Researchers warn that putting a computer to sleep poses security risks. Shut it down completely, or hibernate, instead.
“Sleep mode is vulnerable mode,” said F-Secure’s principal security consultant Olle Segerdahl.
Researchers from Finland-based F-Secure found that nearly all modern computers are susceptible to “cold boot” attacks that can allow attackers to recover sensitive data from a computer’s memory. A cold boot attack refers to a side-channel attack when attackers can force a computer to reset or reboot itself, and then steal the information that was still in memory. Because the computer was forced to boot up without going through the normal shutdown (or restart) process, sensitive data such as passwords, contents of sensitive files, and encryption keys are left behind in memory for several seconds or minutes.
Sleep mode is vulnerable mode.
"It takes some extra steps compared to the classic cold boot attack, but it's effective against all the modern laptops we've tested," said Segerdahl.
F-Secure researchers were able to perform a cold boot attack on modern computers--including systems from Dell, Lenovo, and Apple--by modifying the hardware and booting up the machine off a specially-crafted USB drive containing memory-dumping software. Cold boot attacks have been known for a decade, and most computers have a security feature that overwrites contents of memory when the system boots up. F-Secure changed the hardware to disable this feature.
“It’s not exactly easy to do, but it’s not a hard enough issue to find and exploit for us to ignore the probability that some attackers have already figured this out,” said Segerdahl.
Even though attackers would need to have physical access to the system and special tools to harvest data from memory, this is a consistent and reliable way for attackers to compromise their targets. This method is not particularly exotic or unusual, even though average users will likely not have to worry about this attack. Laptops--such as those storing highly-sensitive information or belonging to high-value individuals such as government officials and executives--are vulnerable to cold boot attacks as they can be stolen.
This is a consistent and reliable way for attackers to compromise their targets.

Attackers can physically modify the hardware in order to perform a cold boot attack on nearly any laptop. (Source: F-Secure)
“It’s not exactly the kind of thing that attackers looking for easy targets will use. But it is the kind of thing that attackers looking for bigger phish, like a bank or large enterprise, will know how to use,” Segerdahl said.
While there is no permanent fix, system administrators are encouraged to configure computers to either shut down completely or hibernate when not in use, rather than entering sleep mode. Hibernate and powering off won’t stop cold boot attacks, but doing one of those things ensures no data is left lingering in memory.
“[Companies] can configure laptops so that an attacker using a cold boot attack won’t find anything to steal,” Segerdahl said.
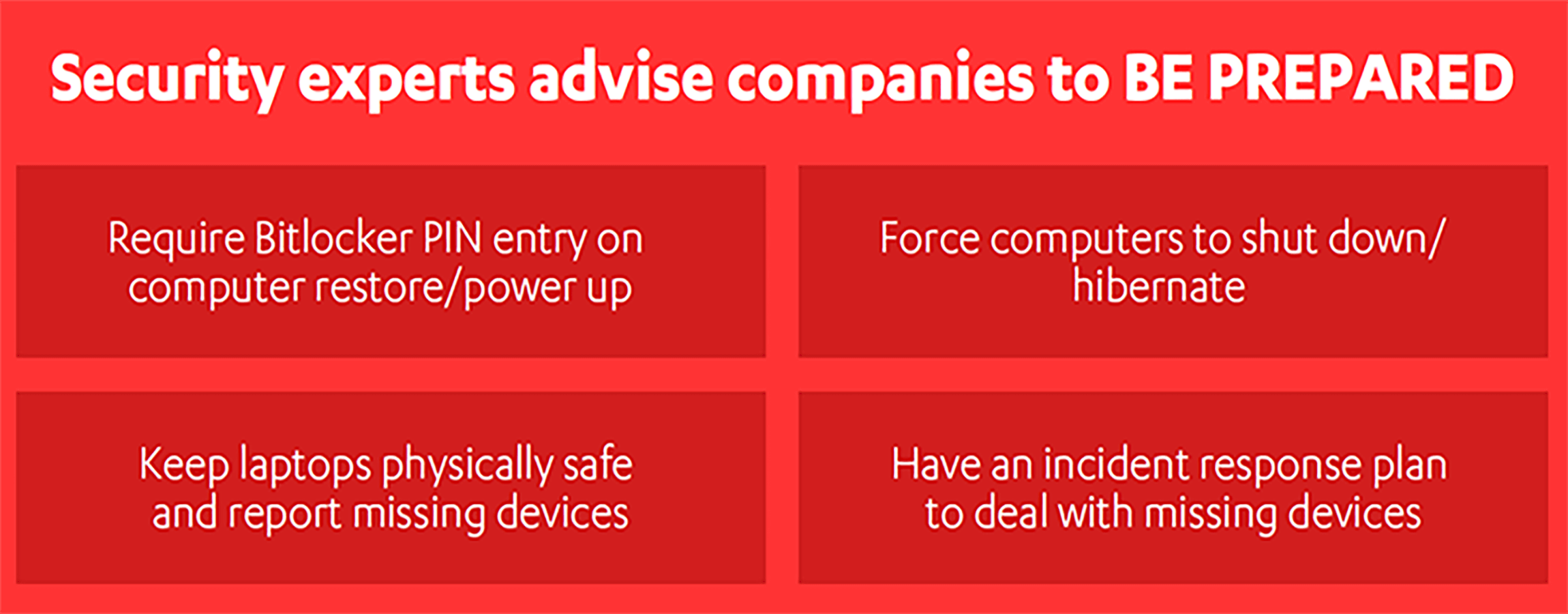
F-Secure notified Intel, Microsoft, and Apple of the issue. In response, Microsoft updated its guidance for BitLocker suggesting that Windows users should configure BitLocker to prompt for a PIN whenever the machine powers up. Encrypting the hard drive won’t stop the attack, but it limits the amount of data attackers would be able to recover.
It’s a really difficult problem to solve easily...coordinated industry response that doesn’t happen overnight.
Apple said Macs with T2 chips already have security mechanisms that should protect against cold boot attacks. Those without T2 chips should set a firmware password.
“When you think about all the different computers from all the different companies and combine that with the challenges of convincing people to update, it’s a really difficult problem to solve easily,” Segerdahl said. “It will take the kind of coordinated industry response that doesn’t happen overnight.”
The best defenses go beyond the immediate fixes. Along with making sure computers are powered off and firmware protected with a BitLocker PIN, system administrators should develop an incident response plan that handles what to do when a device is lost or stolen. IT should also take steps to physically keep the system safe as well as develop a process to report when devices are lost or stolen. Security and incident response teams should rehearse so that they know what to do when devices--inevitably!--get lost.
“Sometimes the most important way to tackle a security problem is to simply let people know it exists. A little awareness building can work wonders,” said Segerdahl.
IT departments should have a plan on how to deal with missing or stolen devices. (Source: F-Secure)

