Duo Access Gateway with Remembered Devices
Last updated:
Duo Access Gateway reached Last Day of Support on October 26, 2023 for Duo Essentials, Advantage, and Premier customers. As of that date, Duo Support may only assist with the migration of existing Duo Access Gateway applications to Duo Single Sign-On. Please see the Guide to Duo Access Gateway end of life for more details.
Learn more about Duo Single Sign-On, our cloud-hosted identity provider featuring Duo Central and the Duo Universal Prompt.
Duo Federal customers may still use Duo Access Gateway for SAML applications after October 26, 2023.
Overview
Duo Access Gateway secures access to cloud applications with your users’ existing directory credentials (like Microsoft Active Directory or Google Workspace accounts) using the Security Assertion Markup Language (SAML) 2.0 authentication standard. SAML delegates authentication from a service provider to an identity provider, and is used for single sign-on solutions (SSO).
Duo Access Gateway combined with Remembered Devices allows you to minimize additional two-factor authentication prompts after primary SSO. Using the robust Policy & Control engine, you can create policies tailored to your SAML applications allowing for SSO between certain applications while still requiring that more sensitive applications prompt the user for two-factor authentication again.
The Duo Premier, Duo Advantage, and Duo Essentials plans include Duo Access Gateway.
Video Overview
Prerequisites
Before you can configure the Duo Access Gateway with Remembered Devices you must complete the following prerequisites:
-
Successfully deploy the Duo Access Gateway for Linux] or Duo Access Gateway for Windows with an authentication source and protect your cloud applications.
If you're already running Duo Access Gateway for Windows v1.2.1 or earlier, you'll need to upgrade to version 1.3 with a 64-bit install of PHP 7 to use the new Launcher and SSO features. See the Windows upgrade instructions for details.
-
Enable the Duo Access Gateway Launcher to allow users to access their cloud applications from one convenient location.
Create a New Policy for Cloud Applications
Create a new policy in the Duo Admin Panel enabling Remembered Devices.
-
Log into the Duo Admin Panel and navigate to Policies.
-
On the "Policies" page scroll down to the "Custom Policies" section. Click the + Create New Policy button. A new window will appear with the policy builder.
-
In the Policy Name field name the policy something that easily identifies what the policy is for, such as "Cloud SSO".
-
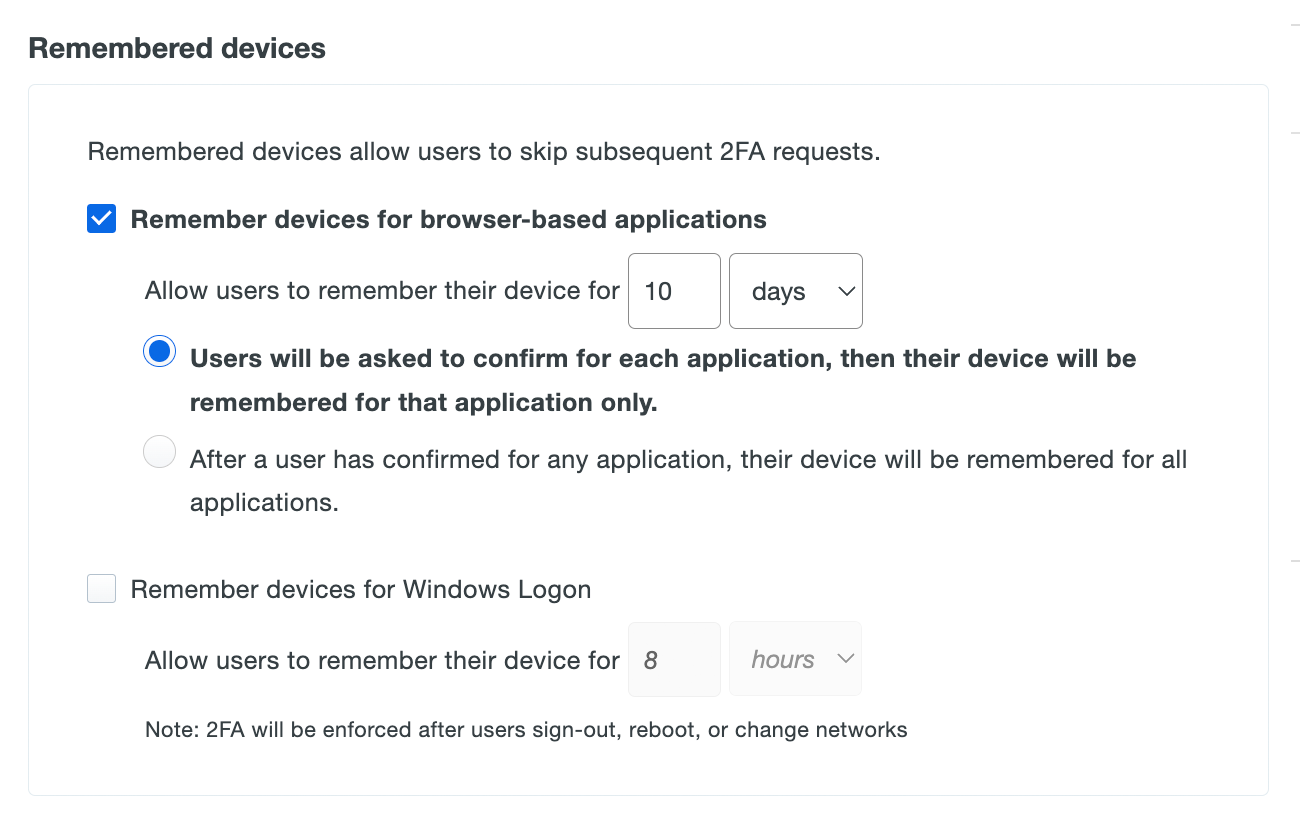
Click on Remembered Devices located under the "Devices" section in the policy builder. A "Remembered Devices" section will be added to your policy.
