Directory Sync - Troubleshooting and FAQ
Last updated:
Will passwords be imported from external directories into Duo?
No, Duo does not import passwords from external directories.
How often does user directory sync run?
Duo's directory sync for users runs automatically twice a day, at 12 hour intervals chosen at random when you create your sync. You can opt into a high-frequency sync schedule from the details page of a given directory sync, which will start the next sync about 30 minutes after the previous process ends.
Scheduled synchronization ran once every 24 hours prior to March 10, 2022.
You can run a full sync at any time by visiting your user directory sync's properties page in the Duo Admin Panel and clicking the Sync Now button.
Sync an individual user from the same directory sync by entering their username value from the source directory in the Sync Individual Users field on the directory sync's properties page and then clicking Sync User.
External directories that use SCIM integrations push updates to Duo when information changes in the directory.
How often does admin directory sync run?
Duo's directory sync for admins runs automatically every 30 minutes.
You can run a full sync at any time by visiting your admin directory sync's properties page in the Duo Admin Panel and clicking the Sync Now button.
Sync an individual admin from the same directory sync by entering their admin email address value from the source directory in the Sync individual admins field on the admin directory sync's properties page and then clicking Sync User.
Does the Duo service need to be able to contact my on-premises directory servers?
No, Duo's service does not need to directly contact your directory servers. When you configure Active Directory or OpenLDAP sync for users or admins, the Duo Authentication Proxy server you configure contacts your directory server to search for information about users and groups, and also makes an outbound connection to Duo's service to send the user and group information to perform the sync.
Can I use a Linux Duo Authentication Proxy for Active Directory Sync?
Yes, you can use a Linux server to sync Active Directory domains when you specify NTLMv2 or Plain authentication when setting up directory sync for users or admins. See the AD Sync instructions for more information.
Can I use a single Duo Authentication Proxy to run more than one directory sync?
Yes. You must have Authentication Proxy v5.2.0 or later installed. To run multiple syncs through a single proxy server, all the syncs must be configured for a single Duo customer account, i.e. the api_host value for all the directory syncs is identical.
Here is an authproxy.cfg example for multiple directory syncs using Integrated (SSPI) authentication. Note that the integration key (ikey) differs but the API host is the same in both [cloud] sections; this reflects the requirement that the multiple syncs must be for a single Duo customer account:
[cloud]
ikey=DIABCDEFGHIJKLMNOPQR
skey=XXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXX
api_host=api-12345678.duosecurity.com
[cloud2]
ikey=DISTUVWXYZABCDEFGHIJ
skey=XXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXX
api_host=api-12345678.duosecurity.comAuthentication Proxy versions up to v5.1.1 can only run a single directory sync. Adding more than one [cloud] section to authproxy.cfg prevents the proxy service from starting due to this being an invalid configuration.
Can I import admins, users, and groups from Active Directory Lightweight Directory Services?
Yes, Duo supports importing admins, users, and groups from Active Directory Lightweight Directory Services (AD LDS) via Active Directory sync. Imported groups must be local to AD LDS, but the users may be either local to AD LDS or proxied from an underlying AD domain (with objectClass=userProxyFull).
What Active Directory attributes are synchronized to Duo?
The following table lists the default Active Directory attributes synchronized to Duo during user sync, along with their corresponding Duo attribute mappings:
| AD Attribute | Duo Attribute |
|---|---|
| CN | Group name |
| sAMAccountName | Username |
| displayName | User full name |
| User email address | |
| telephoneNumber | Phone (type Mobile, platform Generic Smartphone) ** |
| mobile | Phone (type Mobile, platform Generic Smartphone) ** |
| info | Notes ** |
*Not synced unless the "Import phones" option is checked.
** Not synced unless the "Import notes" option is checked.
The Active Directory user attributes synchronized to Duo can be changed using custom attribute mapping.
Username aliases aren't imported unless you specify a source attribute; there are no default alias attributes. Username alias attribute values must be unique throughout the synced directory. If the sync process encounters an alias value that's already attached to another Duo user, then it skips updating properties of the user with the duplicated alias value (but will update that user's group memberships).
These are the default Active Directory attributes synchronized to Duo during admin sync and their Duo attribute mappings:
| AD Attribute | Duo Attribute |
|---|---|
| displayName | User full name |
| User email address | |
| telephoneNumber | Phone (type Mobile, platform Generic Smartphone) * |
*Not synced unless the "Import phones" option is checked.
