Duo Two-Factor Authentication for Microsoft UAG (Deprecated)
Last updated:
End of Support Information
Microsoft Unified Access Gateway (UAG) reached Microsoft's end of support in April 2020. See the list of Microsoft products ending support in 2020 for more information.
The last date of support for Duo two-factor authentication on UAG was February 21, 2022.
After that date, no new Microsoft UAG applications may be created in the Duo Admin Panel. In addition, Duo Support will no longer provide configuration or troubleshooting assistance for UAG.
If you created a Duo Microsoft UAG application before February 21, 2022:
- Your existing Microsoft UAG configuration continues providing two-factor authentication for user logins.
- You may view and manage existing Microsoft UAG applications in the Duo Admin Panel.
Consider migrating to a supported solution for publishing web applications, like Duo Network Gateway.
Review the Duo End of Sale, Last Date of Support, and End of Life Policy.
The instructions for this solution were removed on March 31, 2025. Customers who had this configuration deployed before then and need to refer to the original instructions to execute the migration to a supported solution may contact Duo Support.
Troubleshooting
Need some help? Review troubleshooting tips for the Authentication Proxy and try the connectivity tool included with Duo Authentication Proxy 2.9.0 and later to discover and troubleshoot general connectivity issues.
Also take a look at our UAG Knowledge Base articles or Community discussions. For further assistance, contact Support.
Network Diagram
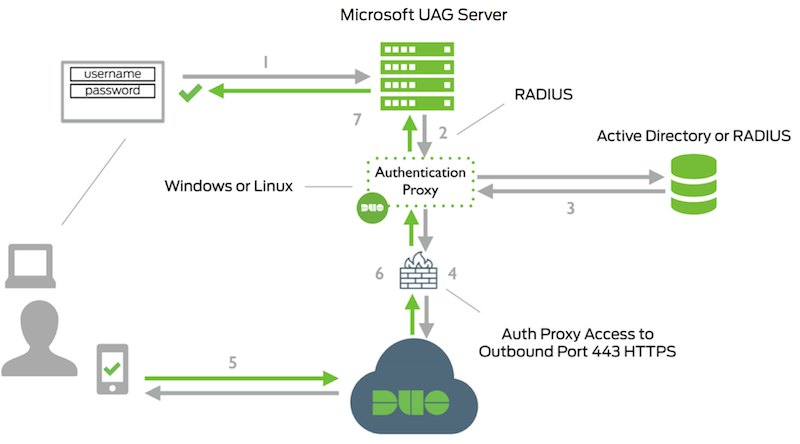
- Primary authentication initiated to UAG Server
- UAG Server sends authentication request to Duo Security’s authentication proxy
- Primary authentication using Active Directory or RADIUS
- Duo authentication proxy connection established to Duo Security over TCP port 443
- Secondary authentication via Duo Security’s service
- Duo Authentication Proxy receives authentication response
- UAG access granted