-
Select Remember devices for browser-based applications and choose the amount of time in days or hours that you'd like to allow the policy to trust an authenticated device. When a device is trusted, the Duo Prompt will not require additional two-factor authentication for a user who has already successfully 2FA'd on that same device within that time period.
-
Select Users will be asked to confirm for each application, then their device will be remembered for that application only. to enable single sign-on functionality. All applications that have this policy linked to them will experience SSO after the initial two-factor authentication is completed successfully.
-
You can add & configure additional policy options to tailor this policy to your needs.
-
Once you've configured your policy, click Create Policy.
Assign the Remembered Devices Policy to Applications
Once you've configured a policy with Remembered Devices "for all protected web applications", apply that policy to the applications where you want to let your end users skip additional Duo prompts after the first successful 2FA login.
-
While logged into the Duo Admin Panel navigate to Applications → Applications.
-
Locate and click on the Duo Access Gateway application, which is Access Gateway Launcher application. If you cannot find an application with the type "Duo Access Gateway" please make sure you've completed all the prerequisites listed above.
-
Once you are on the "Duo Access Gateway" application page, scroll down to the "Policy" section and click Add a policy to all users next to "Application policy".
-
When the "Apply a Policy" screen appears select the name of your new policy from the drop-down. Once the policy is selected click Apply Policy.
-
The page reloads and shows your Remembered Devices policy applied under "Application policy".
-
Repeat these steps with additional SSO applications where you want to minimize Duo prompts for authentication. If you want to ensure an application always requires Duo approval before access, do not attach this policy to that application.
See Remembered Devices in the Policy documentation for more information about the available options.
Verify Application Policy
Access the applications now using the shared Remembered Devices policy. When configured correctly, the first application accessed (which may be the Launcher itself) requires Duo approval, and any other application linked to the same Remembered Devices policy won't show additional Duo prompts.
-
Navigate to your Duo Access Gateway Launcher page; this is the base URL of your DAG server. This redirects to the Duo Access Gateway login page. Enter your primary directory logon information.
