The four questions every compliance framework asks
I recently presented a webinar called "Compliance Made Simple with Cisco Duo for Public Sector." The audience included government IT teams, K-12 technology leaders, and law enforcement agencies.
These organizations share something in common with small and mid-size businesses: limited staff, strict requirements, and users who don't want security slowing them down.
As I prepared for that session, I realized the compliance challenges public sector teams face are nearly identical to what SMBs experience: whether you handle payment card data, work with government agencies, support healthcare patients, or simply need to satisfy your cyber insurance provider, the requirements all come down to the same four questions.
The barriers to success are the same. And the solutions that work are the same.
Ready to see how Duo simplifies compliance for your organization? Start your free trial and experience it yourself.
Every compliance framework asks the same four questions
Strip away the jargon and every compliance requirement asks:
Who is the user?
What device are they on?
What policy applies?
Can you prove it?
No matter how many pages the compliance document contains, it always comes back to these four. The rest is formatting.
When I share this with IT administrators, I see relief on their faces. Compliance feels overwhelming because the documents are written in language that looks like English but somehow isn't. Breaking it down to four questions makes the path forward clear.
Once you understand the four questions, you need controls to answer them. I organize these into three components:
Identity controls
Device controls
Access policies with audit capabilities
1. Identity controls answer "who is the user"
Compliance frameworks now require multi-factor authentication (MFA) for both privileged and non-privileged users. Static passwords alone no longer meet modern compliance standards. MFA is not optional for regular users. It is required for everyone who accesses sensitive systems.
Cisco Duo addresses identity requirements through a wide range of authentication methods.
Duo Push provides fast, familiar authentication for smartphone users, with options for number-matching and proximity-based verification.
Hardware tokens serve field workers and anyone without a smartphone.
Time-based one-time passwords (TOTP) and FIDO2/WebAuthn support offer additional options based on your security requirements against replay resistance.
See how Duo aligns with NIST 800-63-3 AAL2/AAL3 requirements for phishing-resistant authentication.
The adoption piece is also critical here. I've seen MFA rollouts fail because users fought the change. Duo succeeds because it stays out of the way. Duo Push takes seconds, and the experience feels familiar. If your MFA solution requires a 40-page deployment guide and a week of training, adoption is already in trouble.
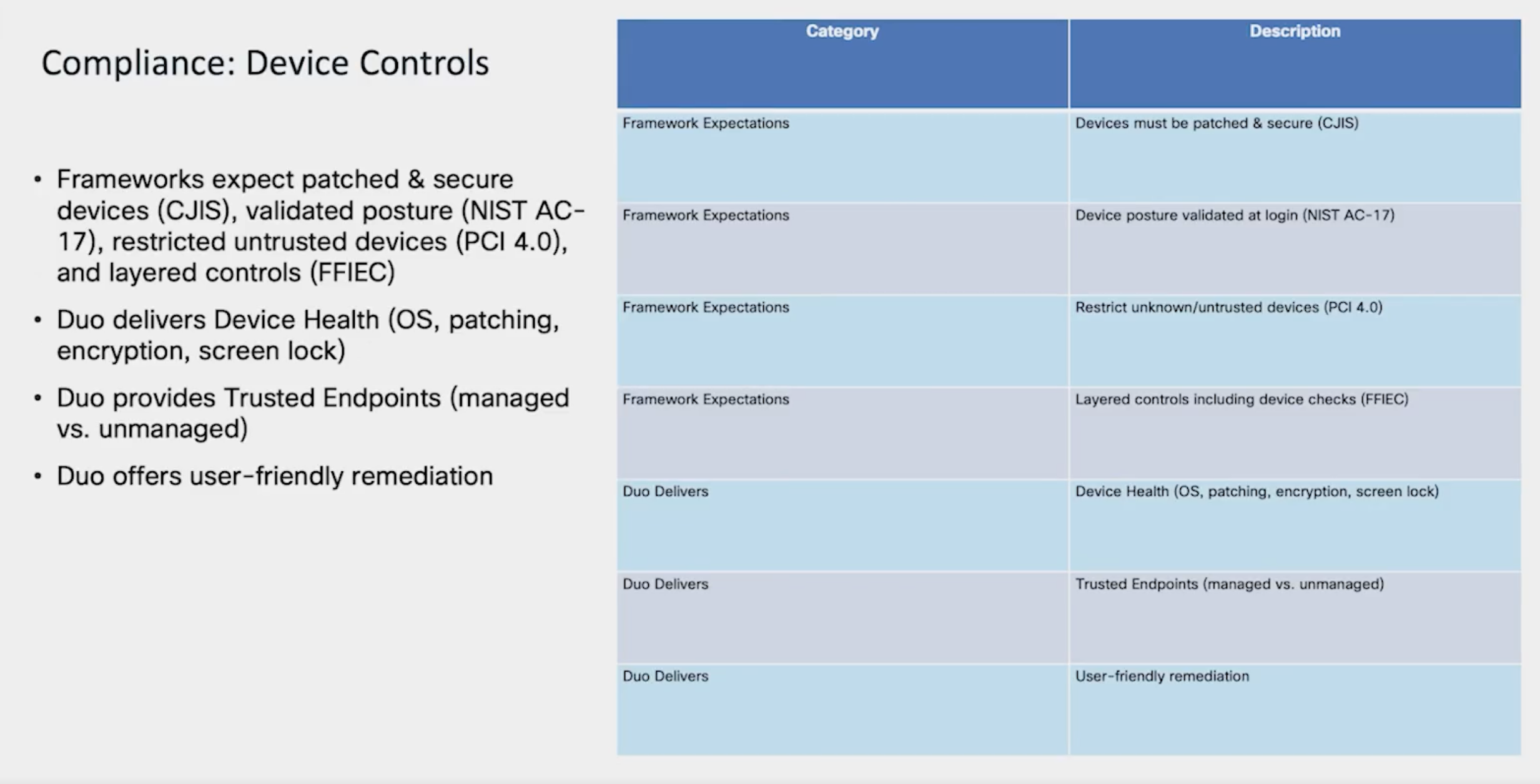
2. Device controls answer "what device are they on"
Compliance frameworks now require endpoint validation and patching verification before granting access, making device trust essential. Auditors increasingly ask about endpoint posture, and "we authenticated the user" is no longer a complete answer.
