Duo Authentication for Windows Logon and RDP - FAQ
Last updated:
General
Does Duo for Windows Logon use the traditional Duo Prompt?
No, the Duo for Windows Logon user interface is not shown in a browser iframe. While it has a design similar to the traditional Duo Prompt it does not actually use the end-of-support traditional Duo Prompt.
Is Duo for Windows Logon affected by the traditional Duo Prompt end of life?
No, Duo for Windows Logon is unaffected by the traditional Duo Prompt end of life and requires no action ahead of the traditional Duo Prompt end-of-life date.
Can I update Duo for Windows Logon to use Duo Universal Prompt?
No, Duo Universal Prompt is exclusively available to Duo applications that use OIDC or the Duo Web SDK to show the Duo login prompt in a browser window. Duo for Windows Logon does not show a browser-based Duo login prompt.
Which versions of Duo for Windows Logon support Verified Duo Push?
Verified Duo Push support in Duo for Windows Logon was introduced in the 4.3.16 beta release and became generally available in version 5.0.0. We recommend updating any 4.3.16 beta installations to the most recent non-beta release.
Duo for Windows Logon releases 4.3.1 and earlier will not offer Verified Duo Push regardless of the effective authentication methods policy setting.
Is Duo for Windows Logon affected by the 2026 Duo CA bundle expiration?
No. While messaging regarding the 2026 Duo root certificate authority bundle replacement originally identified Duo for Windows Logon versions 4.3.16, 5.0.0, and 5.1.0 as affected by the CA root expiration, they are not impacted. An issue was discovered with certificate pinning in those versions which prevented successful CA verification, meaning that those releases effectively do not perform certificate pinning at all. Therefore, no version of Duo Authentication for Windows Logon is affected by the Duo CA bundle expiration in 2026.
Duo for Windows Logon 5.2.0 corrects the issue with certificate pinning. This version and all releases that follow support the updated certificate authorities.
We do still encourage updating older installs to current versions to obtain security fixes and experience new features and enhancements.
What logon interfaces can Duo protect?
Duo Authentication for Windows Logon provides two-factor authentication for both RDP and local console logons, and credentialed UAC elevation prompts (e.g. Right-click + "Run as administrator").
Duo's Windows Logon client does not add a secondary authentication prompt to the following logon types:
- Shift + right-click "Run as different user"
- PowerShell "Enter-PSSession" or "Invoke-Command" cmdlets
- Non-interactive logons (i.e. Log on as a Service, Log on as Batch, Scheduled Tasks, drive mappings, etc.)
- Pre-Logon Access Providers (PLAPs) such as Windows Always On VPN
- RDP Restricted Admin Mode
Duo Premier and Advantage plan customers can protect PowerShell and SSH with Duo Windows Command Line Protection, or enforce MFA for other types of Active Directory logins with Legacy AD Protection.
Can remembered devices be used over RDP (Remote Desktop Protocol) connections?
No, RDP logins will not see the option to remember the device in the Duo for Windows 2FA prompt. Consider applying an authorized networks policy to the Duo Microsoft RDP application to minimize interactive Duo authentication for RDP users.
How are local trusted sessions created by the remembered device option invalidated or revoked?
An existing device trust session ends under any of the following conditions:
-
If an administrator resets the user's remembered devices session with the Require 2FA on Next Auth button on a user's details page in the Duo Admin Panel.
-
Changes to the operating system session state: When initialized the Duo credential provider determines if the Windows logon type is a workstation unlock or a new logon session. A new logon session will require Duo multi-factor authentication (MFA), and subsequent workstation unlocks bypass interactive MFA for the duration of the "Remember me" session.
- Confirm this by enabling debug logging, reproducing the issue, and checking for the this output in the
%PROGRAMDATA%\Duo Security\duo.logfile:CanTrustSession isUnlockSession=false “Session not trusted because it is login session, not unlock – secondary authentication required.”
- Confirm this by enabling debug logging, reproducing the issue, and checking for the this output in the
-
Change to network location: At each logon authentication attempt Duo snapshots and compares the network state of the user's device to determine whether it differs from the most recent network used to create a local trusted session. If the network state has changed and you have not configured the "Always remember devices from these networks" option for Windows (supported in version 5.2.0 and later) in the effective remembered devices policy settings, Duo prompts for interactive MFA. Some changes to the network state that could invalidate a session are connecting to a different wireless or wired network, switching from a wired to wireless connection on the same network, or connecting to a VPN network.
- Confirm this by enabling debug logging, reproducing the issue, and checking for this output in the
%PROGRAMDATA%\Duo Security\duo.logfile:CanTrustSession hasNetworkChanged=true
- Confirm this by enabling debug logging, reproducing the issue, and checking for this output in the
-
Use of offline authentication: If a user logs in to or unlocks the workstation with Duo offline access, Duo prompts for interactive MFA at the next online login.
-
User action: If a user clicks the "Cancel" button during login of a local trusted session, Duo prompts for interactive MFA.
- Confirm this by enabling debug logging, reproducing the issue, and checking for this output in the
%PROGRAMDATA%\Duo Security\duo.logfile:User canceled trusted session login for user:
- Confirm this by enabling debug logging, reproducing the issue, and checking for this output in the
-
Policy change: If a Duo administrator removes the remembered devices policy from the Duo Microsoft RDP application or edits the policy to disable the "Remember devices for Windows Logon" setting, at the next logon or workstation unlock the local Duo application applies the policy change and prompts for interactive MFA.
-
Registry edit: The trusted session created by remembering the device adds a registry key at
HKLM\Software\Duo Security\DuoCredProv\Users\<UserSID>. If that registry key for a user is deleted, Duo prompts for interactive MFA. -
Trusted session length: If a trusted session length exceeds the limit set by an administrator in the Duo Admin Panel “Remember devices for Windows Logon” option, Duo prompts for an interactive MFA on the next Windows logon or unlock attempt.
- Confirm this by enabling debug logging, reproducing the issue, and checking for this output in the
%PROGRAMDATA%\Duo Security\duo.logfile:Session trust expired – secondary authentication required
- Confirm this by enabling debug logging, reproducing the issue, and checking for this output in the
-
Passwordless for Operating System (OS) Logon enabled: If Passwordless OS Logon is enabled for the Duo Microsoft RDP application in use, remembered devices policy settings have no effect. Passwordless for OS Logon removes the manual requirement for users to provide an OS password when logging into their workstation by automatically invoking a Bluetooth push for users to authenticate with their biometrics or PIN via Duo Mobile to resume their session.
Does Duo Authentication for Windows Logon support offline multifactor authentication?
Yes, MFA using a Duo Mobile passcode or supported U2F security key while a Windows system is unable to reach Duo's service is supported in version 4.0 and later. Learn more about offline access.
Do offline sessions work with remembered devices?
No, a trusted device session created with the "Remember me" option during online Duo authentication does not maintain the trusted session for offline access, and an offline access login will not show the option to remember the device.
Which security keys are compatible with offline access with MFA?
