooth session as it signal hops within the Bluetooth spectrum.
The high-end machines work differently, by simply grabbing the entire Bluetooth spectrum at once, capturing everything. Specialized software is used to help control the device and read the captured data, and typically only runs on Windows. These devices are built for lab work, but one could easily add beefier antennas, and, as long as they can meet the power requirements, this could be considered an excellent field device as well (some high-end models are even marketed that way - built for both lab and field).
Software Tools
All About The Command Line
For the Linux hacker, it is all about the command line interface (CLI). There are plenty of CLI tools for Bluetooth and many of them provide useful information, although not all of them provide output in any consistent manner.
This usually isn’t a problem when you are exploring and poking at a single device, but if you’re trying to look at a number of devices all at once (such as scanning a lot of devices while in a coffee shop), then you will have to come up with some scripting and parsing of the output to bring order to the different output formats.
Here are a number of tools commonly used by researchers (there are others, this is a sampling of the more popular ones used in Labs, check their main pages or run them with the -? or --help options for all of the functions).
hcitool - This utility can be used for command-line scanning and obtaining the ever-important MAC address when connecting with other tools.
gatttool - Included with the Bluez library, this is a great tool for honing in on specific values of a General Attribute, or GATT characteristic as defined in the Bluetooth specification.
ubertooth-btle - Included with the Ubertooth software; out of all of the Bluetooth tools, this one will be used quite a lot. While hopping and chasing through the Bluetooth spectrum, you’ll occasionally get a complete chunk of Bluetooth traffic while sniffing with this utility. Don’t let the BTLE part of this fool you - all pairing takes place in Bluetooth 4.x in the low energy realm, so if nothing else, this is a great way to get a sniffer trace of the pairing process. Just be prepared for multiple tries and some patience, and when completed, you will have a nice pcap-formatted output file to analyze.
Mobile Apps on Phones
While doing field work, you sometimes wonder if you should even bother getting out your laptop and setting up your dongles. Sometimes it helps to have a quick way to look at the traffic, and it is even better if it returns useful information - saving you time with what to focus on once you get the laptop out.
There are a number of free applications for your phone that will help with this. Some of the free apps have mixed results, but a basic guideline for choosing one is to select them by the developer.
There are a number of companies that sell tools for building various applications or IoT devices (or both) that write decent free Bluetooth apps for testing from your phone. These are usually fairly high quality because they are intended to complement your development process while using their purchased products.
A couple of decent ones that work good for security researchers are Punch Through’s Light Blue Explorer and Nordic Semiconductor’s nRF Connect.
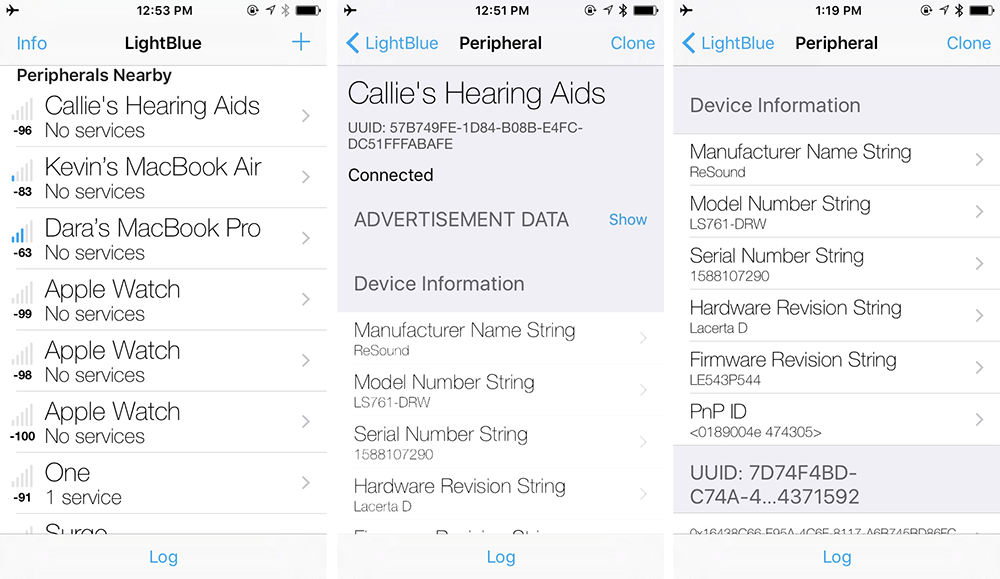 Figure 7. Punch Through’s LightBlue Explorer in action. From the above, you can see it is useful in finding unusual items. This was captured mid-flight during a business trip.