Duo Device Health checks operating system version, patching status, encryption, and screen lock settings at every login. When a device doesn't meet requirements, Duo guides users to fix the issue themselves. This "self-remediation" process means fewer help desk tickets for IT teams already stretched thin.
This also solves a common problem for organizations dealing with bring-your-own-device (BYOD) environments. You can't install mobile device management (MDM) software on personal devices, but you're still responsible when those devices access your network. Duo validates device posture without requiring MDM installation. Users keep control of their personal devices while you maintain visibility into security posture.
3. Access policies and audit controls complete the picture
Compliance frameworks don't just ask whether you authenticated someone; they ask under what conditions. This is where context-based access policies become essential.
Duo lets you apply policies based on user role, device type, location, and network. A contractor accessing sensitive data from an unmanaged device might face stricter requirements than a full-time employee on a company laptop. With Duo, you define the rules based on your risk tolerance.
The audit piece completes the picture. At some point, someone will ask: who accessed this system, from where, on what device, and under what policy? Duo logs all authentication events with this detail. During an audit, you pull the report. During a security incident, you investigate quickly instead of reconstructing events from scattered sources.
When I ask customers why they chose Duo, the answer isn't technical. They tell me their users didn't fight it, their help desk tickets went down, and their audits got easier. For a small IT team, this matters more than any feature list.
Simplify compliance for your organization
I genuinely believe Duo makes the compliance journey simpler for organizations of any size. I've seen it work for public sector teams with the strictest government requirements and the smallest staff. The same approach works for small and mid-size businesses facing similar challenges.
The frameworks all ask the same four questions. The controls break down into three manageable components. And Duo deploys in hours, not weeks.
For a deeper dive into the four questions every auditor asks, watch the full replay of my webinar, Compliance Made Simple with Cisco Duo.
Start your free trial of Cisco Duo and see how Duo helps simplify compliance for your organization.
What IT administrators ask about compliance
What compliance frameworks require multi-factor authentication?
Most major compliance frameworks now require MFA for all users, not just administrators. These include CJIS (Criminal Justice Information Services) for law enforcement, NIST (National Institute of Standards and Technology) guidelines for government contractors, CMMC (Cybersecurity Maturity Model Certification) for defense suppliers, PCI DSS 4.0 (Payment Card Industry Data Security Standard) for organizations processing credit cards, and FFIEC (Federal Financial Institutions Examination Council) guidelines for financial institutions. Many cyber insurance policies also require MFA as a condition of coverage.
How do I simplify compliance for a small IT team?
Focus on the four questions every framework asks: who is the user, what device are they on, what policy applies, and can you prove it. Choose tools that address these questions without requiring dedicated expertise to manage. Duo deploys in hours and reduces help desk tickets rather than increasing them.
What is device trust and why does it matter for compliance?
Device trust means validating that a device meets security requirements before granting access to sensitive systems. Compliance frameworks now require endpoint validation including patching status and encryption. Duo Device Health checks these factors automatically at each login without requiring MDM installation on personal devices.
What is the difference between MFA and two-factor authentication?
Two-factor authentication (2FA) requires exactly two factors to verify identity. Multi-factor authentication (MFA) requires two or more factors. In practice, the terms are often used interchangeably, though MFA can include additional factors for higher security environments.
How does Duo handle compliance logging and audit requirements?
Duo logs all authentication events including user identity, device information, location, and which policy was applied. These detailed logs help you answer auditor questions about who accessed systems and under what conditions. During security incidents, the same logs enable faster investigation and response.