Offline access for Windows Logon works with these security keys:
- Yubico brand keys supporting U2F/FIDO2 (Vendor ID 1050)
- Feitian ePass FIDO (Vendor ID 096E)
- Thetis FIDO (Vendor ID 1EA8)
Older Google Titan U2F keys with Vendor ID 096E will work, but newer Google Titan keys with Vendor ID 18d1 will not.
HyperFIDO tokens are not supported for offline access activation, nor are simple OTP passcode tokens or Duo D-100 hardware tokens. Do not use tokens that require extended length encoding.
Is it possible to use the same authentication device for both online and offline Windows Logon?
Yes, you may use these authentication devices for both online and offline access with a single device:
- An Android or iOS device with Duo Mobile activated for both online and offline 2FA.
- A hardware token that supports both OTP and U2F (like the YubiKey 5 series).
Does Duo support ARM processors?
Duo for Windows Logon 5.2.0 and later fully support ARM64 processors. ARM devices must run Windows 10 version 1709 or later.
Does Duo support Windows 11?
Yes, Duo for Windows Logon version 4.2.0 and later supports Windows 11 64-bit clients.
Does Duo support Windows 10?
Duo does not offer support for Windows integrations running on Windows operating system versions beyond Microsoft's Extended Support End date.
Windows 10 reached Microsoft's end of mainstream support on October 14, 2025, with Extended Support until October 13. 2026. Duo will support Windows 10 through the ESU period and will end support in October 2026.
Please see Are Duo's Windows applications supported on Windows versions that are end-of-life? in the Duo Knowledge Base for detailed Duo for Windows lifecycle support information.
Does Duo support Windows Vista, Windows 7, Windows 8, or Windows 8.1?
Microsoft end-of-support information for these Windows clients is as follows:
- Windows Vista extended support ended on April 11, 2017.
- Windows 7 extended support ended on January 14, 2020.
- Windows 8 extended support ended on January 12, 2016.
- Windows 8.1 extended support ended on January 10, 2023.
Duo's last day of support for installation and use of any Duo applications on Windows operating systems corresponds with the Microsoft end of support. We strongly urge you to upgrade to a supported version of Windows.
Does Duo support Windows Server Core installations?
Server Core installs were supported prior to Duo for Windows Logon version 4.0.0. Nano (headless) installs are not supported in any version.
Does Duo support Windows Server 2025?
Yes, Duo for Windows Logon version 5.0.0 and later supports Windows Server 2025 full desktop GUI installs.
Server Core and Nano (headless) installs are unsupported.
Does Duo support Windows Server 2016, 2019, or 2022?
Yes, Server 2016 full desktop GUI installs are supported starting with version 2.1.0. Duo for Windows Logon version 4.0.0 adds Server 2019 support and version 4.2.0 adds Server 2022 support.
Server Core installs are unsupported as of v4.0.0. Nano (headless) installs are unsupported by any release.
Does Duo support Windows Server 2012 or 2012 R2?
Microsoft ended extended support for Windows Server 2012 and 2012 R2 on October 10, 2023. Duo's last day of support for installation and use of any Duo applications on Windows operating systems corresponds with the Microsoft end of support. Duo for Windows Logon v5.0.0 removed installer support for these versions. We strongly urge you to upgrade to a supported version of Windows Server.
Does Duo support Windows Server 2008, or Windows Server 2008 R2?
Microsoft ended extended support for Windows Server 2008 and 2008 R2 on January 14, 2020. Duo's last day of support for installation and use of any Duo applications on Windows operating systems corresponds with the Microsoft end of support. We strongly urge you to upgrade to a supported version of Windows Server.
Can I use Duo with a Microsoft account?
There is a known issue with using Duo authentication and Microsoft/Live accounts after installing the Windows 10 Fall Creators Update (version 1709) released 10/17/17.
As a temporary workaround, you can allow the Windows Live credential provider, which restores the login prompt for Microsoft and Live.com accounts.
With this workaround in place, Microsoft and Live.com account users log in without Duo 2FA! Domain and local accounts still require Duo authentication.
To enable the Windows Live credential provider for Microsoft and Live.com accounts, use the Registry Editor (regedit.exe) with administrator privileges to create (or update) the following registry values:
Location: HKLM\SOFTWARE\Duo Security\DuoCredProv:
| Registry Value | Type | Description |
|---|---|---|
ProvidersWhitelist
|
REG_MULTI_SZ | {F8A0B131-5F68-486C-8040-7E8FC3C85BB6} |
For Windows systems not running the Windows 10 version 1709 update, you can authenticate with Duo Authentication for Windows Logon using a Microsoft attached account on a standalone system if you enable the local group policy setting "Interactive logon: Do not display last user name" and enroll the username of the Microsoft account in Duo.
To edit your local policy (must be a local administrator):
- Run the command gpedit.msc to open the Local Group Policy Editor.
- Navigate to Local Computer Policy → Computer Configuration → Windows Settings → Security Settings → Local Policies → Security Options.
- Double-click the Interactive logon: Do not display last user name setting.
- Select Enabled and click OK.
- Close the Local Group Policy Editor window.
You can also enable the setting via the registry. Create a new DWORD value dontdisplaylastusername set to 1 at HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System.
With this setting enabled you receive the "Other user" login dialog, where you can input your Microsoft account credentials.
On a domain-joined workstation this setting may be controlled by your administrator.
To determine the username of the Microsoft account on a Windows 10 computer, open the Windows User Manager (lusrmgr.msc), locate the Microsoft account in the list, and look at the Name field for that user. The Name value of the Microsoft account won't be the full e-mail address that you use to sign in, but instead will be shown as a portion of the local part of the email address (the information before the @ symbol). When you have found the Name value for the Microsoft account, enroll that account in Duo. If you do not enroll the account in Duo with the correct username you may not be able to complete log in with the Microsoft account.
How does Duo Authentication for Windows Logon work with NLA (Network Level Authentication)?
Network Level Authentication (NLA) for Remote Desktop Connection is an optional security feature available in Windows Vista and later. When NLA is enabled, remote connections pre-authenticate to the remote system when the RDP client connects before displaying a full remote session. When NLA is disabled, the Windows username and password is entered within the RDP client session after connecting.
When Duo Authentication for Windows Logon is installed on a system where NLA is enabled the RDP client prompts for the Windows username and password in a local system dialog. That information is used to connect to the remote system and passed through to the Remote Desktop manager. Once the RDP client has completed primary authentication the full Remote Desktop session is displayed, and the Duo Security prompt appears for two-factor authentication.
When Duo Authentication for Windows Logon is installed on a system where NLA is not required a full Remote Desktop session is displayed when the RDP client connects to the remote system. The Windows username and password are entered in the Remote Desktop window, and after the logon information is accepted the Duo Security prompt appears for two-factor authentication.
There are some security advantages to enabling NLA, but one of the drawbacks is that users with expired passwords are prevented from logging on to the remote system. More information about NLA and RDP can be found at the Microsoft site and on Wikipedia.
Does Duo Authentication for Windows Logon support web proxying?
Duo can use the HTTPS proxy server configured in your system-wide WinHTTP settings. Configure the proxy server(s) used by WinHTTP with the netsh command.
Duo Authentication version 2.0.0.71 and later also support proxying only Duo authentication traffic. Refer to the instructions for configuring a Duo only proxy.
