The terms zero trust and BeyondCorp (Google’s implementation are getting a lot of airtime in 2018. Getting better security by leveraging a model that assumes “no trust” seems like an oxymoron. So what is a CIO or CISO to think? Is there truth to the claims or is it all propaganda?
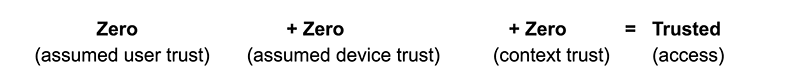
A Beyond (zero trust) model in its simplest terms means no trust is inherited based on who it is (employee, supplier, hacker), what it is (corporate vs personal device) or where it is (on a corporate network or in a coffee shop). Instead, trust is established at the time of access, each time.
Wouldn’t the world be much simpler for security professionals if trust was this easy to determine?
We wouldn’t worry about who to trust, what devices to trust, or what access attempts to trust, because it would all be plainly spelled out. Unfortunately, it’s not that simple.
Let’s start with the visibility of devices used to access applications. The Center for Internet Security publishes a list of 20 controls it suggests every organization implement, and the number one basic control in the list is maintaining an inventory and control of hardware assets. Many organizations use tools to manage their inventory of PCs, tablets and smartphones and some even scan their networks to identify devices they may not be aware of. But what about those devices employees may use when they’re away from the office to access their email in Office365? What if they’re accessing the medical record system on a personal iPad? Do you have visibility to those? Do you trust them? How can you establish an appropriate level of trust?
Answer: Assume no trust in the device.
What about the people using those devices? According to the 2018 Verizon Data Breach Investigations Report, the top threat action in confirmed data breaches is use of stolen credentials.
So how can organizations best establish trust in user access attempts, especially when the application may exist in the cloud and the access attempt may be coming from a remote location?
Answer: Assume no trust in the user.
Let’s compare the elements of a zero trust security model with your child going on a first date.
What’s one of the first things parents want to do before allowing their child to go on their first date? Meet the person they are going with. Parents want to make sure they are friendly, polite, dress appropriately, speak appropriately and are generally of good character. Does the person appear to be lying about who they are or where they are going? The parents are establishing trust in the person.
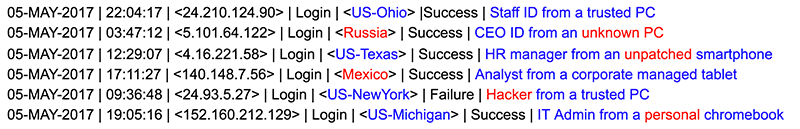
Similarly, in a zero trust model when someone attempts to access an application, the user must establish their identity by having an authorized role in the application and by passing primary authentication—typically a user ID and password. Then, the user is challenged with multi-factor authentication to make sure the credentials aren’t being used by someone who may have compromised them. These steps establish trust in the user. If the user fails authentication, the access is blocked.
Another parental verification of a date is to examine the vehicle they will be driving in. Is the car in good shape, or are there doubts it will make it the next mile? Is the car properly licensed and covered by insurance should there be an accident? At that point, parents are establishing trust in the vehicle.
In a zero trust model, when an access attempt is made, that device is inventoried and security hygiene levels are checked; without an agent, and for every device - even those the organization may not own or manage. Organizations want to answer the question of whether this device is recognized, or whether it’s one you’ve never seen before. These checks could be checks against the computer’s operating system, browser or plugins, or checks against a smartphone’s security properties such as screen lock, encryption, biometric ID or whether it’s jailbroken. Those devices the organization does own or manage can be definitively authenticated. These checks are establishing trust in the device(s) the individual is using. If the device is high risk, it is blocked.
In addition to verifying the date and their ride, parents will examine the context of the situation. Are plans to go somewhere they have never been before? Is the date planned for an unusual day or time? Is there an unusual urgency to leave? All these could be indicators that there are circumstances making this date higher risk than normal. Parents are taking in contextual awareness and establishing trust in the authenticity of the date itself.
Wouldn’t the world be much simpler for security professionals if trust was this easy to determine?
Context in a zero trust model can take several forms. Let’s say a physician is accessing a medical record system. Is that physician accessing it from the hospital, or from a remote location? Are they accessing it from a foreign country? Is this one of many access attempts from the same day, or is this the first time the system has been accessed in a very long time? Is this physician allowed to access this particular system remotely? Is he accessing from a highly unusual time? Did he just login 15 minutes ago from a location 5 hours away? All these types of context checks are establishing trust in the authenticity of the access itself. If it’s highly unusual, maybe it’s blocked.
Why should a CIO or CISO care about the zero trust security model? The CIO and CISO roles today require strong business acumen. They need to enable business to take advantage of new business models and technologies available today and into the future. How does a zero trust model enable that?
A zero trust model can be deployed to protect cloud applications, as well as internally hosted applications. So organizations have flexibility in where they want to deploy applications.
As mentioned previously, trust in the user, their device(s) and the context of the access attempt is evaluated independent of where it’s coming from. So whether a team member is accessing an application from the corporate network or whether they are sitting in a coffee shop across the world, that access can still be protected. That enables organizations to leverage mobile technologies and remote team members to gain the most value from their modern workforce.
Hopefully these examples help explain the concept of a zero trust security model, and how it can help the CIO and CISO achieve their goals.