Duo addresses the critical security gaps in traditional IAM
Comprehensive identity security solutions
Identity that puts security first.
Traditional IAM solutions fall short of protecting you from modern, sophisticated attacks. Discover the Duo Directory, phishing-resistant MFA and other features that attackers hate and users love.

Duo Directory
Everything you need to secure and manage identities from day one, built from the ground up to thwart identity attacks. Finally, identity that puts security first.
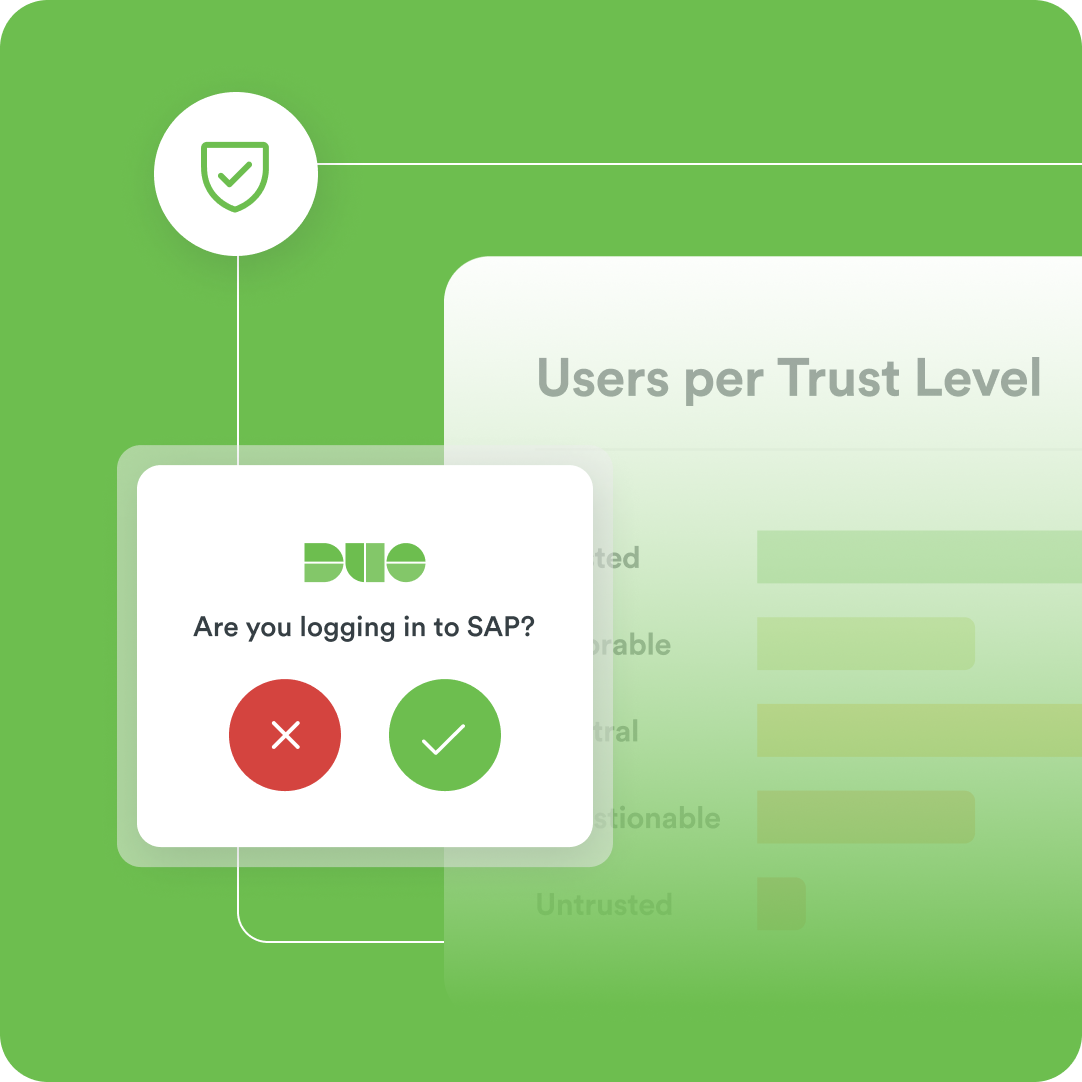
Protect access with phishing-resistant MFA
Verify users and devices behind the scene at every access attempt to stop attackers in their tracks.
Streamline logins with SSO
Enable users to securely log in to multiple applications with one set of credentials. Simplify access for your entire team.
Secure access from anywhere
Whether your team is remote, hybrid, or onsite, ensure seamless access and easy-to-implement permission controls.
Help prevent phishing attacks
Juggling passwords is not only frustrating, but it can also open the door to potential security threats. Duo's end-to-end phishing resistance ensures the highest security before and after login.

Duo Passport: authentication at warp speed
Duo Passport securely reduces frustrating extra authentications, letting your team get back to work.
Eliminate password hassle
Passwordless login lets your team sign in from any device quickly and securely, reducing friction and saving time.
Next-level insights and threat protection
Adding extra layers of security doesn’t have to mean more hassle. Duo’s flexible authentication saves your team time and boosts productivity.
Centralized visibility and control
Reduce the risk of a data breach and monitor activity across your team.
