Five Steps to Perimeter-Less Security: Adopting a Zero Trust Model for Secure Application Access
This guide examines:
- The shift away from traditional perimeter-based security and tools
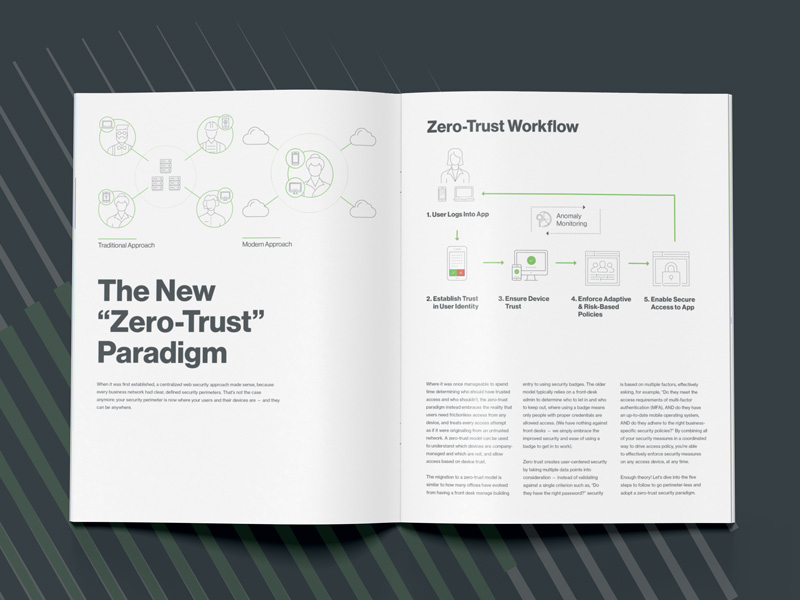
- The new zero trust security paradigm and what it means for your business
- How to enable secure access to cloud and on-premises applications based on user identity and the trustworthiness of devices
- The zero trust security maturity model
- Five crucial steps you can take to efficiently and effectively adopt a zero trust security model within your organization
Modern security is evolving beyond the perimeter. Users want to access critical work applications from anywhere, at any time and from any device, and the security models to support that must evolve.
While the concept of zero trust security has been around for nearly a decade, it again grabbed headlines with Google’s BeyondCorp architecture, which is based on the principles of zero trust.
A zero trust security model states that organizations should not trust anything inside or outside of their network perimeters and should instead verify anything and everything that tries to connect to applications and systems before granting them access. Simply put, no traffic inside a network is any more trustworthy by default than traffic coming from the outside and it’s up to an organization to determine under which conditions they decide to trust something – a user or a device – to grant it access.
In this ebook, we’ll examine the zero trust security model and dig into five key steps to move your organization beyond the perimeter and base application access on user identity and the trustworthiness of devices.