Does Duo Authentication for Windows Logon work with third-party disk encryption software or other credential providers?
Duo's credential provider cannot be chained with other credential providers present on your system. Disk encryption software that stores the Windows username and password provided before boot may no longer use those credentials to automatically log on to Windows.
Duo Authentication for Windows Logon version 2.1.0 permits use of the Windows smart card login provider as an alternative to Duo, meaning that users may choose to authenticate with either Duo 2FA or a PIV/CAC card. Duo for Windows Logon v3.1.0 adds support for smart cards logon with Duo 2FA at the local console.
Does Duo support Windows XP or Windows 2003?
Microsoft ended support for Windows XP on April 8, 2014 and for Windows Server 2003 on July 14, 2015. The last Duo release with XP and 2003 compatibility was version 1.1.8. Duo's last day of support for installation and use of any Duo applications on these operating systems corresponds with the Microsoft end of support. We strongly urge you to upgrade to a supported version of Windows.
Install and Uninstall
Will upgrading Duo for Windows Logon invalidate offline access or passwordless OS logon enrollment?
Upgrading Duo for Windows Logon (RDP) using the steps from our integration guide is not expected to invalidate offline access enrollments or passwordless OS logon enrollments. However, to back up the offline and passwordless OS logon registry settings prior to upgrading, see this help article for further instructions: How do I backup offline access or passwordless OS logon enrollment when uninstalling or upgrading Duo for Windows Logon?.
WARNING: An issue is present in the Duo Authentication for Windows Logon 5.2.0 installer which may cause removal of Duo registry keys and values created after the initial installation when upgrading from a prior version to 5.2.0 using a silent install method. This affects existing user offline access and paswordless OS logon enrollments and users may need to re-enroll in offline access and passwordless OS logon.
This issue is not seen with interactive GUI installations and is corrected in the 5.2.1 release. Please do not install 5.2.0 via silent install if any user enrollments in offline access or passwordless OS logon, or any Duo registry keys and values created after your initial install exist on your clients.
Learn more about the 5.2.0 installer issue in the article Guide to issues with the Duo Authentication for Windows Logon 5.2.0 installer in the Duo Knowledge Base.
How do I update my installed Duo Authentication for Windows Logon software?
Please see Updating Duo Authentication for Windows Logon for details.
Does installing Duo Authentication for Windows Logon require a reboot?
Installing Duo may require a reboot depending on the state of your Windows system, and files in use during installation. Schedule your Duo installation during a maintenance window if unplanned system restarts is a concern.
You may be able to suppress the reboot during silent MSI install or upgrade with the flags /quiet /qn /norestart, so you can schedule the reboot at a better time.
Deployment via Microsoft Group Policy will always require a reboot before installation because software deployment GPOs targeting computers apply and install during the Windows pre-boot stage.
Does Duo Authentication for Windows Logon depend on any other software packages?
Duo Authentication for Windows Logon 4.3.16, 5.0.0, and later depend on the Microsoft Visual C++ 2022 Redistributable. The Duo EXE installer (i.e. duo-win-login-5.0.0.exe) will also install the Visual C++ Redistributable package on your system if a compatible version is not already present.
Duo MSI installers (DuoWindowsLogon32.msi or DuoWindowsLogon64.msi) do not install the Visual C++ prerequisite package, nor do they prevent installation of Duo if the Visual C++ Redistributable is not present on the target system. The Visual C++ Redistributable must be installed separately from Duo Authentication for Windows Logon when using the Duo MSI installers.
Why do I see both version 4.3.0 and 4.3.1 installed on my computer after attempting an upgrade?
Modifications made to the Duo Authentication for Windows Logon version 4.3.1 installer result in direct upgrades from version 4.3.0 to version 4.3.1 leaving the program information for 4.3.0 visible in Add/Remove Programs and the registry. This does not affect the installed 4.3.1 application's operation.
If you wish to remove the duplicate Duo Authentication for Windows Logon entry for 4.3.0 you may uninstall it without affecting the 4.3.1 installation. Uninstalling 4.3.1 will entirely remove the application from your system, and require reinstallation if you wish to continue using Duo.
Upgrades from version 4.2.2 and earlier to version 4.3.1 do not experience this, nor will upgrades from version 4.3.1 to later releases.
Can I silently install Duo Authentication for Windows Logon from a command line or PowerShell?
Yes, you can run the .exe or .msi installers from PowerShell or the Command Prompt. This has no required parameters, but if you do not supply the IKEY, SKEY, and HOST values from the command line make sure you have a Windows group policy object applying values for those settings, or make them present in the registry using another method, otherwise the Duo for Windows Logon application will not function.
Enter the following command into PowerShell or a Command Prompt to silently install Duo Security with automatic push on, fail open enabled, smart cards disabled, and protecting both RDP and console logons (this example uses v4.0.2, replace the file name with the version number you have downloaded):
duo-win-login-4.0.2.exe /S /V" /qn IKEY="DIXXXXXXXXXXXXXXXXXXXX" SKEY="xxxxxxxxxxxxxxxxxxxxxxxxxxxxxx" HOST="api-xxxxxxxx.duosecurity.com" AUTOPUSH="#1" FAILOPEN="#1" SMARTCARD="#0" RDPONLY="#0""Note that the parameter names passed to the installer (IKEY, SKEY, HOST, etc.) are case-sensitive!
The following table lists all the parameters and options that may be set via the command line installer (as of v4.0.2), noting default values if not specified in the command.
| Setting | Description | Default |
|---|---|---|
| IKEY | Your Duo RDP application's integration key. | Blank; product will not function |
| SKEY | Your Duo RDP application's secret key. | Blank; product will not function |
| HOST | Your Duo API hostname. | Blank; product will not function |
| AUTOPUSH | 1 to automatically send a push request, or 0 to disable automatic push. |
0 |
| FAILOPEN | 1 to allow access when Duo's service is unreachable, or 0 to block access without Duo MFA. |
1 |
| RDPONLY | 1 to only require Duo for remote logons, or 0 to require Duo for console and RDP logons. |
0 |
| SMARTCARD | 1 to allow smart card login as an alternative to Duo, or 0 to disable the Windows smart card provider. |
0 |
| WRAPSMARTCARD | 1 to require Duo after smart card primary logon at the local console, or 0 to allow smart card logon without Duo approval afterward. |
0 |
| ENABLEOFFLINE | 1 to enable offline access (subject to the configuration in the Admin Panel), or 0 to completely disable offline access on the target system. |
1 |
| USERNAMEFORMAT | The username format sent to Duo. One of: 0 for sAMAccountName (narroway), 1 for the NTLM domain and username (ACME\narroway), or 2 for the userPrincipalName (narroway@acme.corp). |
1 |
| PROXYHOST | The hostname or IP address of an upstream HTTP proxy server for Duo communications | Not set |
| PROXYPORT | The port for HTTP proxy communications. | Not set |
| LOGFILE_MAXCOUNT | Number of rotated log files to be maintained. | Not set |
| LOGFILE_MAXSIZEMB | Size of rotated log file to be maintained in megabytes (MB). | Not set |
| UAC_PROTECTMODE | 0 to respect existing Duo authentication settings for logon, 1 to disable Duo at logon and only prompt during User Elevation, or 2 to enforce Duo 2FA at both logon and User elevation. |
0 |
| UAC_OFFLINE | 1 to enable offline access for User Elevation, or 0 to disable offline access for User Elevation. |
1 |
| UAC_OFFLINE_ENROLL | 1 to enable offline access enrollment during User Elevation, or 0 to prevent Offline Enrollment during User Elevation. |
1 |
| ENABLECERTPINNING | 1 to enable certificate pinning or 0 to disable it. |
1 |
When specifying a value for one of the DWORD options (a value of 0, 1, or 2), be sure to prefix it with a pound sign #, e.g. RDPONLY=#1.
