Deploying a Duo Proof of Concept
Last updated:
Overview
We strongly suggest deploying Duo to a small subset of users before releasing it to your entire user base. Deploying a "proof-of-concept" installation using this quick-start guide takes just a few minutes, and will familiarize you with Duo application administration, as well as Duo's bulk self-enrollment tool and new user policy features. Once you are comfortable with Duo administration, you can easily expand your pilot installation to protect additional users or services.
Proof of Concept Deployment
These proof-of-concept deployment steps accomplish the following:
- You will have some proof-of-concept test users enrolled in Duo with 2FA devices.
- You will have an application configured to add Duo authentication only for the enrolled test users. The rest of your users, who have not enrolled in Duo, continue to log in without two-factor authentication.
Here's how to set up your proof-of-concept:
-
Log in to the Duo Admin Panel
-
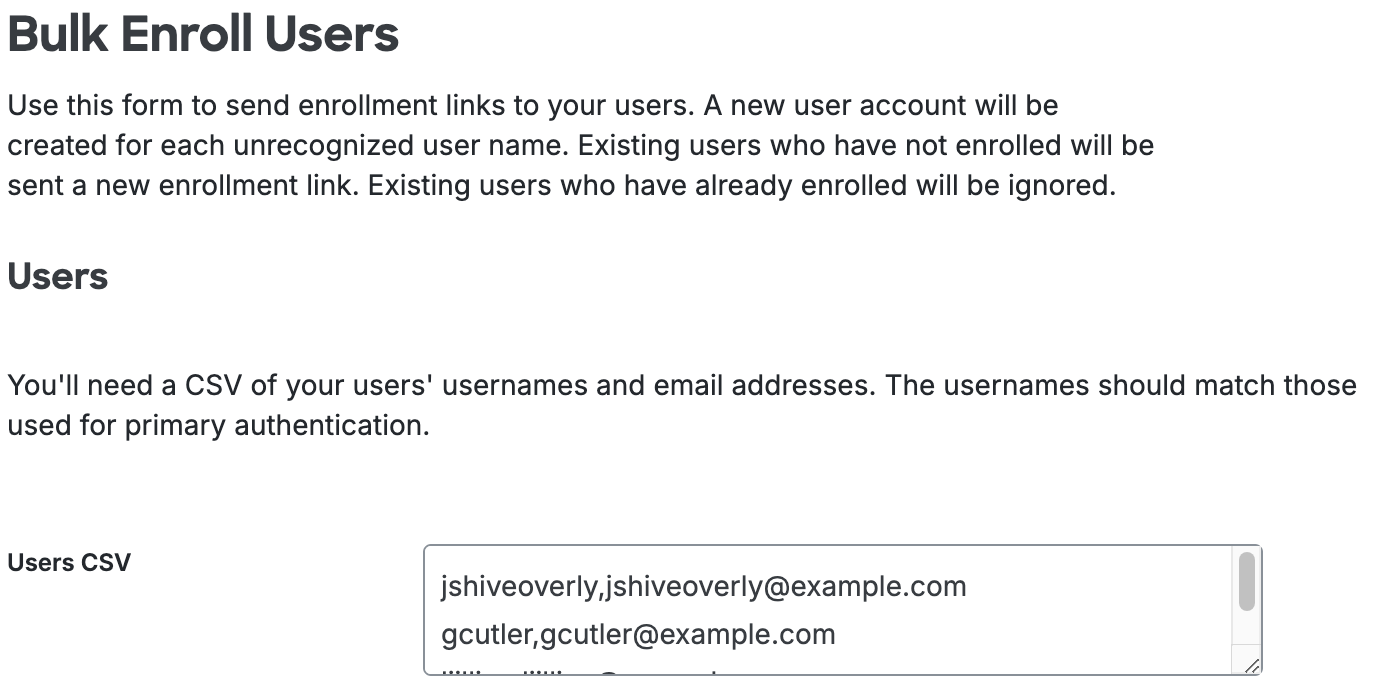
Invite the users participating in the two-factor proof of concept to enroll in Duo. To do this, navigate to Users → Bulk Enroll Users in the Duo Admin Panel.
-
On the "Bulk Enroll Users" page, enter the usernames and email addresses of the participating users. These users will receive an email informing them that their administrator has requested they enroll in Duo. That email includes an individualized link so the user can enroll immediately. If you are a Duo Essentials, Duo Advantage, or Duo Premier customer, then you can edit the text of this email and choose to include your organization's logo before you send it.