Imported values may not be changed from the Duo Admin Panel. To update any of the imported values, change the source attribute value in your directory and perform a sync. See How are synced users affected if I change the values of certain user attributes in Active Directory? for more information about updating synced attributes. You can edit user properties that aren't imported from the source directory, but if you add those attributes to the sync later, the information you added manually gets overwritten with information imported by AD sync.
Add more attributes to your sync configuration and map them to external directory attributes with user attributes.
What OpenLDAP attributes are synchronized to Duo?
There are no default source attributes for OpenLDAP sync. You must specify which directory attribute to use for each Duo user and associated phone property.
The following table lists the Duo properties that may be imported from OpenLDAP attributes for users:
| Duo Attribute |
|---|
| Group name |
| Username |
| User full name |
| User email address |
| Phone 1* (type Mobile, platform Generic Smartphone) |
| Phone 2* (type Mobile, platform Generic Smartphone) |
| Notes** |
*Not synced unless the "Import phones" option is checked and source attribute specified.
** Not synced unless the "Import notes" option is checked and source attribute specified.
Username aliases aren't imported unless you specify a source attribute. Username alias attribute values must be unique throughout the synced directory. If the sync process encounters an alias value that's already attached to another Duo user, then it skips updating properties of the user with the duplicated alias value (but will update that user's group memberships).
These are the Duo properties that may be imported from OpenLDAP for admins:
| Duo Attribute |
|---|
| User full name |
| User email address |
| Phone 1* (type Mobile, platform Generic Smartphone) |
*Not synced unless the "Import phones" option is checked and source attribute specified.
Imported values may not be changed from the Duo Admin Panel. To update any of the imported values, change the source attribute value in your directory and perform a sync. See How are synced users affected if I change the values of certain user attributes in OpenLDAP? for more information about updating synced attributes. You can edit user properties that aren't imported from the source directory, but if you add those attributes to the sync later, the information you added manually gets overwritten with information imported by OpenLDAP sync.
Add more attributes to your sync configuration and map them to external directory attributes with user attributes.
What Entra ID directory attributes are synchronized to Duo?
The following table lists the default Entra ID attributes synchronized to Duo during user sync, along with their corresponding Duo attribute mappings:
| Entra ID Attribute | Duo Attribute |
|---|---|
| CN | Group name |
| userPrincipalName | Username * |
| displayName | User full name |
| User email address | |
| businessPhone | Phone (type Mobile, platform Generic Smartphone) ** |
| mobilePhone | Phone (type Mobile, platform Generic Smartphone) ** |
* Duo username created as the full userPrincipalName ("narroway@example.onmicrosoft.com") or as the unique username without domain information ("narroway") depending on whether "Normalize usernames" is checked.
** Not synced unless the "Import phones" option is checked.
The Entra ID attributes synchronized to Duo can be changed in the directory's synced attributes configuration.
Username aliases and notes aren't imported unless you specify a source attribute; there are no default alias attributes. Username alias attribute values must be unique throughout the synced directory. If the sync process encounters an alias value that's already attached to another Duo user, then it skips updating properties of the user with the duplicated alias value (but will update that user's group memberships).
These are the default Entra ID attributes synchronized to Duo during admin sync and their Duo attribute mappings:
| Entra ID Attribute | Duo Attribute |
|---|---|
| displayName | User full name |
| User email address | |
| businessPhone | Phone (type Mobile, platform Generic Smartphone) ** |
Imported values may not be changed from the Duo Admin Panel. To update any of the imported values, change the source attribute value in your directory and perform a sync. See How are synced users affected if I change the values of certain user attributes in Entra ID? for more information about updating synced attributes. You can edit user properties that aren't imported from the source directory, but if you add those attributes to the sync later, the information you added manually gets overwritten with information imported by Entra ID sync.
Add more attributes to your sync configuration and map them to external directory attributes with user attributes.
What Google directory attributes are synchronized to Duo?
The following table lists the default Google attributes synchronized to Duo during user sync, along with their corresponding Duo attribute mappings:
| Google Attribute | Duo Attribute |
|---|---|
| name | Group name |
| primaryEmail | Username |
| fullName | User full name |
| givenName | First name |
| familyName | Last name |
| primaryEmail | User email address |
| phones/*/value | Phone (type Mobile, platform Generic Smartphone) ** |
** Not synced unless the "Import phones" option is checked.
The Google attributes synchronized to Duo can be changed in the directory's synced attributes configuration.