This performs the install with the same settings in the previous example from the command line with Windows Installer (msiexec), using the 64-bit MSI installer included in the Duo Authentication for Windows Logon Group Policy MSI installers, template files, and documentation package. View checksums for Duo downloads here.
msiexec.exe /i DuoWindowsLogon64.msi IKEY="Integration Key" SKEY="Secret Key" HOST="API Hostname" AUTOPUSH="#1" FAILOPEN="#1" SMARTCARD="#0" RDPONLY="#0" /qnThe MSI installers and properties can also be used to create a transform file for use with with Active Directory Group Policy Software Publishing or other automated software deployment utilities. See the Duo Authentication for Windows Logon Group Policy documentation for more information.
Can I silently upgrade Duo Authentication for Windows Logon from a command line?
Enter the following command into a Command Prompt to silently upgrade an existing Duo installation using the MSI of a newer version, preserving the current integration information and installed options (as of v4.0.2):
msiexec.exe /qn /i "DuoWindowsLogon64.msi"For MSI upgrade installs of releases prior to v4.0.2, and to upgrade from v4.1.0 to 4.1.1 or later, include the options shown in this command:
msiexec.exe /quiet /i "DuoWindowsLogon64.msi" REINSTALL=ALL REINSTALLMODE=vomus IS_MINOR_UPGRADE=1To silently upgrade using a newer installer executable, enter this command (this example uses v4.1.3, replace the file name with the version number you have downloaded):
duo-win-login-4.1.3.exe /S /v/qnCan I silently uninstall Duo Authentication for Windows Logon from a command line or PowerShell?
Enter the following command into PowerShell or a Command Prompt to silently uninstall Duo for Windows Logon using the same version of the installer executable that you have installed on the system (so this example uses the v4.1.3 installer to remove v4.1.3 from the system):
duo-win-login-4.1.3.exe /S /v/qn /XIf you no longer have the same installer executable that matches the Duo installation you wish to remove, use msiexec to perform the uninstall. You will first need to determine the correct product code GUID for your installed version:
-
Launch the Registry Editor (regedit.exe).
-
Navigate down the tree to
HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall. -
Examine the GUID keys until you locate the key with the
DisplayNamevalue of "Duo Authentication for Windows Logon". -
Copy the UninstallString value for the Duo Authentication for Windows Logon product from the registry (for example:
MsiExec.exe /X{BD789CFF-3C7A-4533-90F3-A3E5190A9D43}). -
Use the information from the registry to construct your silent msi uninstall command:
MsiExec.exe /qn /x {BD789CFF-3C7A-4533-90F3-A3E5190A9D43}
Can I deploy or configure Duo Authentication for Windows Logon using Group Policy?
Yes. Please refer to the Duo Authentication for Windows Logon Group Policy documentation.
How do I disable or uninstall Duo Authentication for Windows Logon in Safe Mode?
To disable Duo's credential provider on Windows after booting in Safe Mode, run the following from an elevated command prompt:
Versions 1.2.0.14 and earlier
regsvr32 /u "C:\Program Files\Duo Security\DuoCredProv\DuoCredProv.dll"
regsvr32 /u "C:\Program Files\Duo Security\DuoCredProv\DuoCredFilter.dll"
Version 2.0.0 and later
regsvr32 /u "C:\Program Files\Duo Security\WindowsLogon\DuoCredProv.dll"
regsvr32 /u "C:\Program Files\Duo Security\WindowsLogon\DuoCredFilter.dll"
You can also uninstall the Duo Windows Logon integration while still in safe mode with a registry change and a service start.
- When booted into safe mode, launch the Registry Editor (regedit.exe).
- Drill down into the HKLM\System\CurrentControlSet\Control\SafeBoot\Minimal registry hive (if you are booted into regular safe mode) or down to HKLM\System\CurrentControlSet\Control\SafeBoot\Network (if you are booted into safe mode with networking).
- Right-click the Minimal or Network registry key (as appropriate for your currently booted mode) and click New → Key on the context menu. Name the new key MSIServer.
- From an elevated command prompt, run the command
net start msiserver. - You can now use Programs and Features on the Windows Control Panel to uninstall the Duo application.
For more information about Safe Mode refer to the instructions for your operating system: Windows 10, Windows 8/8.1 and 2012/2012 R2.
Windows 10 users may need the BitLocker recovery key in order to boot the system into safe mode. If you don't have it available, use one of Microsoft's recommendations to locate it.
Configuration
Where are the Duo for Windows Logon settings stored in the registry?
Duo Authentication for Windows Logon stores the installation settings in the registry at HKLM\Software\Duo Security\DuoCredProv.
If you're managing the Duo client configuration with Windows Group Policy, then any setting configured by a GPO is stored as a registry value in HKLM\Software\Policies\Duo Security\DuoCredProv, and overrides the same setting configured at the default registry location.
Since GPO settings get reapplied periodically at the client system, any permanent changes to a setting configured via group policy should be made by editing the GPO to update the setting with the new value, not by updating the client registry.
How does offline access in Duo for Windows Logon interact with fail mode?
Enabling offline access on the RDP v4.0 or later application overrides the configured fail mode setting for users who activate offline access.
Users who have not activated offline access are subject to the fail mode setting e.g. if set to fail open, a user who did not activate offline access would be able to log in without completing Duo offline authentication. Disable "fail open" if you want to prevent users who did not activate offline access from logging in when the computer is offline.
How can I configure the fail mode?
When the fail mode is set to "fail open", it permits the Windows logon to continue if it is unable to contact the Duo service. You can set the fail mode during installation to "fail closed" by deselecting the "Bypass Duo authentication when offline" box during installation. This will deny all login attempts if there is a problem contacting the Duo service.
By default, Windows Logon 4.2.2 and earlier installers the fail mode is set to "fail open".
Windows Logon 4.3.0 installers will default to "fail closed". The msi installer will preserve the selection made by a previously installed version on upgrade. Upgrades from previous versions using the exe installer will override the previous fail mode selection and default to fail closed.
To change the fail mode after installation, use the Registry Editor (regedit.exe) with administrator privileges to create or update the following registry value:
Location: HKLM\SOFTWARE\Duo Security\DuoCredProv:
| Registry Value | Type | Description |
|---|---|---|
FailOpen
|
DWORD | Set to 1 to allow "fail open" for all users or 0 to restrict to "fail closed" (except for users who have activated offline access in v4.0 or later). Default: Fail open. |
If the Duo settings are managed by Windows Group Policy, those settings override any changes made via regedit. Update the "Duo Service: Fail Open if Unable to Contact Duo" setting in the GPO instead.