When you're ready to send the enrollment email, click the Send Enrollment Links button at the bottom of the page. See the Bulk Self-Enrollment documentation for more detailed instructions.
-
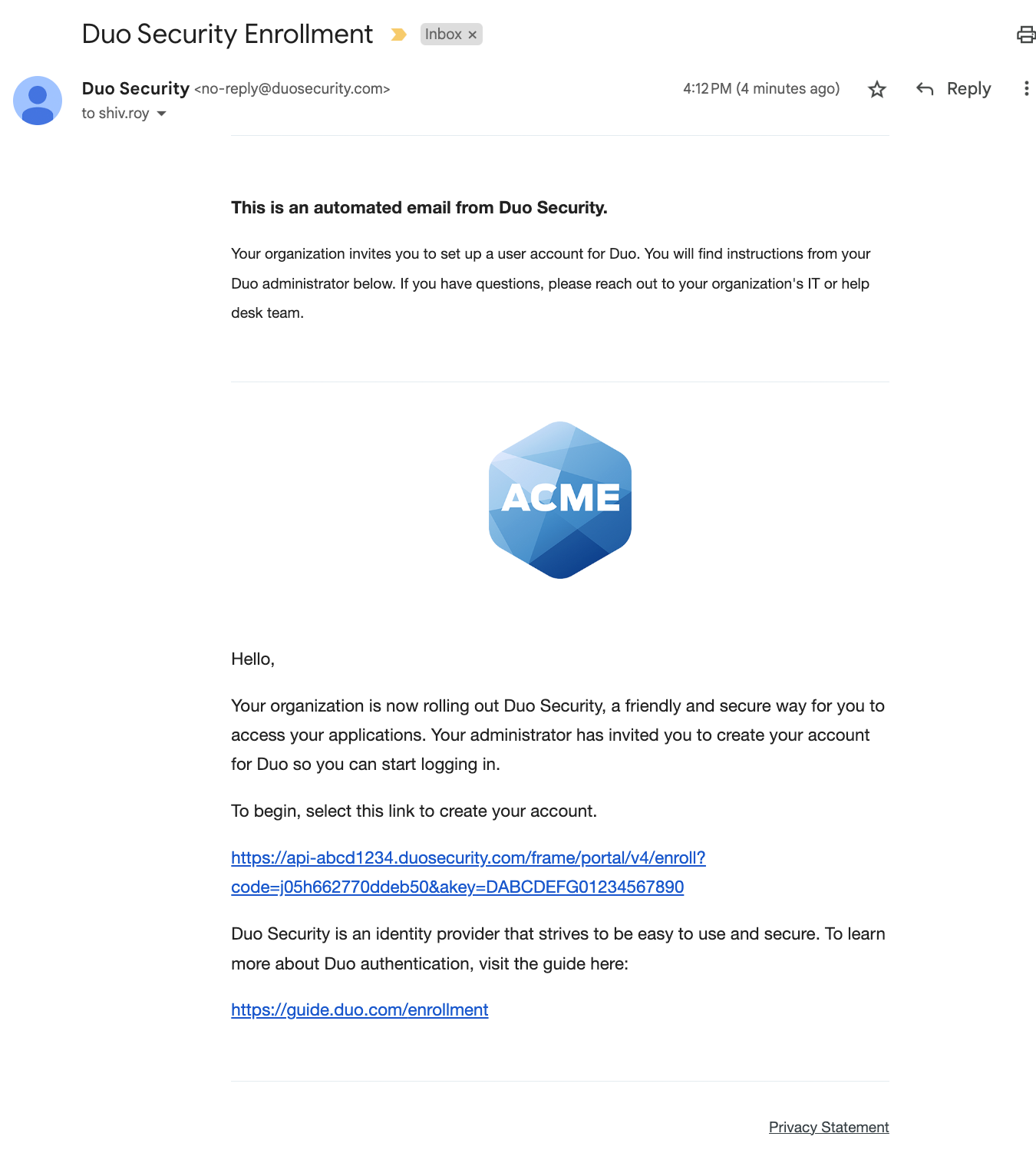
Once these users click on the link in the email message and complete registering an authentication device they'll be enrolled in Duo's service. These users will now be able to securely log in using Duo's two-factor authentication system.
-
In the Duo Admin Panel, navigate to Applications → Application Catalog.
Alternatively, you can click the Add New... button in the top right of the Admin Panel's Home page and then click Application.
-
Locate the type of application for your proof of concept in the catalog (you can filter the list by typing in a keyword), then click + Add. You'll automatically be sent to the properties page for your new application. See our Protecting Applications documentation for more details.
