Editor's Note: This story has been updated.
While federal government shutdown has had an immediate effect on the hundreds of thousands of employees and contractors either furloughed or forced to work without pay, IT security teams outside of the government could potentially be affected as necessary public services become unavailable.
The partial shutdown began when funding for parts of the government ran out on Dec. 22, impacting more than a third of the federal employees working at departments including State, Justice, Treasury, Transportation, Interior, Agriculture, and Homeland Security. Nearly half of the affected 800,000 workers are working without pay—such as air traffic controllers and agents at airport security checkpoints—while the rest are furloughed. Who works and who stays home depends on which jobs are considered “essential.” That means many of the federal security workforce are exempt from the shutdown, especially those specialists responsible for security operations, monitoring networks, and defending systems against attacks.
While the Justice Department’s Justice Security Center is staying open and the Treasury Department identified computer security incident response and emergency operations staff as being essential, nearly 85 percent of the National Institute of Standards and Technology staff are furloughed. The fact that so much of NIST is closed would potentially impact the upcoming release dates for security standards and guidelines the agency has been working on, including the new risk management framework, changes to the federal government’s guidelines on security controls, and requirements to access controlled by unclassified information.
Even though NIST regulates federal agencies, corporate security teams use NIST standards as a baseline for their security programs. The NIST guidelines provide enterprises with actionable security best practices as well as detailed threat-mitigation strategies. The delay in releasing these guidelines will impact security teams at organizations waiting for these publications.
Also closed: the FIPS-validation sites Cryptographic Algorithm Validation Program and Cryptographic Module Validation Program, which means products can't undergo testing during this period. CMVP certifies products used by the federal government that collect, store, transfer, share and disseminate "sensitive, but not classified" information as meeting the requirements of meeting the requirements of FIPS 140-2. CAVP is the prerequisite.
Trying to keep networks and data safe and thwarting attacks when not at full-strength is risky, especially when no one can predict how long this state of affairs will last.
“At a minimum, agencies must avoid any threat to the security, confidentiality and integrity of the agency information and information systems maintained by or on behalf of the government," the Office of Management and Budget said in a memo released back in Jan. 19, 2018. “Agencies should maintain appropriate cybersecurity functions across all agency information technology systems, including patch management and security operations center (SOC) and incident response capabilities.”
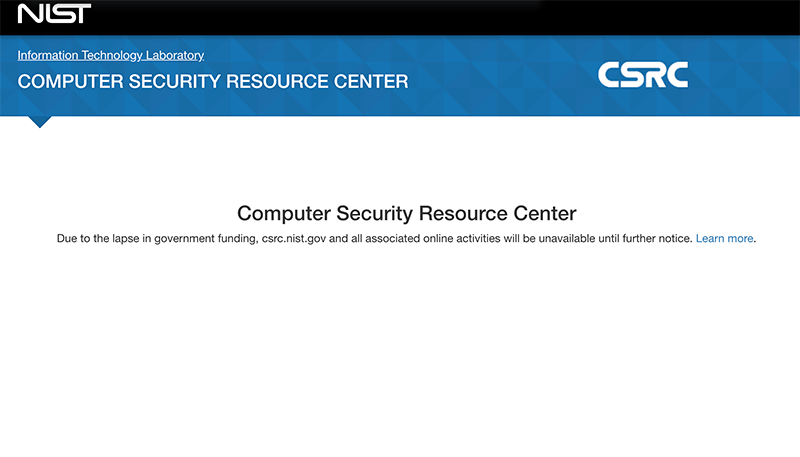
Shutdown message shown on select guidelines and publications from NIST.
Services Stay Open
Even though much of NIST’s work will be interrupted with the shutdown, several NIST services will stay open. During the shutdown period, a computer scientist and an IT specialist will maintain the National Vulnerability Database, 16 employees will manage NIST’s time servers, and an IT specialist will be at the National Cybersecurity Center of Excellence.
NVD is a repository of security checklists, software security vulnerabilities, and misconfigurations, and helps organizations understand and prioritize issues to mitigate. Outside of government, enterprises rely on the time servers to synchronize their infrastructure to have the same time so that they can look at transactions across systems, log events, and make sure tasks completed at the right time in the proper order.
“NIST time and frequency operations in Boulder, Ft. Collins, and Kauai are required to continue for reasons of national security (universal time coordination), national economy (e.g. Security Exchange Commission requirements), and national timing and synchronization infrastructure (e.g. millions of radio-controlled clocks),” said the Department of Commerce in its planning documents.
While much of the Small Business Administration will be closed, small businesses will be able to continue accessing security recommendations and guidance from the website. If small businesses have specific questions or need assistance with security matters, the National Cybersecurity and Communications Integration Center (NCCIS) service desk is open and accepting calls (as of Dec. 31).
All services of the National Technical Information Service will stay up and running.
At Reduced Capacity
It is an uncomfortable fact that the shutdown means the government’s security capabilities are reduced. The Department of Homeland Security’s newly-established Cybersecurity and Infrastructure Security Agency has 45 percent of employees furloughed. Approximately 45 percent of Homeland Security's analysis and operations team—which encompasses the Office of Intelligence and Analysis and the Office of Operations Coordination—is on furlough. I&A provides security intelligence to public and private sector partners and develops intelligence from those partners for DHS and the intelligence community.
Just because important services are available and security-related functions are up and running doesn’t mean there is nothing to worry about. The longer it takes for the government to reopen, the greater the chances that these agencies operating on short-term reserves may run out of cash on hand. At which point, they will be forced to shutter some of these services.
Security is challenging enough when fully-staffed and fully-funded. Trying to keep networks and data safe and thwarting attacks when not at full-strength is risky, especially when no one can predict how long this state of affairs will last.
Editor's Note: The original version of this story incorrectly referenced an older plan regarding the National Protection and Programs Directorate. When CISA was created in 2018, NPPD was reogranized into the new agency. The story has been updated to remove references to NPPD.
Header image credit: Photo by Marco Bianchetti on Unsplash