Duo Authentication for Epic - FAQ
Last updated:
Is it possible to use the Duo Universal Prompt for Epic Hyperdrive authentication?
Yes, this feature is available for evaluation in the Duo Authentication for Epic Hyperdrive with Duo Universal Prompt Beta.
Does Duo Support Epic Hyperdrive?
Yes, with the October 2022 release of Duo Epic for Hyperdrive. Epic asks its customers to migrate from Hyperspace to Hyperdrive by their November 2023 release.
What Hyperspace versions does Duo support?
Duo Authentication for Epic is compatible with Hyperspace versions 2010 through the current release. Contact Epic technical support for assistance configuring Duo in your installed version.
Which Windows versions does Duo Authentication for Epic support?
Duo Authentication for Epic Hyperspace and Hyperdrive is supported on Windows 10 and later desktop clients, and Windows Server 2016 and later.
Microsoft end-of-support information for these Windows systems is as follows:
- Windows Server 2008 and 2008 R2 extended support ended on January 14, 2020
- Windows Vista extended support ended on April 11, 2017
- Windows 7 extended support ended on January 14, 2020
- Windows 8 extended support ended on January 12, 2016
- Windows 8.1 extended support ended on January 10. 2023
Duo's last day of support for installation and use of any Duo applications on Windows operating systems corresponds with the Microsoft end of support. We strongly urge you to upgrade to a supported version of Windows. Duo no longer supports installation of any Duo applications on these operating systems. We strongly urge you to upgrade to a supported version of Windows.
Does Duo Authentication for Epic protect initial Hyperspace client logons?
No, Duo Authentication for Epic may only be used for workflows that require reauthentication after completing Hyperspace client logon, like EPCS workflows.
Can I protect Epic mobile apps?
Yes, Duo Single Sign-On can protect access to Epic's Haiku, Canto, and Rover mobile applications. See the Duo Single Sign-On for Epic Mobile Apps documentation.
Can I configure Duo Authentication for Epic to fail open?
The "fail mode" determines whether users may or may not log into a protected application when the Duo cloud service is unreachable. Duo Authentication for Epic will always "fail closed" if it is unable to contact the Duo service. This means that users can not complete the EPCS authorization flow in Epic without successful Duo two-factor authentication. This setting is not configurable.
Why do I receive an error message during EPCS authentication stating that the application does not support unknown users?
The user attempting to authentication with Duo for Epic is not enrolled in Duo with a two-factor device. Duo Authentication for Epic doesn't support inline self-enrollment. Enroll your users in Duo ahead of time using directory synchronization, CSV import, or another enrollment method.
Additionally, Duo Authentication for Epic sends the Epic application username as the Duo username by default. If your users are enrolled in Duo under their Windows usernames (and these do not match the Epic usernames) you can either add your Epic usernames to existing Duo users as username aliases, or use Group Policy to change the "Client: Duo Username Source" setting from the Epic username to the Windows username.
Can I do a scripted install of Duo Authentication for Epic?
Yes, after downloading the msi install file enter the following command into PowerShell or add to a script to silently install Duo for Epic.
cmd.exe /c DuoEpic.msi DUO_IKEY=Integration Key DUO_SKEY=Secret Key DUO_HOST=API Hostname
cmd.exe /c DuoEpicHyperdrive.msi DUO_IKEY=Integration Key DUO_SKEY=Secret Key DUO_HOST=API Hostname
How do I enable Duo debug logging on a single Epic client without using a group policy object (GPO)?
Perform the following steps on the system where the Epic Hyperspace client and Duo Authentication for Epic are installed.
- Close and exit the Epic client.
- As an administrator, launch the Registry Editor (regedit.exe).
- Locate the Duo Epic registry values at HKLM\Software\Policies\Duo Security\Epic or HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Duo Security\Duo Epic Hyperdrive or HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432\Policies\Duo Security\Duo Epic Hyperdrive depending on the product you installed and the platform of the client computer.
- Create a new DWORD value named EpicEnableDebugLogging set to 1.
- Reopen the Epic client and attempt Duo authentication.
- View the resulting debug file "DuoEpic.log" or "DuoEpicHyperdrive.log" in the current user's %TEMP% directory (e.g. C:\Users\DuoUser\AppData\Local\Temp\DuoEpic.log).
Can I publish the Duo Authentication for Epic to clients using Active Directory?
Yes, the Duo Authentication for Epic clients may be deployed via a Group Policy software installation package.
First, create a transform for the installer file by using a table editor tool like Orca. Open the DuoEpic.msi or DuoEpicHyperdrive.msi file in the editor, click on the Property table, and add these new rows using your Epic application's information from the Duo Admin Panel:
| Property | Value |
|---|---|
| DUO_IKEY | Your Duo integration key |
| DUO_SKEY | Your Duo secret key |
| DUO_HOST | API hostname |

Save the transform as an MST file and copy that transform along with the DuoEpic.msi or DuoEpicHyperdrive.msi installer to your application deployment repository. The share with the MST file should not be readable by unprivileged user accounts to prevent exposure of the Duo secret key.
In the Group Policy Management console, create a new GPO for Duo Epic publishing. Navigate to Computer Configuration\Policies\Software Settings\Software installation then right-click and select New > Package.
Select the network accessible DuoEpic.msi or DuoEpicHyperdrive.msi installer package and choose Advanced as the deployment method. In the properties window go to the Modifications tab. Click the Add button and select the MST transform you created earlier. Click OK to finish, and the Duo Authentication for Epic software package is created.
Here's a sample software publishing policy for Duo Authentication for Epic.
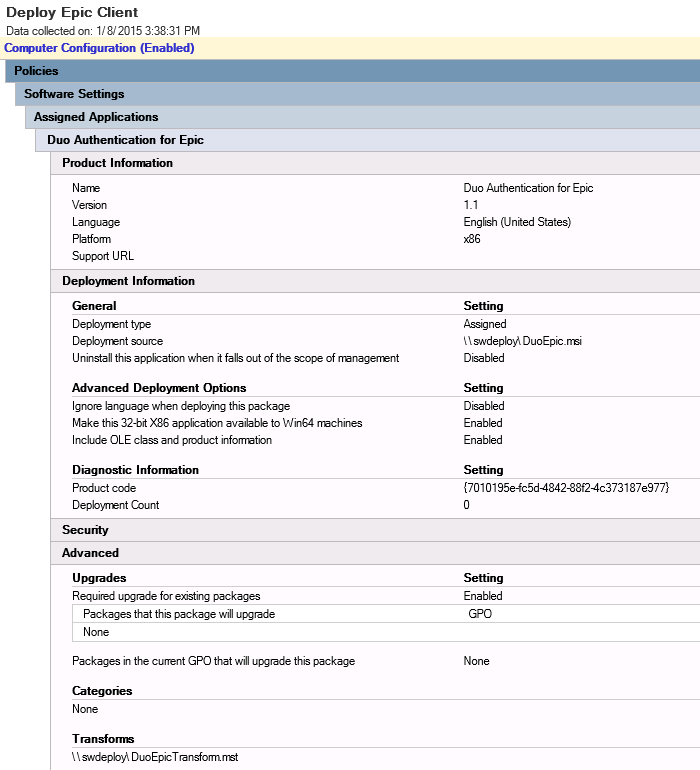
Learn more about installing software using Group Policy at Microsoft Support.
Additional Troubleshooting
Need more help? Try searching our Epic Knowledge Base articles or Community discussions. For further assistance, contact Support.
