Credit monitoring company Equifax has released more details about last year’s data breach—including specifics about the kind of information that was stolen—and to no one’s surprise, more consumer information had been stolen than previously reported.
“Breaches get worse within the first week,” said Jessy Irwin, head of security at Tendermint. “The first details that emerge are usually wrong, or don’t show the whole picture of what’s going on.”
In its “statement for the record” to the Securities Exchange Commission filed on May 7, the executives revealed that 146.6 million names, 146.6 million dates of births, 145.5 million Social Security numbers, 20.3 million phone numbers, 99 million addresses, 209,000 payment cards with numbers and expiration dates, 17.6 million driver’s license numbers, 1.8 million email addresses, and 97,500 Tax Identification numbers had been exposed. Equifax also provided more details about also “dispute documents” which had been part of the breach: 38,000 driver’s licenses, 12,000 Social Security and Taxpayer ID cards, 3,200 passports and passport cards, and 3,000 other documents including military and state IDs, and resident alien cards. Originally, the company had said names, Social Security numbers, and dates of births of 143 million customers in the United States had been exposed. The figure was later revised to 145.5 million people.
Equifax originally didn’t disclose the exact details of the sensitive documents because it didn’t think there was a legal obligation to do so. “With respect to the data elements of gender, phone number, and email addresses, U.S. state data breach notification laws generally do not require notification to consumers when these data elements are compromised, particularly when an email address is not stolen in combination with further credentials that would permit access,” the company wrote in the SEC letter.
This isn’t a good look for a company that has struggled with disclosing the breach or how it communicated with victims.
The investigation has revealed both a bigger number of affected victims and a broader trove of data that was stolen, which means there are more ways for attackers to use the information. Identity theft is bad enough with names, addresses, Social Security numbers, dates of birth, and driver’s license numbers on their own, but add in the sensitive documents, email addresses, and phone numbers, and now there are potentially more spear phishing and phone scams to worry about.
The company concluded that because no new customers were identified, there was no need to inform victims about other data elements that may have been exposed. That means victims don’t know the extent of their exposure or what steps to take to protect themselves.
“Six to twelve months later, there’s an update that is just far enough away from the initial announcement that it doesn’t fully reawaken customer ire,” Irwin said. “It almost always looks like companies are withholding information when the number of affected people doubles right outside of that window where the breach is front-page tech news,”
Breaches get worse within the first week.
The Equifax breach isn’t the only incident where later reports revealed more victims. Target initially said payment data was stolen from 40 million customers, but said an additional 70 million people may have also been affected. Yahoo initially had said its 2013 breach affected 1 billion accounts, and then later said all 3 billion user accounts had been compromised. It took Anthem just 20 days to discover that 78.8 million people were affected in its 2015 breach, much higher than the initial 37.5 million records it had reported.
Looking at the minimum actions required under law and regulations sets a very low bar of expectations. Organizations don't do more than they need to, but that just re-victimizes the individuals. The fact that Twitter didn't have to disclose what happened with user passwords but did so anyway is a good thing. Organizations should be disclosing because it the right thing to do, and the expectation should be that they do the right thing even when there is nothing forcing them to do so.
“It almost seems as if this pattern of behavior is a way to exploit breach fatigue and inattention to security issues, and that’s not good for anyone,” Irwin said.
Part of the reason the numbers get revised it because it takes a while for investigators to get a clear idea of the breach and to understand all the affected systems. Equifax said it found more information about the breach after it had standardized data elements and mapped the database fields across multiple impacted systems to “determine the impacted customers and Equifax’s notification obligations.”
This is why organizations need to be very careful about how they communicate about the breach right from day one. When a breach is discovered is not the time to figure out who will be in charge of deciding what to tell the victims, regulators, and the press, and how that will be handled. Incident response plans need to cover how the organization will communicate internally and externally.
"The right timing on when and what you communicate will make or break your response," said Jen Ellis, vice-president of community and public affairs at Rapid7.
Ellis recommends not giving into internal or external pressures to communicate details too early. If it's too soon to say how many victims have been impacted, or if it's not clear what systems have been breached, give a general statement that more information will be shared when it is possible to do so, will be a better response. Burying the head in the sand and not responding to queries at all will harm customer confidence and investor trust. Companies rush to get a statement out before they know the facts, or release misinformation, confusing advice, and inconsistencies. It's much harder to convince everyone that everything possible is being done, or that the situation is being handled, if numbers keep getting revised or information keeps changing.
It isn't evasion if the communications is clear that there isn't a lot of detials because the investigation is still ongoing. Try to answer questions that can be answered, and make sure everyone on the team is aware of what information is ready to be distributed and what will have to wait.
In many cases, the organization "will scramble to handle communications through their standard channels and personnel, who likely will not have a security background and will not be familiar with the terrain they find themselves in," Ellis said. "In this environment, it's easy to make a wrong move."
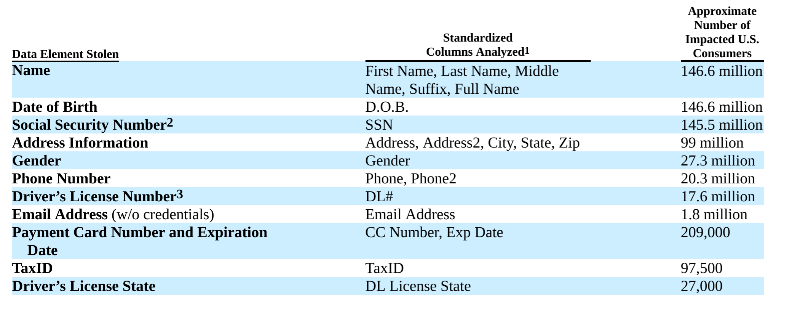
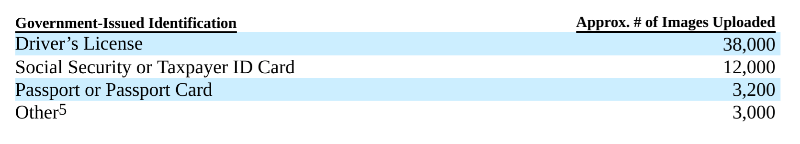
Data tables from Equifax's May 7 letter to the Securities Exchange Commission with details on what was exposed during the data breach.
