We see Duo serving as a core technology building block to enable our zero trust security philosophy. We chose Duo primarily due to three reasons: broadest coverage of devices and applications; great user experience for accessing protected internal tools; and simple implementation and roll-out.
Read the customer storyVivian Ho
Security Software Engineer, Lyft


[Duo] is one of the most effective security products we have rolled out. The simple subscription-based pricing is easy to manage and we know exactly what we are getting.
Read the customer storyWayne Keatts
Assistant Vice President & Information Security Officer, Methodist Health System


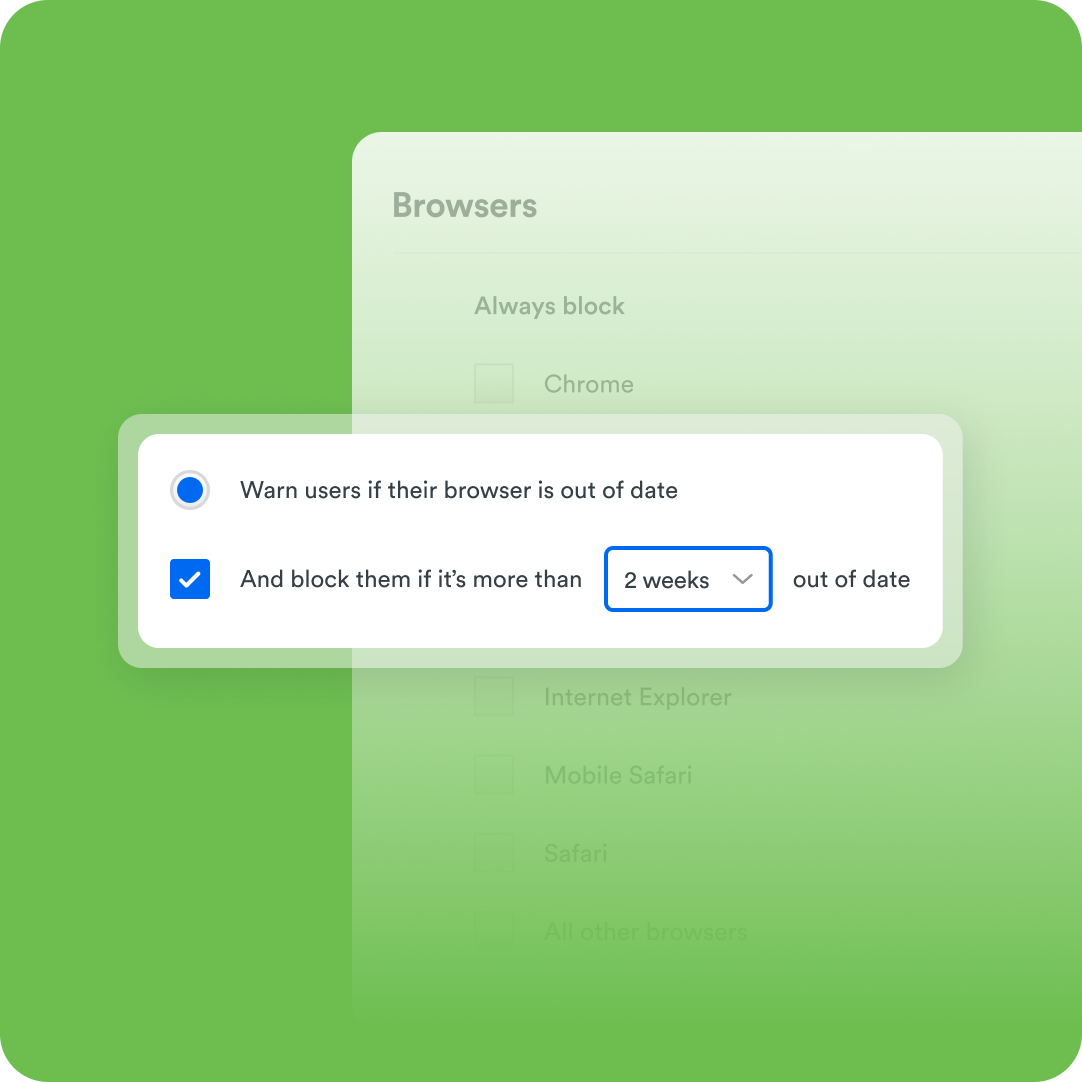
When users are on an out-of-date web browser—and when being out-of-date introduces critical vulnerabilities—we want to be able to make users aware of that. We want to help them to take the [necessary] steps themselves to remediate that vulnerability. This empowers the user to do it directly, rather than creating work that a small IT department doesn’t really have time for in every case-by-case basis.
Read the customer storyAllan Edwards
Senior Security Analyst, Eastern Michigan University