Stay ahead of threats
Detect threats early with proactive and rapid threat detection.
Proactive identity posture assessment
Evaluate, detect, and mitigate identity risks across your network.
Security in action
Get a closer look at Duo’s solution for identity security. Check out our interactive demos to explore our most common use cases and tools.
Duo MFA has been brilliant because we can integrate it with so many different packages, ADFS, Azure, and the like and also when we came to actually talking about MFA with some of partners they were already using Duo so for them to not need to have another program or application to authenticate was great.
Adrian Foo
IT Manager, Hynds Group
Identity security solutions for everyone
Teams of all sizes trust Duo to secure their data. From small businesses to government agencies, Duo delivers scalable security solutions that adapt to your needs.
SMB
Versatile solutions for agile teams. Stay ahead of evolving threats with our suite of authentication and identity security tools.
Enterprise
Protect your entire team with advanced adaptive access controls, zero-trust security, and seamless identity management across devices.
Government
Robust tools for the strictest safety standards. Ensure compliance and protect confidential data with Duo’s most advanced security tools.
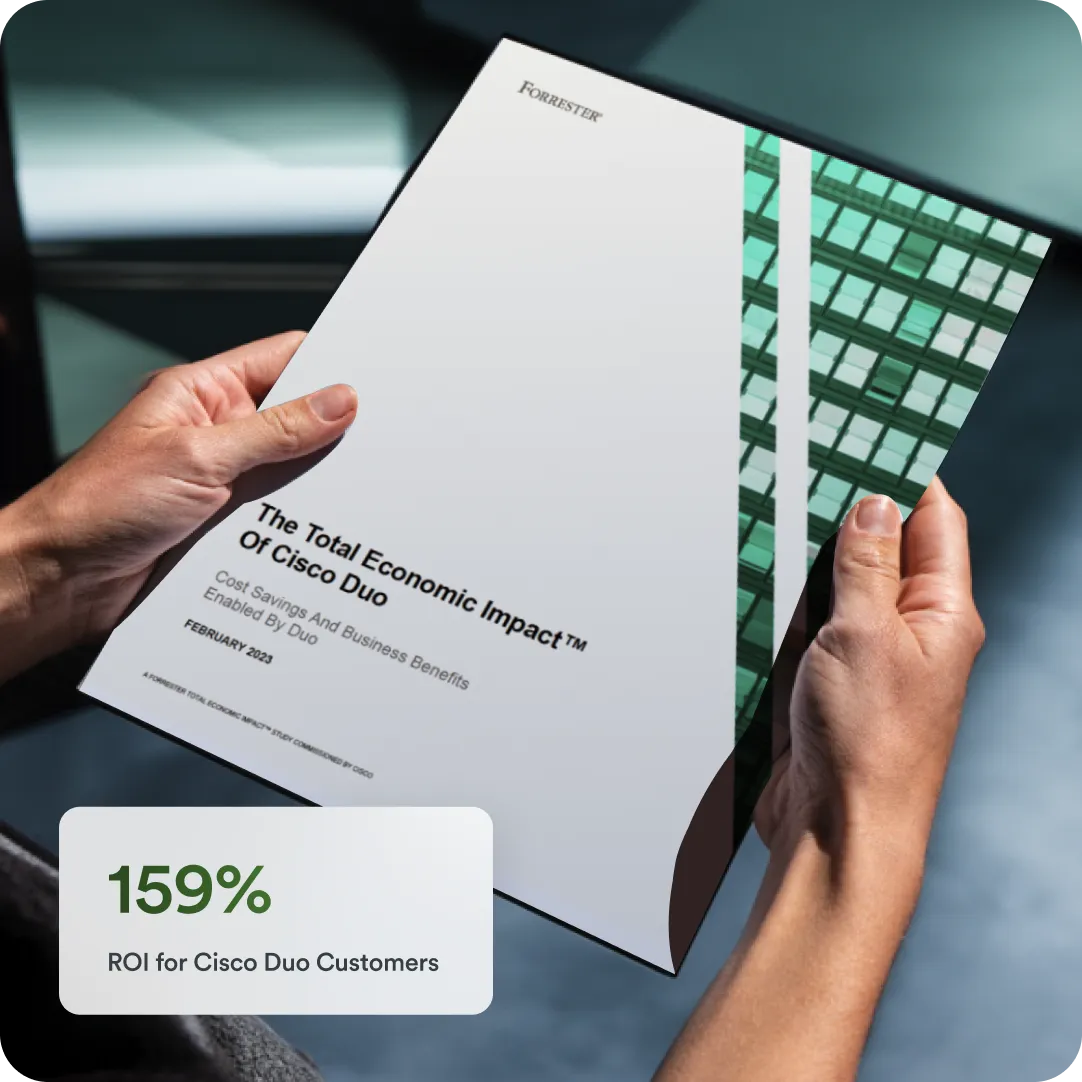
Economic Impact Study
A Forrester Consulting study found that implementing Cisco Duo resulted in time savings for end users, help desk staff, security analysts, and IT staff, as well as a reduced risk of credentials-related security breaches.
Ready to secure your organization?
See why Duo is one of the most trusted access management tools. Try it for free, explore editions, and connect with security experts to get started.