When modifying the FailOpen registry value on a Windows 2003 or XP system a reboot is required to make the change effective.
How can I configure automatic push?
When automatic push is enabled, Duo Authentication for Windows Logon automatically sends a push notification to the Duo Mobile app or a phone call to the user's default device after submitting the Windows username and password. This is the installation default. You can choose to disable automatic push for all users of Duo for Windows Logon on a given system by deselecting the "Use automatic push to authenticate if available" box during installation.
To change the automatic push behavior for all users of the system after installation, use the Registry Editor (regedit.exe) with administrator privileges to create or update the following registry value:
Location: HKLM\SOFTWARE\Duo Security\DuoCredProv:
| Registry Value | Type | Description |
|---|---|---|
AutoPush
|
DWORD | Set to 0 to disable automatic push or 1 to enable it. |
If the Duo settings are managed by Windows Group Policy, those settings override any changes made via regedit. Update the "Client: Enable Auto Push" setting in the GPO instead.
When automatic push is disabled, Duo does not request logon verification until the user submits the name of an authentication factor at the Duo Authentication prompt.
How do I enable debug logging?
To enable debug logging, use the Registry Editor (regedit.exe) with administrator privileges to create the following registry value:
Location: HKLM\SOFTWARE\Duo Security\DuoCredProv:
| Registry Value | Type | Description |
|---|---|---|
Debug
|
DWORD | Set to 1 to enable debug logging. Default: No debug logging. |
If the Duo settings are managed by Windows Group Policy, those settings override any changes made via regedit. Update the "Enable Debug Logging" setting in the GPO instead to enable debug logging globally, or if you just need to temporarily enable it to capture an issue update the HKLM\Software\Policies\Duo Security\DuoCredProv\debug registry value as well (this may be reverted at the client's next GPO refresh).
The log file location is %PROGRAMDATA%\Duo Security\duo.log for version 1.1.8 and later, and %ProgramFiles%\Duo Security\DuoCredProv\duo.log for version 1.1.7 and earlier.
How can I configure log file rotation?
By default, Duo Authentication for Windows Logon will not rotate log files.
Version 4.0.6 and later supports log file rotation. To configure the log file rotation, use the Registry Editor (regedit.exe) with administrator privileges to create the following registry values:
Location: HKLM\SOFTWARE\Duo Security\DuoCredProv:
| Registry Value | Type | Description |
|---|---|---|
LogFileMaxSizeMB
|
DWORD | Set the size of log file to be maintained in megabytes (MB). Minimum Value: 1 Maximum Value: 4096 (decimal) |
LogFileMaxCount
|
DWORD | Set the number of log files to be maintained on disk. Minimum Value: 1 Maximum Value: 100 (decimal) |
Both registry keys must be created and set to a value greater than 0 to enable rotation. Backup logs will increment starting at duo00.log through duo99.log. Log may be slightly larger than the defined size to ensure an authentication in-process is not split across log files.
Example setting: LogFileMaxSizeMB to 1 and LogFileMaxCount to 1 will result in Duo.log coexisting with duo00.log, both with a maximum size of 1MB.
How do I disable certificate pinning?
Duo Authentication for Windows Logon uses certificate pinning as an additional security measure protecting communications between the client application and Duo's cloud service. Certificate pinning is enabled by default at install.
To disable certificate pinning, use the Registry Editor (regedit.exe) with administrator privileges and update the following registry value:
Location: HKEY_LOCAL_MACHINE\SOFTWARE\Duo Security\DuoCredProv\EnableCertPinning or HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Duo Security\DuoCredProv\EnableCertPinning
| Registry Value | Type | Description |
|---|---|---|
EnableCertPinning
|
DWORD | Set to 0 to disable certificate pinning. Default: 1. |
If the Duo settings are actively managed by Windows Group Policy, those settings override any changes made via regedit. Update the "Duo Service: Certificate Pinning Available" setting in the GPO instead.
Can Duo protect local console logins in Windows?
Yes, Duo Authentication for Windows Logon does provide protection for local console logins. However, it can be difficult to prevent an attacker with physical access to a system from compromising it. In particular, there are two significant threats you should take care to address:
-
Duo Authentication for Windows Logon can be bypassed by rebooting a Windows system into Safe Mode. To limit the effect of this, you should prevent all but a select group of users from logging in while Windows is running in Safe Mode (for example, via the registry DWORD value HKLM\Software\Microsoft\Windows\CurrentVersion\Policies\System\SafeModeBlockNonAdmins set to 1).
-
By default, the RDP integration will "fail open" if it is unable to contact the Duo service. A user with local console access might be able to disrupt a machine's network connectivity (e.g. by unplugging an ethernet cord), thereby bypassing Duo authentication.
You can set the fail mode during installation to "fail close" by deselecting the "Bypass Duo authentication when offline" box in the Duo installer, or by configuring the Registry DWORD value HKLM\Software\Duo Security\DuoCredProv\FailOpen set to 0 to "fail closed". This will deny all login attempts if there is a problem contacting the Duo service.
To enable Duo authentication for both local console and RDP logins, clear the "Only prompt for Duo authentication when logging in via RDP" box during installation.
To change which logon connections are required to use Duo after installation, use the Registry Editor (regedit.exe) with administrator privileges to create or update the following registry value:
Location: HKLM\SOFTWARE\Duo Security\DuoCredProv:
| Registry Value | Type | Description |
|---|---|---|
RdpOnly
|
DWORD | Set to 0 to protect both RDP and local console logons or 1 to protect RDP logons only. |
If the Duo settings are managed by Windows Group Policy, those settings override any changes made via regedit. Update the "Client: Limit Two-Factor to RDP Logons Only" setting in the GPO instead.
Can I choose which username attribute gets sent to Duo?
Duo Authentication for Windows Logon defaults to sending the username in NTLM (or msDS-PrincipalName) e.g. DOMAIN\username to Duo's cloud service as the Duo username. However, when you create your RDP application in Duo, the "Username normalization" option defaults to "Simple" normalization, so that Duo ignores anything preceding a backslash or after an at symbol in the username received in a logon request. This means Duo treats "narroway", "ACME\narroway", and "narroway@acme.local" as the same "narroway" user in Duo. Therefore, with the default username settings applied at both the Windows client and to the RDP application in Duo, we try to match the username only when looking for an existing user; essentially matching the sAMAccountName.
If the username sent to Duo by our Windows Logon application doesn't match an existing Duo username, the user can't complete Duo authentication. This causes issues when an organization has already enrolled Duo users with a different username format, like userPrincipalName (UPN).
Duo Authentication for Windows Logon version 3.1 and later allows specifying which Windows username attribute is sent to Duo's service when authenticating.