Figure 7. Punch Through’s LightBlue Explorer in action. From the above, you can see it is useful in finding unusual items. This was captured mid-flight during a business trip.
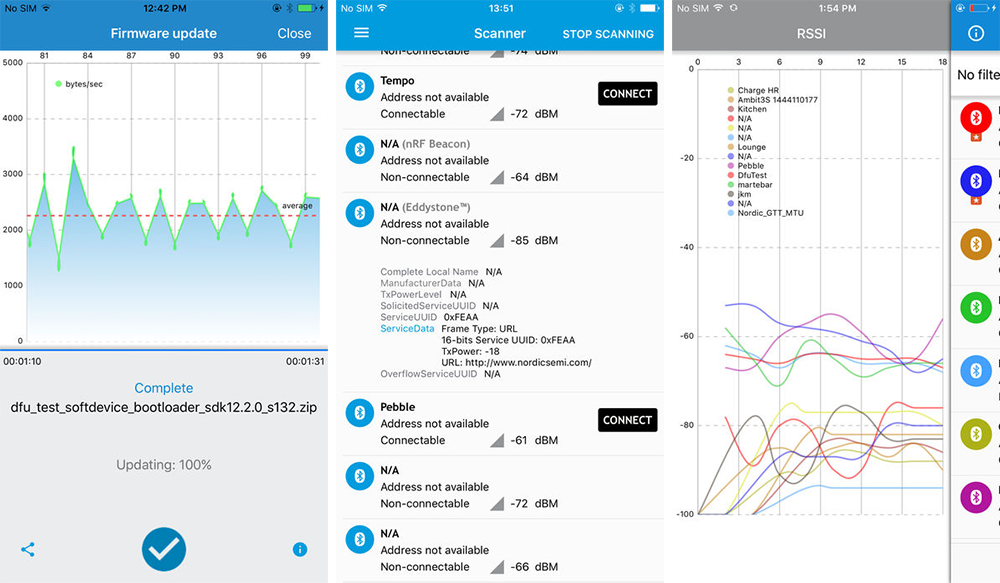 Figure 8. Nordic Semiconductor’s nRF Connect. Excellent app with decent logging capabilities.
Figure 8. Nordic Semiconductor’s nRF Connect. Excellent app with decent logging capabilities.
Using Wireshark
Most of the hardware and even some of the software comes with Wireshark plugins compile and install all of them. While there are too many to name and plan for, there are some general rules to keep in mind.
Read the documentation, but note the date. Many of the tools have detailed instructions and requirements regarding which version of Wireshark source code you need to compile the plugin, and odds are you’re running a much newer version of Wireshark. If the instructions are old and refer to an old version of Wireshark, it is possible that the plugin comes included with the newer version of Wireshark. Most plugins will compile without incident with a newer version of Wireshark. In fact, most will compile with the Wireshark development package for your Linux version, for example, wireshark-dev on Ubuntu.
The purpose of the plugins is simply to interpret the raw Bluetooth packets inside the Wireshark app into something a little more readable, and since there are multiple protocols involved with Bluetooth, it helps to make some sense out of what is going on.
There are often a couple of different ways to sniff Bluetooth - directly within Wireshark and with one of the command line tools itself. For example, Ubertooth includes the aforementioned ubertooth-btle, which allows capturing of Bluetooth traffic and saving the data in pcap format that Wireshark can read and interpret (with the appropriate plugins). But you can also plug in your Bluetooth USB dongles and sniff from within Wireshark itself. And you can use more than one Bluetooth source during sniffing within Wireshark.
