Securing Organizations Against Identity-Based Threats
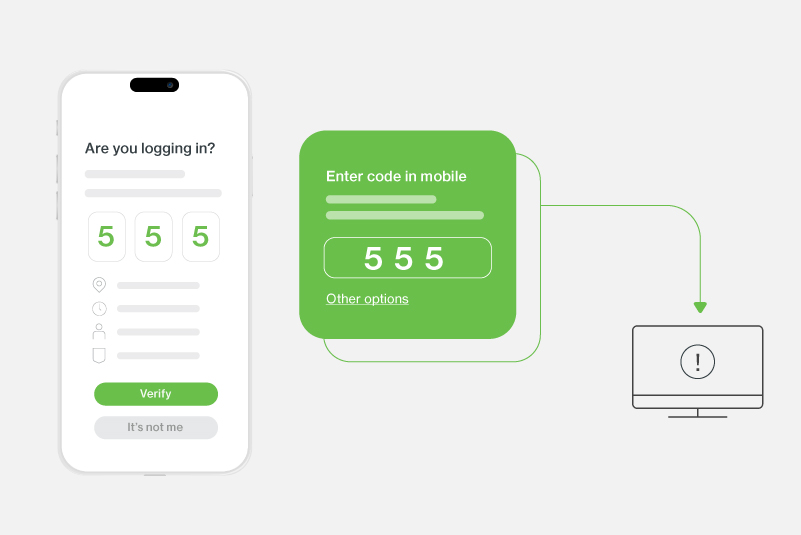
From intercepting one-time codes to stealing session cookies, attackers love to launch threats targeting multifactor authentication (MFA). So, what’s the attacker game plan and how can you modernize (and galvanize) your secure access?
In our free eBook, Attack Vectors Decoded: Securing Organizations Against Identity-based Threats, we take you inside the criminal playbook and give you the tools to build powerful, secure identity access that protects your business, your data, and your workers -- wherever they are.
In this eBook, you'll learn:
- How to combine your device authentication and security
- The anatomy of an MFA-targeted attack – straight from the criminal playbook
- What you can do right now to modernize your secure access
- How to use reactive tools to improve your security posture
- What the strongest authorization posture looks like
- How you can improve your security efficacy in the face of threats
Who is this guide for?
- CISOs who want to learn proactive security strategies
- Business leaders who want to keep their organizations secure
- Anyone curious about the future of identity security