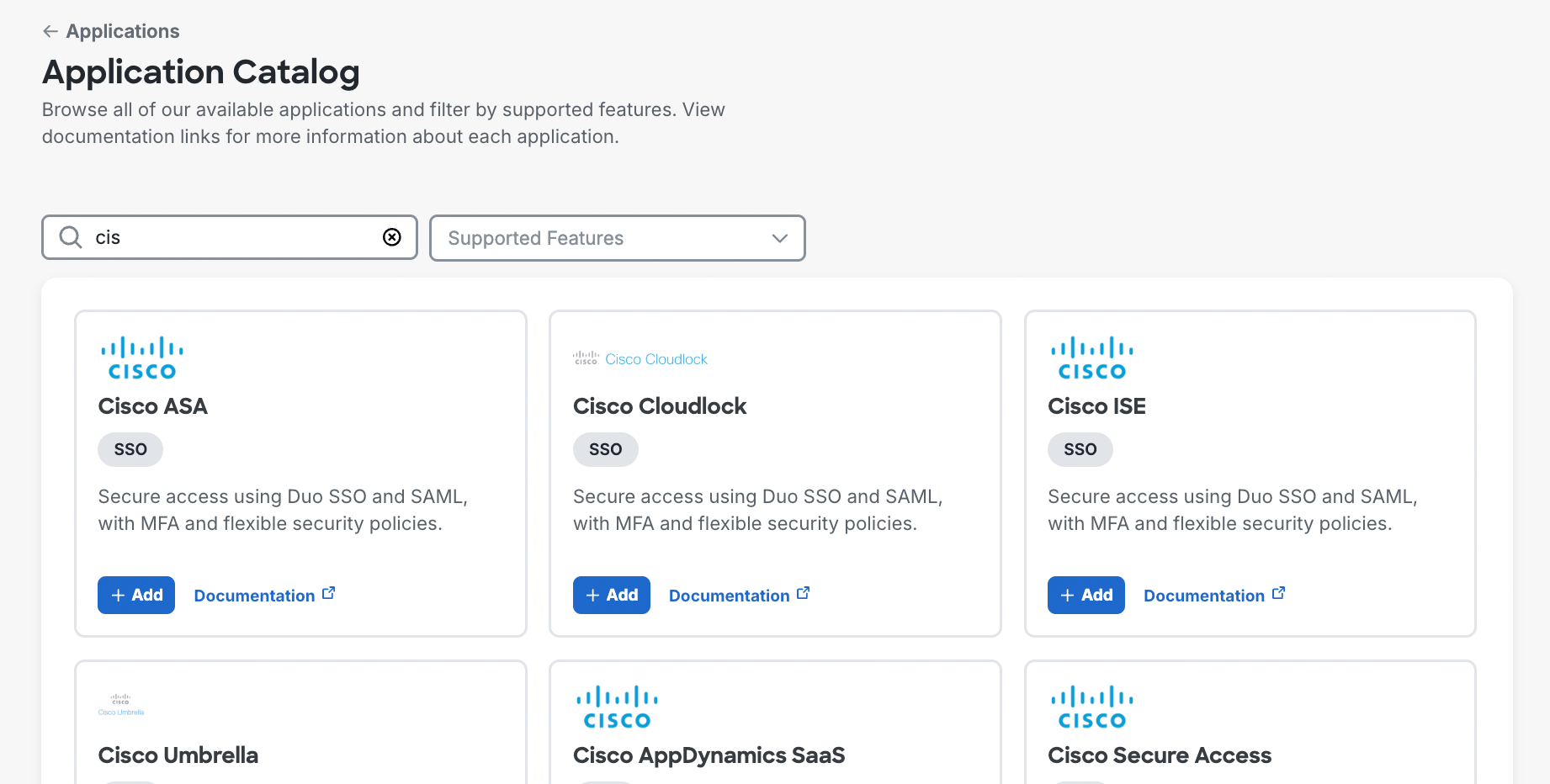
If you see a Configure SSO button for the application that you want to protect with Duo, that means it's a Duo Single Sign-On (SSO) application. You'll need to set up Duo SSO with a working authentication source before you can create the application.
-
By default, all users are asked to enroll with Duo when they log in for the first time after you protect most services or applications. You'll want to change this behavior so that users who aren't part of the proof of concept will continue to log in normally. To change the default new user policy, go to the Policies page at Policies → Policies and edit the global policy. Locate the New User Policy in the editor and select Allow access without 2FA. Click the Save Policy button.