To change which Windows username attribute gets sent to Duo, use the Registry Editor (regedit.exe) with administrator privileges to create or update the following registry value:
Location: HKLM\SOFTWARE\Duo Security\DuoCredProv:
| Registry Value | Type | Description |
|---|---|---|
UsernameFormatForService
|
DWORD |
Set to 0 to send the sAMAccountName as the Duo username (e.g. "narroway"). Set to 1 to send the NTLM domain and username as the Duo username (e.g. "ACME\narroway"). This is the default installation setting. Set to 2 to send the userPrincipalName as the Duo username (e.g. "narroway@acme.local"). |
If the Duo settings are managed by Windows Group Policy, those settings override any changes made via regedit. Update the "Duo Service: Specify format of username sent to Duo service" setting in the GPO instead.
If you want Duo for Windows Logon to send the NTLM or UPN username formats to Duo, and your Duo usernames or aliases are also NTLM or UPN format, then be sure to log in to the Duo Admin Panel and change the "Username normalization" option for your RDP integration from "Simple" to "None".
Whichever username format you choose, ensure that a matching username or username alias exists in Duo.
Why might an incorrect username get sent to Duo from a machine joined to Entra ID?
Duo for Windows Logon sends the username from the logon token by default. If the resulting username is incorrect for a machine joined to Entra ID, Duo for Windows Logon 4.3.0 and later can parse the username from the login string instead.
To change how the username gets parsed on an Entra ID-joined machine, use the Registry Editor (regedit.exe) with administrator privileges to create or update the following registry value:
Location: HKLM\SOFTWARE\Duo Security\DuoCredProv:
| Registry Value | Type | Description |
|---|---|---|
ParseUsernameAndDomain
|
DWORD |
Set to 0 to send the username from logon token. Default: Disabled Set to 1 to parse the username and domain from the username login string instead of the logon token. Enable this setting when devices joined to Entra ID send an incorrect username value to Duo. |
If the Duo settings are managed by Windows Group Policy, those settings override any changes made via regedit. Update the "Client: Parse Username and Domain" setting in the GPO instead.
Can Duo protect Remote Desktop Connection logons only?
It is possible to only enable Duo authentication for RDP sessions (and not local console logins). This can be set during the installation by checking the "Only prompt for Duo authentication when logging in via RDP" box.
To change which logon connections are required to use Duo after installation, use the Registry Editor (regedit.exe) with administrator privileges to create or update the following registry value:
Location: HKLM\SOFTWARE\Duo Security\DuoCredProv:
| Registry Value | Type | Description |
|---|---|---|
RdpOnly
|
DWORD | Set to 1 to protect RDP logons only or 0 to protect both RDP and local console logons. |
If the Duo settings are managed by Windows Group Policy, those settings override any changes made via regedit. Update the "Client: Limit Two-Factor to RDP Logons Only" setting in the GPO instead.
When modifying the RdpOnly registry value on a Windows 2003 or XP system a reboot may be required to make the change effective.
Is it possible to use a web proxy only for Duo Authentication for Windows Logon traffic?
Yes, Duo Authentication for Windows Logon version 2.0.0.71 and later supports proxying only Duo authentication traffic. This can be set during the installation by checking the "Configure manual proxy for Duo traffic" box and entering your proxy host and port information.
To change the HTTP proxy settings for the Duo application after installation, use the Registry Editor (regedit.exe) with administrator privileges to create or update the following registry value:
Location: HKLM\SOFTWARE\Duo Security\DuoCredProv:
| Registry Value | Type | Description |
|---|---|---|
HttpProxyHost
|
String | Hostname or IP address of an HTTP proxy. If set, will be used for communicating with Duo Security's service. Must support the CONNECT protocol. Default: do not use a proxy. |
HttpProxyPort
|
DWORD |
Port to connect to on http_proxy_host. Enter port number as decimal. Default: '80'.
|
If the Duo settings are managed by Windows Group Policy, those settings override any changes made via regedit. Update the "Duo Service: HTTP Proxy Hostname" and "Duo Service: HTTP Proxy Port" settings in the GPO instead.
If you do not already have an HTTP proxy deployed on your network you can use the Duo Authentication Proxy application to act as an HTTP proxy for Duo Windows Logon client connections. Install the Authentication Proxy on a server in your network that has direct internet access, add the HTTP proxy settings to the Authentication proxy configuration, and then update the Duo for Windows Logon proxy settings to point to that Authentication Proxy. See the HTTP Proxy instructions in the Authentication Proxy Reference for more information.
How do I allow smart card login instead of Duo Authentication?
Duo Authentication for Windows Logon v2.1.0 and later permits use of the Windows smart card login provider as an alternative to Duo. With this enabled, users may choose to log on with either the built-in Windows smart card authentication and a DOD CAC or other PIV card, or with Windows primary username and password credentials followed by Duo two-factor authentication.
You can turn on smart card login during a clean install of Duo for Windows Logon by selecting the "Enable Smart card support" option followed by selecting "Enable smart card login without Duo" in the installer.
To enable smart card support after upgrading or installing v2.1.0 or later, use the Registry Editor (regedit.exe) with administrator privileges to create or update the following registry value:
Location: HKLM\SOFTWARE\Duo Security\DuoCredProv:
| Registry Value | Type | Description |
|---|---|---|
EnableSmartCards
|
DWORD | Set to 1 to allow smart card login as an alternative to Duo. Default: 0. |
If the Duo settings are managed by Windows Group Policy, those settings override any changes made via regedit. Update the "Duo Service: Enable Smart Cards" setting in the GPO instead.
How do I enable smart card login plus Duo Authentication?
With Duo Authentication for Windows Logon v3.1.0 and later, you can require Duo two-factor authentication for smart card users logging in at the local console. When this is enabled, user may choose to log on with either the built-in Windows smart card authentication and a DOD CAC or other PIV card, or with Windows primary username and password credentials. Both smart card and username/password primary login is followed by Duo two-factor authentication.
You can turn on smart card login during a clean install of Duo for Windows Logon by selecting the "Enable Smart card support" option followed by selecting "Enable smart card login with Duo" in the installer.
To enable smart card + Duo support after upgrading or installing v3.1.0 or later, use the Registry Editor (regedit.exe) with administrator privileges to create (or update) both of the following registry values:
Location: HKLM\SOFTWARE\Duo Security\DuoCredProv:
| Registry Value | Type | Description |
|---|---|---|
EnableSmartCards
|
DWORD | Set to 1 to enable the smart card credential provider. This may already be done if you selected the "Enable Smart card support" option during installation. |
WrapSmartCards
|
DWORD | Set to 1 to require Duo authentication after logging in with the smart card credential provider. Default: 0. |
If the Duo settings are managed by Windows Group Policy, those settings override any changes made via regedit. Update the "Duo Service: Wrap Smart Cards" setting in the GPO instead.
Can I permit use of other credential providers after installing Duo?
Installing Duo disables all other installed logon credential providers. You can enable the Windows smart card login provider in the Duo installer, but other credential providers (what your users may refer to as "logon tiles") are hidden.
