Recently, phishing attacks against Gmail users, a major U.S. financial services provider, and Android app users have revealed unique ways to deliver malware and steal login credentials.
Gmail Phishing
The latest highly-effective attacks include specially crafted URLs to trick users into typing in their Gmail credentials on a spoofed site.
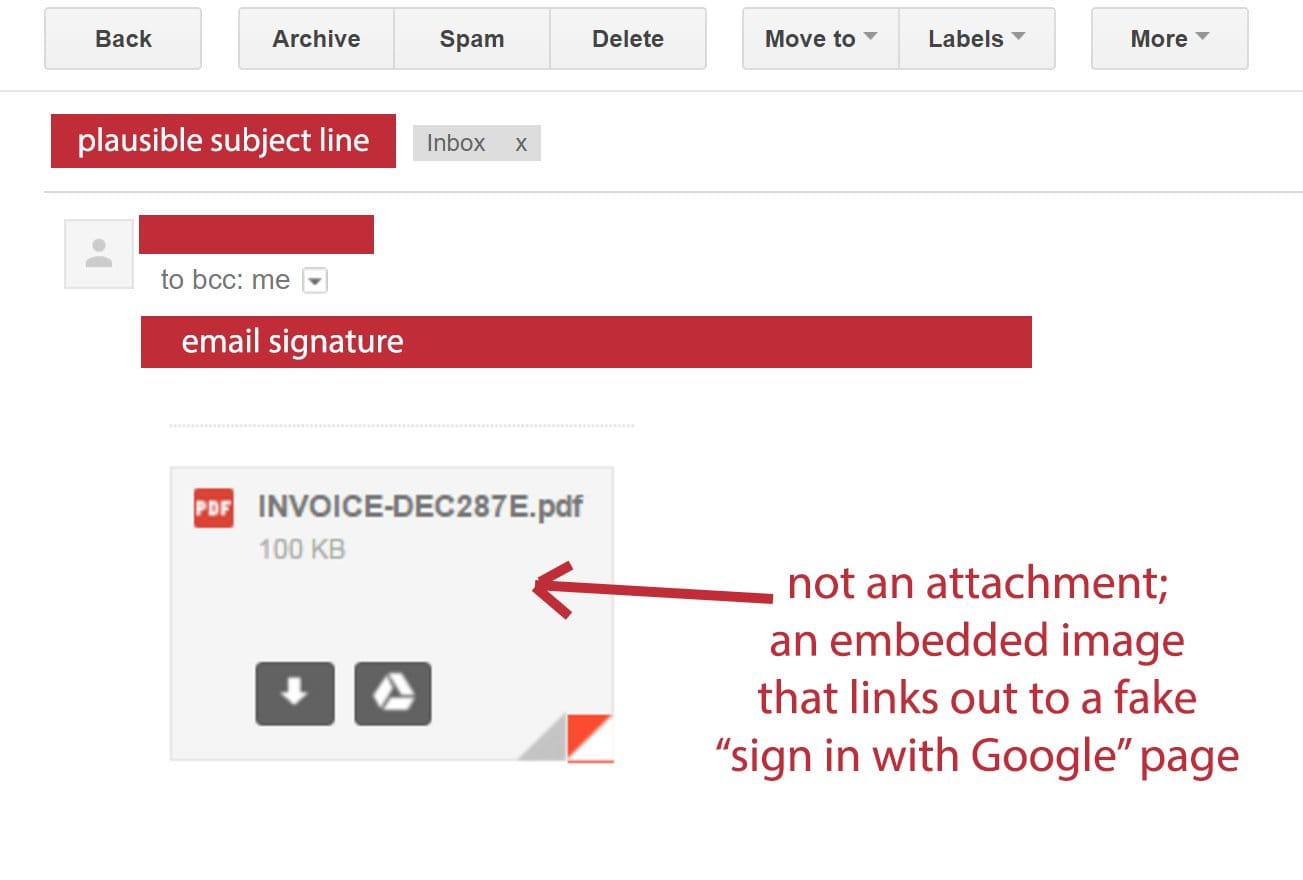
The phishing emails contain a PDF document that appears to be an attachment, but is actually an embedded image - once a user clicks on it, they’re directed to a very convincing yet fake Gmail login page, according to SecurityWeek.com. An example can be seen below, as posted by user @tomscott to Twitter and reported by Fortune.com:
The URL of the fake Gmail login page reads “data:text/html,https://accounts/google.com” plus a longer string of text that is hidden by extra whitespace. According to the researchers at Wordfence, this phishing technique uses data URI to embed a complete file in the browser location bar. When you click on the embedded image, a script serves up a file designed to look like a Gmail login page, but really works to steal your login credentials.
There have been reports of users getting compromised almost immediately after entering their credentials. Attackers are logging into their accounts and accessing their contact lists in order to find new victims, sending them emails from the compromised user.
Google has released a statement about the attacks:
"We’re aware of this issue and continue to strengthen our defenses against it. We help protect users from phishing attacks in a variety of ways, including: machine learning based detection of phishing messages, Safe Browsing warnings that notify users of dangerous links in emails and browsers, preventing suspicious account sign-ins, and more. Users can also activate two-step verification for additional account protection."
Microsoft Word Phishing
Another set of phishing emails were sent to a major U.S. financial services and insurance provider. These emails contained a Microsoft Word attachment designed to deliver a malicious payload that installed a keylogger on the user’s machine.
Keyloggers collect information that the user types, including passwords and personal information, sending it to the attacker’s email.
What’s different about this particular phishing email is it uses an embedded object in the form of a Visual Basic Script (VBS) that can be opened and executed from within the Word file, according to ZDNet.com.
The Word file prompted users to click on an image in order to install Microsoft Silverlight to view the document content. Other malicious Word attachments usually ask the user to enable macros to view content, which allows them to evade detection as they download malware on their machine.
Android App Phishing
Meanwhile, a number of infected Android Apps in the Google Play Store were reportedly stealing Instagram users’ passwords, according to Softpedia.com. These free apps were advertised as a way to increase their number of followers, get Instagram analytics or automate posting, and they prompted users to type in their Instagram login credentials after they were installed.
The apps have been removed from the Google Play Store, and they are flagged as malicious by antivirus solutions for Android devices. However, if you have downloaded or shared your credentials, it’s a good idea to change your password now.
Security Tips to Protect Against Phishing
Phishing emails may be relentless, but they don’t have to be successful. Keep your defenses up by doing the following:
Enable two-factor authentication on every login. Also known as multi-factor authentication, you can effectively protect access to your Gmail and other applications with a smartphone app that sends you a notification on your phone to verify your identity. That way, even if online criminals manage to steal your username and password, they still can’t log into your accounts without physical possession of your mobile device.
Assess your risks by conducting a phishing simulation. To evaluate your company’s likelihood of getting phished successfully, use a free phishing simulator tool to send targeted emails to your own employees. Use the data to educate your users and to make security budget decisions.
Check the address bar. Don’t enter our credentials into any site with a questionable URL. In the case of the Gmail phishing attack, the “data:text/html” might have seemed innocuous enough, but most secure sites start with “https://” and display a lock icon.
In general, don’t enter your password into a page you clicked on via email, and be wary of password prompts when you’re already logged into and viewing Gmail content.
Identify and update software on your devices. Exploit kits and malware downloaders leverage out-of-date software on user devices in order to compromise them.
