SINGAPORE——Kaspersky Lab security researcher Fabio Assolini was on a business trip to Moscow when his phone suddenly stopped making or receiving any calls. His phone didn’t have a signal and he couldn’t connect to any local carriers. The error message on the phone wasn’t very helpful: “Can’t connect to this network right now. Try again later.”
When Assolini called the phone company to find out what had gone wrong, he learned that someone had reported the phone stolen and initiated the process to port the phone number ported to another device. That person had then requested the original phone—the one Assolini was holding—be deactivated.
“SIM swap fraud is that simple,” Assolini told attendees at the Kaspersky Security Analyst Summit.
A person trying to take control of someone else’s phone doesn’t need to resort to malware or theft. Social engineering or bribing the customer representative at the phone company to get the phone number switched to a different SIM card (the chip inside the phone that communicates with the cellular networks) is far easier. Once the process is complete—it takes less than three hours, and in practice is usually just a matter of minutes—and the SIM card is inserted into a device owned by the person, all phone calls and text messages are delivered to that phone and not the original owner’s.
Phone Number as a Key
While SIM swap fraud is not new, the number of cases have skyrocketed in recent years. The FBI warned earlier this year of an uptick in SIM-swapping fraud cases. In Brazil, criminal gangs activate phone numbers and then send messages over WhatsApp to trick victims into paying money, Assolini said.
Getting control of the phone number doesn’t sound like a lot, but it can be devastating for the victim. Many financial services organizations and online services rely on the user’s phone to confirm transactions and verify identity. For example, many banks send one-time-passwords over SMS to user phones to confirm online transactions. Many sites allow users to perform password resets with a phone call.
If the thief has the victim’s email address, then the attacker is one step closer to finding the victim’s bank accounts and other services. Thieves can reset the password on the email account, initiate account recovery on the bank account, and then use the phone number to obtain the one-time-passcode to access the account. They can drain the money out of the account, and that’s just the beginning.
The original owner never lost physical control of the phone, and didn’t even know the phone number was being moved until the process is already underway. Phone companies generally don’t ask for a lot of information to fulfill requests—a phone number and some user information (such as name and birthday) is often enough—and it isn’t hard to find those pieces of information. People list their phone numbers on social media and in email signatures, and there are many services that can be used to look up people’s numbers.
“It is easy to find your number,” Assolini said. “We don’t think of it [the phone number] as sensitive information.”
Ending SIM Swap Fraud
Mobile payments are “huge in Africa,” with mobile payments accounting “almost half of the country’s GDP” in some countries, said CERT Mozambique’s Andre Tenreiro, who presented with Assolini. Mozambique records more than half-a-million dollars of mobile payments per month. It is possible to “buy groceries and water, pay for your maid, [get] salary,” over mobile, Tenreiro said. Even pay bail to get out of jail.
Smartphones are not very widespread in Mozambique, so most services and applications rely on OTP codes sent via SMS messages, giving criminals a large victim pool to work with.
SIM swap fraud is a big problem in African countries and Mozambique was no exception. The problem was so bad that there was a perception that banks and mobile operators were colluding to steal the money from their customers, Tenreiro said.The reputation of the banks and the carriers were at stake.
Banks couldn’t switch to app-based two-factor authentication mechanisms because the bulk of the users didn’t have smartphones. So the banks and mobile operators put together an authentication scheme that made sure that the mobile device associated with the account had not recently been changed, Tenreiro said.
Under the system, banks could ask mobile operators whether a specific mobile number had been recently ported. Most banks block transactions from a mobile number that has changed SIM cards within the last 48 hours, while some allow for a 72-hour window, Tenreiro said. The idea is that most users will contact their phone operator within 48-72 hours in case of an unauthorized SIM card change. In case of a legitimate SIM change, some banks let users go to a branch office for a face-to-face verification.
This initiative “reduced SIM card fraud [in Mozambique] to nearly zero percent,” Tenreiro said.
Stronger Authentication Methods
SIM card fraud will remain a problem as long as mobile carriers keep it easy to port phone numbers. Some mobile carriers give customers the option to put a PIN on the SIM chips to make it harder for someone to swap the phone number. Mobile operators should train agents and retail staff to recognize if someone is trying to impersonate a customer.
Banks checking with the operators to very the SIM has not been swapped before authorizing transactions would also help. Banks should also switch to physical hardware tokens or authentication apps to protect accounts and use other authentication mechanisms such as biometrics. Another important step: eliminating voice password recovery—the practice of letting users reset passwords with a phone call—since it can be easily abused.
Banks should “kill off OTPs via SMS,” Assolini said. “App-based OTPs, please.”
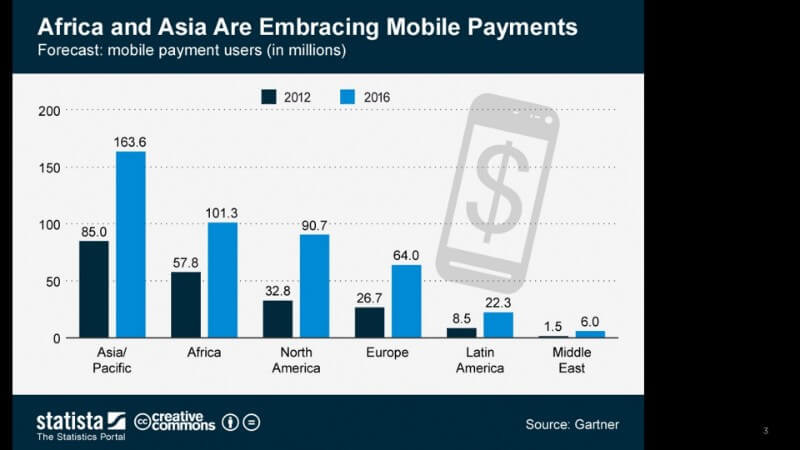
Mobile payments is growing in popularity in various parts of the world. In African countries, mobile phone-based money transfers allow users to deposit, withdraw and pay for goods and services with mobile devices. Source: Gartner, by way of Kaspersky Lab.