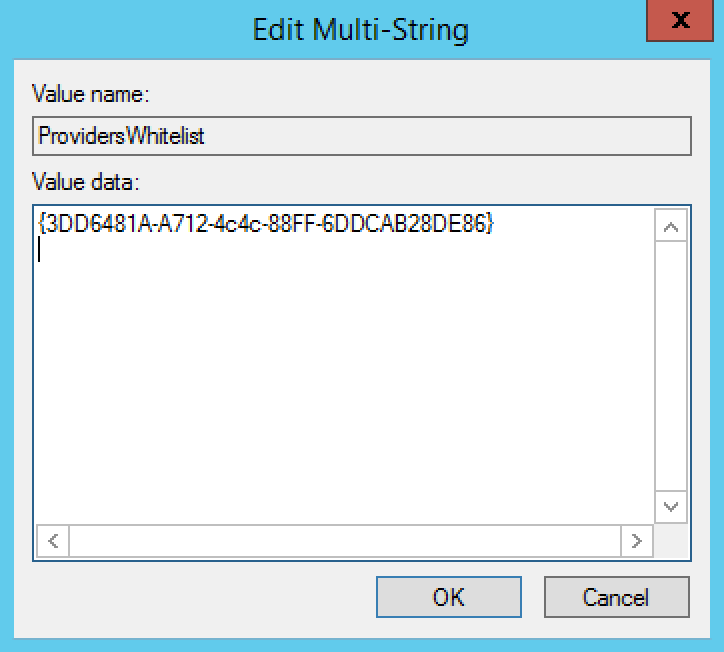
Duo Authentication for Windows Logon version 3.1 and later allows re-enabling access to a hidden credential provider via the registry. A common use case for this would be to restore access to a password reset tool from the Windows logon screen.
Be aware that any credential provider you allow in this registry value is accessible without Duo two-factor authentication! Users who log in with a credential provider in the ProvidersWhitelist skip Duo authentication entirely.
Use the Registry Editor (regedit.exe) with administrator privileges to create (or update) the following registry values:
Location: HKLM\SOFTWARE\Duo Security\DuoCredProv:
| Registry Value | Type | Description |
|---|---|---|
ProvidersWhitelist
|
REG_MULTI_SZ | Populate the multi string value data with the GUIDs of the third-party credential providers to allow. You can find GUIDs for all registered credential providers on a system in HKLM\Software\Microsoft\Windows\CurrentVersion\Authentication\Credential Providers, or contact the application's vendor for assistance determining the GUID for their credential provider. Supports multiple permitted GUIDs. |
Example registry value that permits the Microsoft FIM Password Reset client:
How many users can enroll in offline access with MFA per Windows client?
By default, five (5) users may enroll in offline access. To increase or reduce the number of users that may activate offline access on a given Windows client, use the Registry Editor (regedit.exe) with administrator privileges to create or update the following registry value:
Location: HKLM\SOFTWARE\Duo Security\DuoCredProv:
| Registry Value | Type | Description |
|---|---|---|
OfflineMaxUsers
|
DWORD | Create this value and set to the number of users you would like to have the ability to enroll in offline access on a given Windows system. Minimum value: 1; Maximum value: 50. If not set the default is 5. |
Once the maximum number of users have activated offline access, the next user receives an error when attempting to enroll in offline access.
How can I remove a user's existing offline activation?
To force offline reactivation for a previously activated user on a given Windows system, use the Registry Editor (regedit.exe) with administrator privileges to delete the entire registry key that includes the username from HKLM\SOFTWARE\Duo Security\DuoCredProv\Offline.
How can I completely prevent offline access with MFA at the Windows client?
You may have Windows systems where no users should log in using offline access, regardless of the application setting in the Duo Admin Panel. To prevent offline authentication for any user on a given Windows client, use the Registry Editor (regedit.exe) with administrator privileges to create or update the following registry value:
Location: HKLM\SOFTWARE\Duo Security\DuoCredProv:
| Registry Value | Type | Description |
|---|---|---|
OfflineAvailable
|
DWORD | Create this value and set to 0 to disable offline access for all users. Your fail mode configuration applies to offline logins (either fail open or fail closed). |
How do I enable and configure User Elevation to add Duo authentication to UAC prompts?
Available in version 4.1 and later, User Elevation adds Duo two-factor authentication to password-protected Windows UAC elevation attempts. By default. Duo UAC elevation protection is disabled. When enabled, Duo Authentication for Windows Logon will prompt for MFA on credentialed UAC elevation attempts.
You can enable and configure User Elevation during a clean install of Duo for Windows Logon by selecting the "Enable UAC Elevation Protection" option, followed by selecting your desired User Elevation configuration settings in the installer.
To enable and configure User Elevation after upgrading or installing v4.1.0 or later, use the Registry Editor (regedit.exe) with administrator privileges to create (or update) the following registry values:
Location: HKLM\SOFTWARE\Duo Security\DuoCredProv:
| Registry Value | Type | Description |
|---|---|---|
ElevationProtectionMode
|
DWORD | Create this value and set to 0 to disable UAC protection and only prompt for Duo 2FA at login, 1 to enable Duo only for UAC protection (no Duo 2FA at login) or 2 to enable Duo 2FA for both logon and UAC. Default: 0 |
ElevationOfflineEnable
|
DWORD |
Create this value and set to 0 to disable offline access for UAC elevation, or 1 to enable offline access for UAC elevation. Requires offline access enabled and ElevationProtectionMode set to 1 or 2. Default: 1
|
ElevationOfflineEnrollment
|
DWORD |
Create this value and set to 0 to disable enrollment in offline access during UAC elevation, or 1 to permit enrollment in offline access during UAC elevation. Requires offline access enabled and ElevationProtectionMode set to 1 or 2. Default: 1
|
How do I enable User Account Control credentialed elevation in Windows?
User Account Control (UAC) protects Windows systems and users from malicious software by prompting for additional approval before running an application with administrator privileges. Duo Authentication for Windows Logon v4.1.0 and later optionally adds two-factor authentication to password-protected UAC prompts. If you've enabled Duo User Elevation but you're only getting asked to approve UAC elevation requests ("Prompt for consent"), and aren't required to enter your Windows password to approve the elevation request, you won't be prompted for Duo when approving the UAC elevation request either.
You can configure User Account Control to require a password to approve elevation requests via registry edit or local/domain Group Policy.
To require password entry for UAC elevation with the Registry Editor, launch regedit.exe with administrator privileges to create (or update) the following registry values:
Location: HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System:
| Registry Value | Type | Description |
|---|---|---|
ConsentPromptBehaviorAdmin
|
DWORD | Create this value and set to 1 to prompt administrators for credentials on the secure desktop (recommended), or 3 to prompt administrators for credentials on the interactive desktop. |
ConsentPromptBehaviorUser
|
DWORD | Create this value and set to 1 to prompt standard users for credentials on the secure desktop (recommended), or 3 to prompt standard users for credentials on the interactive desktop. |
To require password entry for UAC elevation with Group Policy, enable the following policy settings with Group Policy Management Console (gpmc.msc) or local Group Policy Editor (gpedit.msc):
Location: Computer Configuration\Policies\Windows Settings\Security Settings\Local Policies\Security Options
| Policy Setting | Description |
|---|---|
| User Account Control: Behavior of the elevation prompt for administrators in Admin Approval Mode | Set to Prompt for credentials on the secure desktop or Prompt for credentials. |
| User Account Control: Behavior of the elevation prompt for standard users | Set to Prompt for credentials on the secure desktop or Prompt for credentials. |
Please refer to User Account Control Group Policy and registry key settings for additional information about UAC settings.