For example, one can sniff using the laptop’s built-in Bluetooth capabilities; use one USB port with a dongle to perform actions with one CLI tool; and use a second USB port with a second dongle to perform another action - you can sniff from all three at once. It sounds overly complicated, but it isn’t. If you are using one dongle to probe a device and another trying to flood it at the same time, you can see the results from both in the same sniffer session. And it helps when testing how one dongle or CLI performs against the other.
So What’s The Point?
The checklist for examining Bluetooth’s attack surface involves determining what version of Bluetooth has been implemented, if the implementation is susceptible to such things as denial of service, etc.
This also involves simply documenting what the device does during various stages. For example, can more than one device pair to it? Does it begin advertising itself immediately after applying power for the first time, or do you have to perform an action (such as a button press) before it will allow pairing? Does it cycle through periods of advertising versus not advertising, perhaps in an effort to conserve battery power? But even more importantly, seeing how much information can be read remotely to fingerprint or otherwise determine information about the device - particularly as the state of the device changes. And this gets into the second area.
Things such as the name of the device or a model number can come in handy. Often when fingerprinting a device, you find information that will assist your IoT investigation in other areas - such as Bluetooth chipset and perhaps firmware versions associated with that chipset.
Being able to remotely determine the firmware version down to the exact build version can be a massive timesaver - particularly if you are able to find firmware versions online. If you’re aware of a build version that contains a certain flaw but is only available on an earlier version, you can eliminate that flaw from your testing phase, saving time.
thegnome@fang:~$ hcitool -i hci1 leinfo 00:07:80:CF:76:BC
Requesting information ...
Handle: 75 (0x004b)
LMP Version: 4.0 (0x6) LMP Subversion: 0x3
Manufacturer: Bluegiga (71)
Features: 0x01 0x00 0x00 0x00 0x00 0x00 0x00 0x00
thegnome@fang:~$
With a little Googling, determining the Bluegiga chipset and the build version of 71 helped determine the exact firmware version from 2013. Even poking around with freeware apps on a phone can reveal interesting info:
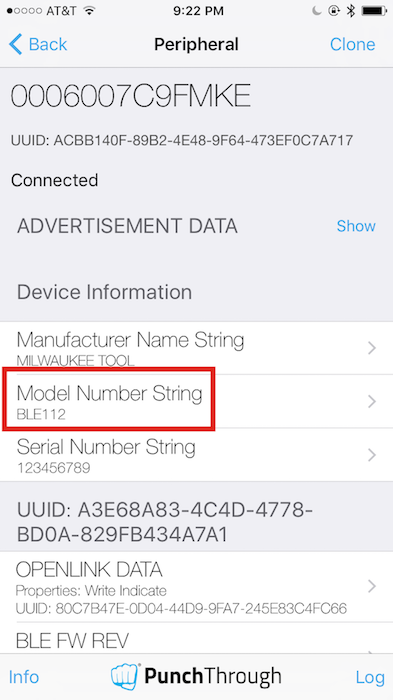 Figure 9. Scanning and finding a device’s model number string in plain English, instead of ascii hex.
Figure 9. Scanning and finding a device’s model number string in plain English, instead of ascii hex.
In the above example, the model number string of BLE112 coupled with the hcitool output with Bluegiga and the build version helped confirm the exact firmware. For the record, using the command line tool gatttool one could also determine the exact same information, although not presented nearly as cleanly.