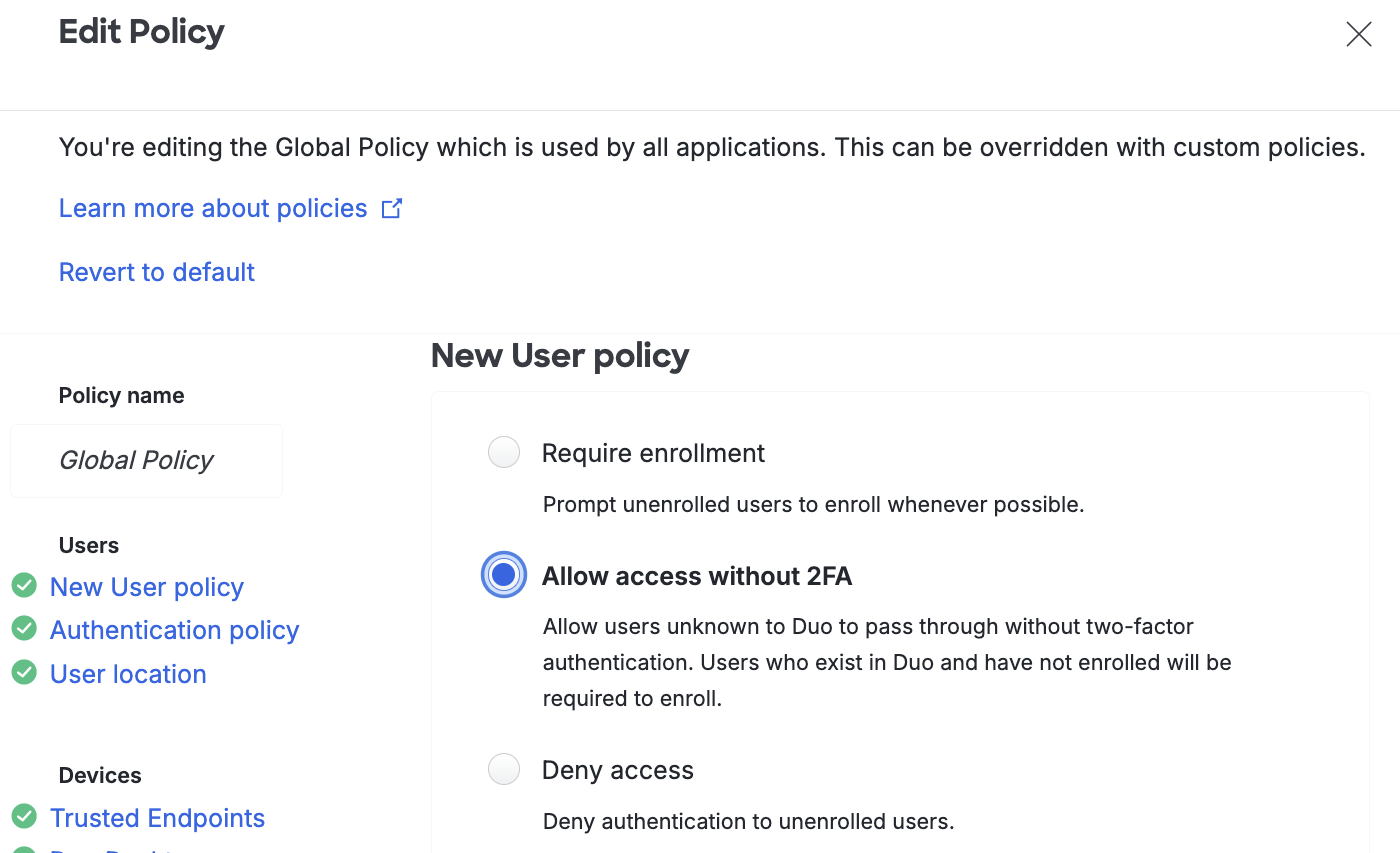
From now on, only users who are participating in the proof of concept and have completed enrollment (as in step 4) will be asked to provide secondary Duo authentication. Unenrolled users — meaning users who do not exist in Duo — will log in as usual, with no two-factor authentication required.
-
Configure your system, device, or application to use Duo two-factor authentication with the application created in step 6 using the documentation specific to your device or service. You'll typically find configuration instructions for that specific application linked from the application's details page in the Duo Admin Panel.