How do I enable remembered devices for Windows Logon?
Duo Essentials, Advantage, and Premier customers can apply a remembered devices policy to their Microsoft RDP Duo applications with the Remember devices for Windows Logon setting enabled and set to the number of hours or days desired.
Duo Authentication for Windows Logon version 4.2.0 and later will apply this policy setting to online authentications at the local console, offering the "Remember me" option in the prompt.
Earlier versions of Duo Authentication for Windows Logon must be upgraded to v4.2.0 or later to use this feature.
What logging is available for device authentication during a trusted session?
Duo records logins authenticated as a local trusted session in the Admin Panel Authentication Log with "Remembered Device" as the second factor. The local Windows Logon client log, found at %PROGRAMDATA%\Duo Security\duo.log, also shows the authentication type for the logon activity as a "Remembered Device".
Troubleshooting
Using the Support Tool
If you open a case with Duo Support for an issue involving Duo Authentication for Windows Logon (RDP), your support engineer will need you to submit your registry configuration, recent debug log output demonstrating the issue, and other system configurations. Sensitive information, such as your Duo application's SKEY, should not be sent to support.
We've made collecting troubleshooting information easy with a script that gathers all the necessary files, scrubs them of sensitive information, and creates a zip package ready for you to send to Duo Support. The script is included in version 4.0.6 and later at C:\Program Files\Duo Security\WindowsLogon\Winlogon-Diag.ps1, but for the best results we recommend downloading the most recent version of the script if your local copy is an older version.
Obtain the most recent version of the Support Tool here:
https://dl.duosecurity.com/Winlogon-Diag.ps1
Version 0.8 released 6/30/25
SHA-256 checksum: 8d7cb479001ac157424517f690f6061769a98095c5f9faecc69126d9f5dfaa6b
The support tool performs the following actions:
- Runs
Invoke-Webrequestto determine if a connection to Duo is available. - Creates a zip file that contains all of the collected information.
- Captures the following information:
- Installed version and if it is deployed with GPO configuration.
- Debug status.
- Host information to DuoSupport.log:
- Hostname
- Username
- Domain
- System/Browser proxy settings
- Operating system version, build and bit
- Bitlocker status
- AV product
- TPM availability
- Timezone
- Exports list of all credential providers and filter from registry to
credprov.txtin zip file. - Copies
C:\ProgramData\Duo Security\duo.logto zip file. - Exports Duo Registry keys from
HKLM\Software\Duo Security\DuoCredProvtoDuoSupport.login zip file (excluding your SKEY). - Exports Duo Offline Registry keys from
HKLM\Software\Duo Security\DuoCredProv\OfflinetoDuoSupport.login zip file. - Optional: Export Application and/or Security Event logs to zip file.
- Saves the zip file to the current CMD location or chosen directory as
DuoSupport-year-month-date-time.zip.- For example: On Windows, the support file would be
C:\SupportScript\DuoSupport2019-06-06-04-28-17.zip.
- For example: On Windows, the support file would be
Additional PowerShell command options
| Setting | Description |
|---|---|
-duodebug |
Default is off; $true only enables debug in registry; $false only disables debug in registry. |
-rename |
Default is off; $true renames existing logs; $false does not rename the logs. |
-out |
Sets the preferred log path; defaults to Desktop if not set. |
-eventlogs |
Exports application and/or security logs. Options: all, application, security. |
-days |
Defines a selected number of days to export from both Duo native logs and event logs. |
-tls |
Exports Client TLS settings from registry. |
Running the Support Tool
Here's an example of how you can use the Support Tool. In this example, debug is enabled, and security event logs from the last two days are exported.
-
Open an administrative PowerShell command-line session on the system where Duo is installed. The prompt will show
PSto indicate it is a PowerShell session, likePS C:\>. -
Enable debug.
.\Winlogon-Diag.ps1 -duodebug $true -
Reproduce the Duo issue you are experiencing.
-
Run a script to export the logs:
.\Winlogon-Diag.ps1 -out C:\testing\ -eventlogs security -days 2 -
Disable debug:
.\Winlogon-Diag.ps1 -duodebug $false
Why am I unable to log in to Windows after installing Duo?
In order for the Duo service to properly authenticate a Windows user account, the username in Windows must match the username or a username alias in the Duo account. If you receive a message like "The Duo native Windows client does not currently support unknown users", "The username you have entered is not enrolled with Duo Security", or "Access is not allowed because you are not enrolled in Duo.", then the account you are using to log into Windows does not match an enrolled Duo user.
- Log in to the Duo Admin Panel and make sure that you've added a user with a username that matches the Windows username.
- You will also need to manually enroll this user's phone number so that the user can receive passcodes or phone calls, which are needed in order to authenticate.
- Once the user's phone number has been added you may optionally install and enroll the Duo Mobile smartphone app, which will enable the "push" functionality for an RDP login.
- Now try to log in to Windows again.
If you receive the message "Unknown devices are not permitted by your administrator" then a Duo policy may be restricting your Windows system or 2FA approval device.
Please review your global policy, as well as any policies associated with your "RDP" application in the Duo Admin Panel. Commonly, issues occur with application or global policies that restrict allowed authentication methods or restrict operating systems by blocking access from Windows or specific Windows versions.
Users receive the error "Logon failure: the user has not been granted the requested logon type at this computer" when attempting to log in.
This error may be seen in Duo Windows Logon version 1.1.5 or later. Ensure that the users have been delegated the "Allow log on locally" rights for console logins, or have been delegated both the "Allow log on locally" and "Allow log on through Remote Desktop Connection" rights in the computer's local or domain-level security policy. Please see the Group Policy Settings Reference for Windows and Windows Server for more information about these user rights assignments.
When logging in via Remote Desktop, my authentication is accepted but the Remote Desktop session is disconnected. How do I fix this?
You can increase the logon timeout if extra time is needed to complete authentication (for example, if users must type in a hardware token passcode). Create a new registry DWORD value HKLM\SYSTEM\CurrentControlSet\Control\Terminal Server\WinStations\RDP-Tcp\LogonTimeout and set it to a decimal value greater than 60. You may need to cycle the TermService service or restart Windows recognize the change.
To increase the Remote Desktop logon timeout for multiple computers joined to an Active Directory domain with Group Policy, add the HKLM\SYSTEM\CurrentControlSet\Control\Terminal Server\WinStations\RDP-Tcp\LogonTimeout value to a GPO (Group Policy object) as a registry preference item. Please see "Configure a Registry Item" at the Microsoft TechNet site for more information.
Why is Passwordless OS Logon not restricted to only the groups I selected in the Passwordless configuration?
Group restrictions for Passwordless OS Logon were not supported in the 4.3.16 public beta release. Update to Duo for Windows Logon version 5.0.0 or later.
Additional Troubleshooting
Need more help? Try searching our Windows Logon Knowledge Base articles or Community discussions. For further assistance, contact Support.
