Dive deeper into multi-factor authentication
RESOURCES
Explore our library of informative assets on MFA
ARTICLE
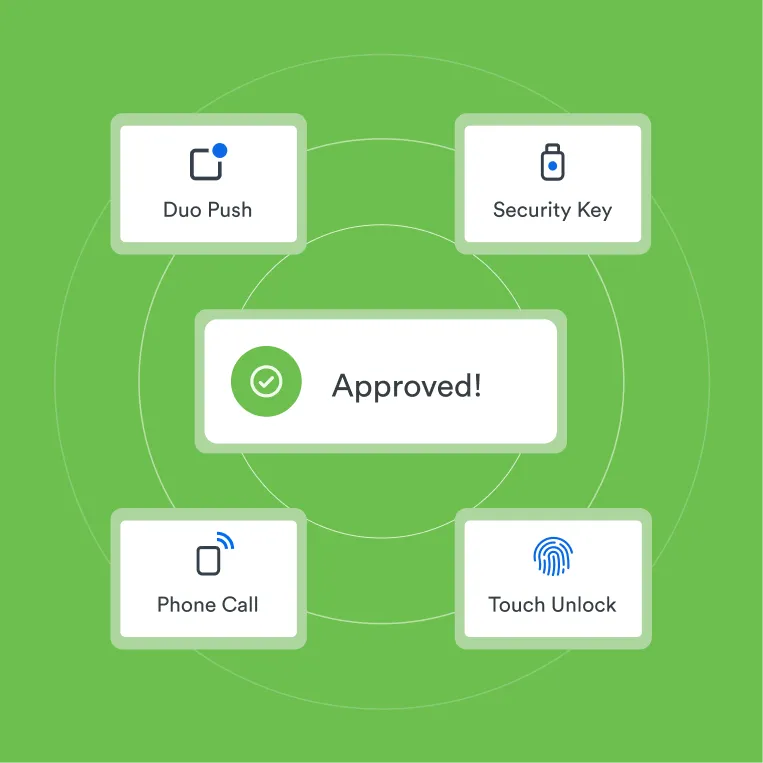
Verified Duo Push Makes MFA More Secure: A blog that introduces Duo Push and more
ARTICLE
Best Practices for Enrolling Users in MFA: A discussion of enrollment options and best security practices for Duo admins
ARTICLE
Multi-factor authentication (MFA) Fatigue: What it is and how to respond

Our deployment of MFA, with multiple authentication options, helped the city achieve a security mindset, a major culture change. The City and County of Denver rolled out MFA to over 18,000 users in less than three months with minimal impact to our IT help desk. Having a simple mobile app option is crucial to higher user adoption.
Read customer storyPaul Kresser
Chief Data Officer, City & County of Denver