-
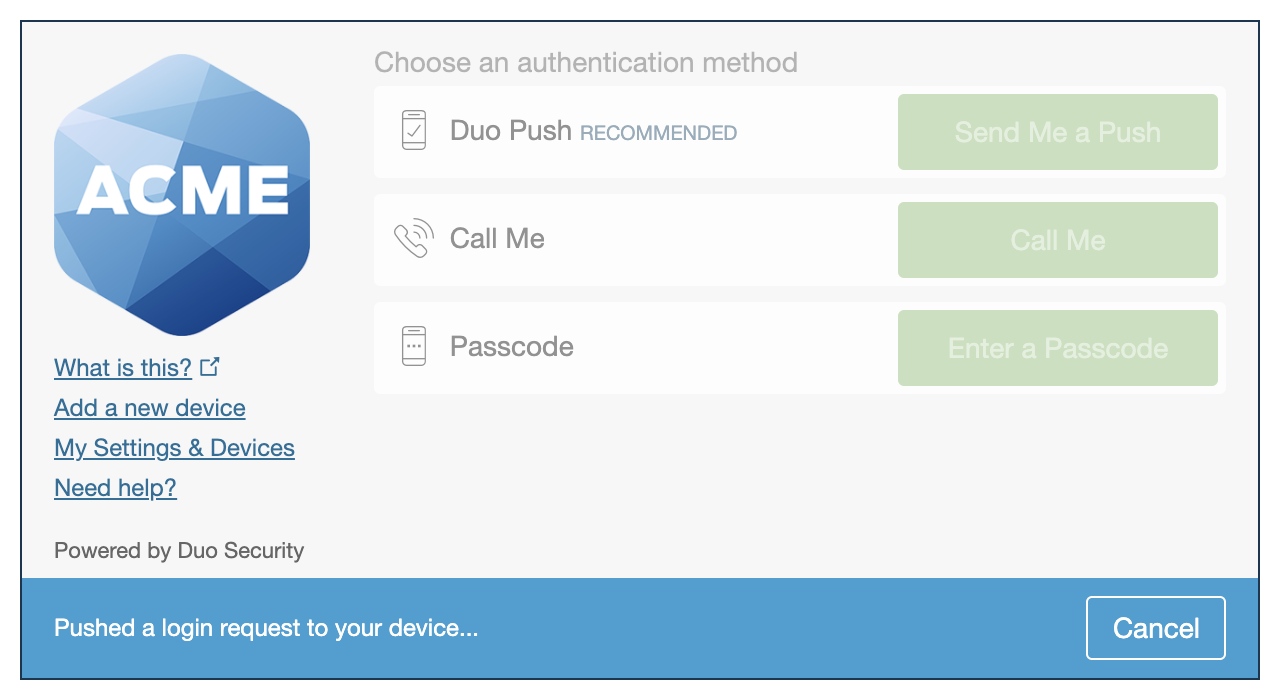
Ask the newly enrolled proof-of-concept users to log in to the Duo protected service. They will now see the Duo prompt and be asked to complete secondary authentication. Unenrolled users will not be prompted for secondary authentication. Example browser-based Duo experiences shown below.
Universal Prompt Traditional Prompt 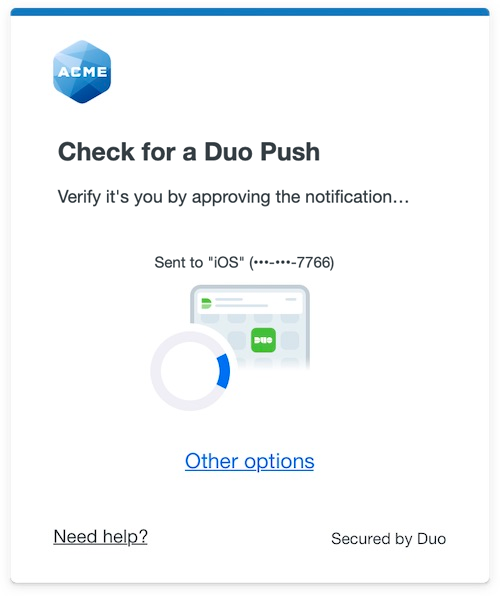
Next Steps
Expand your successful proof-of-concept by enrolling additional users with bulk enrollment, directory sync, or another method, adding additional applications to protect your other services, or exploring different policy options.
When you're ready to protect all your users with Duo two-factor authentication, be sure to edit your application's properties to change the new user policy back to Require Enrollment (or to Deny Access if your preference is to send your users enrollment links instead of allowing them to self-enroll in Duo when logging in to your protected system).
Troubleshooting
Need some help? Try searching our Knowledge Base articles or Community discussions. For further assistance, contact Support.