root@plague:~# gatttool -i hci1 -I
[ ][LE]> connect 00:07:80:cf:76:bc
Attempting to connect to 00:07:80:cf:76:bc
Connection successful
[00:07:80:cf:76:bc][LE]> characteristics
handle: 0x0002, char properties: 0x0a, char value handle: 0x0003, uuid: 00002a00-0000-1000-8000-00805f9b34fb
handle: 0x0004, char properties: 0x02, char value handle: 0x0005, uuid: 00002a01-0000-1000-8000-00805f9b34fb
handle: 0x0007, char properties: 0x02, char value handle: 0x0008, uuid: 00002a29-0000-1000-8000-00805f9b34fb
handle: 0x0009, char properties: 0x02, char value handle: 0x000a, uuid: 00002a24-0000-1000-8000-00805f9b34fb
handle: 0x000b, char properties: 0x02, char value handle: 0x000c, uuid: 00002a25-0000-1000-8000-00805f9b34fb
handle: 0x000e, char properties: 0x28, char value handle: 0x000f, uuid: 80c7b47e-0d04-44d9-9fa7-245e83c4fc66
handle: 0x0012, char properties: 0x2a, char value handle: 0x0013, uuid: 00002a26-0000-1000-8000-00805f9b34fb
[00:07:80:cf:76:bc][LE]> char-read-uuid 00002a24-0000-1000-8000-00805f
handle: 0x000a value: 42 4c 45 31 31 32
[00:07:80:cf:76:bc][LE]> char-read-hnd 0a
Characteristic value/descriptor: 42 4c 45 31 31 32
[00:07:80:cf:76:bc][LE]>
The steps above were as follows:
- Go into gatttool’s “interactive” mode (
gatttool -i hci1 -I). - Connect to the device via Bluetooth using the MAC address obtained from the hcitool lescan (
connect 00:07:80:cf:76:bc). - Obtain a list of the common handles with their values (
characteristics). - In this case, we’re interested in the 0x2a24 GATT characteristic, which contains the Bluetooth chipset’s model number (this line:
handle: 0x0009, char properties: 0x02, char value handle: 0x000a, uuid: 00002a24-0000-1000-8000-00805f9b34fb). - The uuid value starting with 00002a24 is the one we’re looking for, and by using either the full uuid (
char-read-uuid 00002a24-0000-1000-8000-00805f) or the char value handle (char-read-hnd 0a), we can obtain the string with the model number (42 4c 45 31 31 32, which is “BLE112” in hex, and refers to a specific Bluegiga product).
The character properties values are interesting - for example, 02 is read only (char properties: 0x02), and 0a is writable. But as you can see, after a bit of probing and poking, we’ve gained a ton of information to help us locate firmware, chipset specs, and so on.
Correlating With Source Code
Finding all of the interfaces that allow for the external writing of values is an important part of examining the attack surface, and having all of the UUID values are great for when it comes to grepping through decompiled code. This allows you to potentially map values that are inputted into the IoT device and see how these values are processed by, for example, the accompanied app on the phone.
If you’ve managed to obtain firmware for the IoT device and decompiled it, you have an idea about what interfaces you can probe with arbitrary data, or at least which ones might look the most promising.
Not Exactly Perfect
Bluetooth can be imperfect, and it helps to run tests several times. For example, look at the results against a device, ran within a couple of minutes of each other:
thegnome@claw:~$ hcitool -i hci1 leinfo 44:fe:d3:98:29:7e
Requesting information ...
Handle: 3585 (0x0e01)
Features: 0x00 0x00 0x00 0x00 0x00 0x00 0x00 0x00
thegnome@claw:~$ hcitool -i hci1 leinfo 44:fe:d3:98:29:7e
Requesting information ...
Handle: 3585 (0x0e01)
LMP Version: 4.1 (0x7) LMP Subversion: 0x64
Manufacturer: Nordic Semiconductor ASA (89)
Features: 0x01 0x00 0x00 0x00 0x00 0x00 0x00 0x00
The first one did not receive a complete answer, while the second one did. This is why we recommend multiple passes of a test.
Summary
We hope that this information might provide a bit more direction when it comes to poking around with Bluetooth devices. Some of the areas might seem complex, particularly when dealing with multiple ways to provide input into an IoT device and trying to layer them when formulating attacks. But by using various devices with different antennas and repeating tests when they seem to fail for no reason, one can shorten research time and find actual flaws a bit quicker.
Using a System76 running Linux, a Sena UD100 with a larger dipole antenna, the Nordic Semiconductor nRF51-DK (or the new nRF52-DK), various Linux tools, and the Linux version of nRF Connect for Desktop is solid for covering most field and lab work. Coupled with some apps on the phone such as nRF Connect for either iOS or Android, and you have a quick way to check if it is worth getting out that laptop while out in the field - plus you have another source of information. But if you can use anything additional, such as more antenna choices or an Ubertooth - go for it.
Bluetooth research is like woodworking - you could do the entire project with just a hammer and nails, a chisel, sandpaper and a handsaw, but having a number of other tools like a jigsaw or an electric sander will certainly help get better results quicker.