-
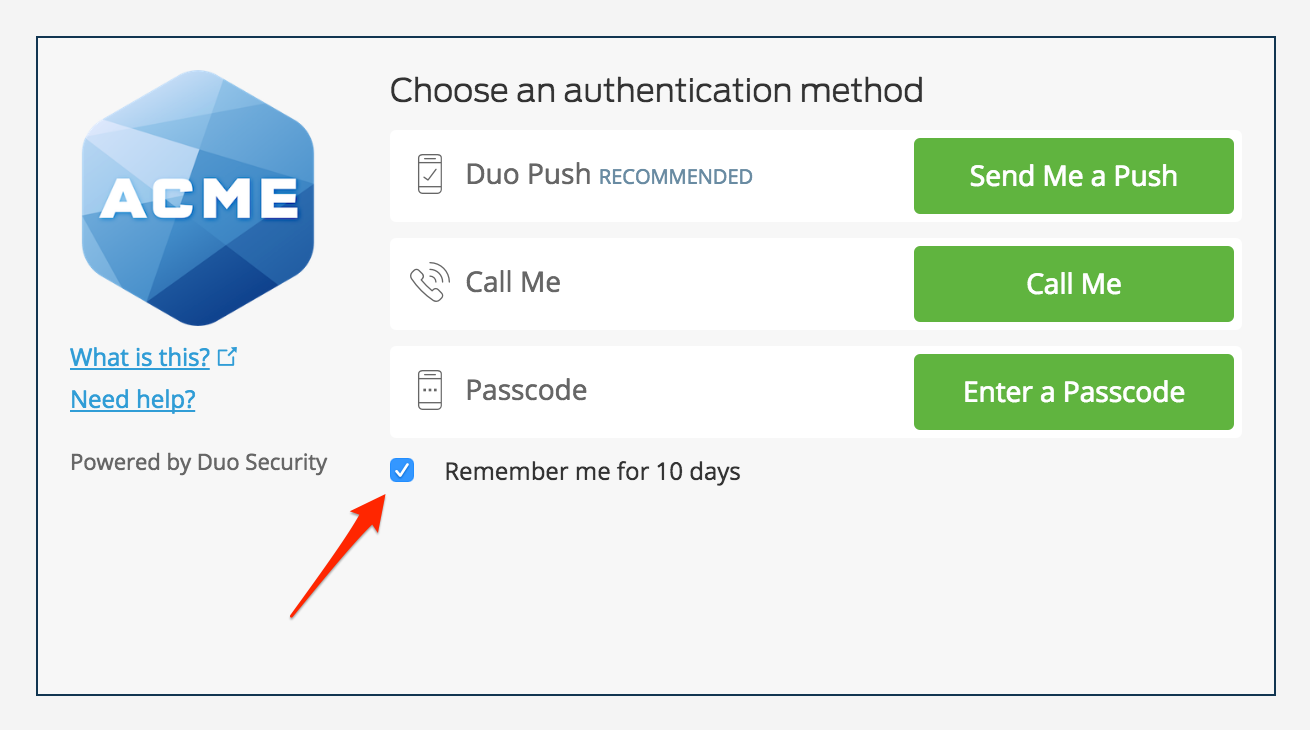
After you've successfully authenticated with your primary credentials you will be directed to the Duo Prompt to complete two-factor authentication. Check the Remember me box near the bottom of the Duo Prompt to trust your device for all applications sharing the SSO policy. Complete two-factor authentication to log into the Duo Access Gateway Launcher.
-
While logged into the Duo Access Gateway Launcher, click on any cloud applications that also have the shared Remembered Devices policy applied. The applications open in new tabs and you will be automatically logged into your cloud applications without an additional Duo prompt.
If you log into an application that doesn't have a remembered devices policy set to apply to all applications linked, you'll need to perform Duo authentication again before accessing that application. If you have two sets of applications with different Remembered Devices policies linked (i.e. Remembered Devices Policy A attached to Application A, and Remembered Devices Policy B attached to Application B) then selecting the "Remember Me" option for Application A doesn't skip Duo Authentication for Application B, and selecting "Remember Me" when logging into Application B invalidates the previously saved session for Application A. Then next time you access Application A you'll need to approve Duo 2FA again.
Troubleshooting
Need some help? Try searching our Knowledge Base articles or Community discussions. For further assistance, contact Support.