Username aliases and notes aren't imported unless you specify a source attribute; there are no default alias attributes. Username alias attribute values must be unique throughout the synced directory. If the sync process encounters an alias value that's already attached to another Duo user, then it skips updating properties of the user with the duplicated alias value (but will update that user's group memberships).
These are the default Google attributes synchronized to Duo during admin sync and their Duo attribute mappings:
| Google Attribute | Duo Attribute |
|---|---|
| fullName | User full name |
| primaryEmail | User email address |
| phones/*/value | Phone (type Mobile, platform Generic Smartphone) |
Imported values may not be changed from the Duo Admin Panel. To update any of the imported values, change the source attribute value in your directory and perform a sync. You can edit user properties that aren't imported from the source directory, but if you add those attributes to the sync later, the information you added manually gets overwritten with information imported.
Add more attributes to your sync configuration and map them to external directory attributes with user attributes.
What Okta directory attributes are imported to Duo?
The following table lists the default Okta attributes imported to Duo via SCIM, along with their corresponding Duo attribute mappings:
| Okta Attribute | Duo Attribute |
|---|---|
| displayName | Group name |
| userName | Username |
| displayName | Display name |
| givenName | First name |
| familyName | Last name |
| User email address | |
| phoneNumbers | Phone (type Mobile, platform Generic Smartphone) ** |
** Not synced unless the "Import phones" option is checked.
The Okta attributes imported to Duo can be changed in the directory's attribute mapping configuration.
Username aliases and notes aren't imported unless you specify a source attribute; there are no default alias attributes. Username alias attribute values must be unique throughout the synced directory. If the sync process encounters an alias value that's already attached to another Duo user, then it skips updating properties of the user with the duplicated alias value (but will update that user's group memberships).
Imported values may not be changed from the Duo Admin Panel. To update any of the imported values, change the source attribute value in your directory and perform a sync. You can edit user properties that aren't imported from the source directory, but if you add those attributes to the sync later, the information you added manually gets overwritten with information imported.
Add more attributes to your sync configuration and map them to external directory attributes with user attributes.
Can you customize the Entra ID attributes imported into Duo?
Yes, when creating a new Entra ID directory sync for users or admins you can modify the synced attributes for user sync or admin sync.
Note that you cannot modify the Duo username source attribute after the first user Entra ID sync runs, but you can specify up to four source attributes for username aliases.
Similarly, you may not change the Duo email source attribute after the first admin Entra ID sync runs.
What happens when existing Duo users are synced with external directories?
The Duo user cannot be deleted manually from the Admin Panel, with the Admin API, or via CSV import. User attributes imported from the source directory become read-only and can only be updated in the source directory.
Directory synchronization overwrites information for any required or specified optional attribute, such as full name, email address, and username aliases, for any Duo user with a matching username in the external directory. The sync doesn't modify or remove information for attributes that aren't configured in the sync. Additionally, you can edit the values for optional custom attributes not configured in your sync (like aliases and notes), manually from the Admin Panel, programmatically via Admin API, or by CSV import.
Any phones or tokens that were attached to the Duo user before the directory sync remain intact. Phone numbers imported from the source directory are attached to the user as additional phones.
The user's Duo group memberships are updated to match the user's group memberships in the source directory. Groups managed by directory sync are identified as such when viewed (the group's description notes the type and name of the sync managing the group i.e. from Entra ID Sync "Acme"). The user cannot be manually added to any groups from the Duo Admin Panel, with Admin API, or via CSV import.
Policy settings and user access based on the user's previous Duo group memberships no longer apply if the sync removes a user from the policy's target groups. Apply the Duo policies and user access config to the groups managed by directory sync to maintain the configuration previously applied to the users before the sync.
Can I sync multiple directories into Duo?
Yes, you can configure multiple syncs with different source directories of any type and import all those users and groups into Duo. If you do this, ensure that the users you select for import have unique names.
If the same username exists in two different sync directory sources, the first sync you create will create or manage the user. Subsequent syncs with the same username get a sync error preventing the sync from affecting those users with the message "Cannot sync a user belonging to another directory sync unless that sync is paused". You can view the error in the Administrator Actions report for that sync's "completed" event. This error only affects the user in question; it doesn’t halt the sync.
If you want a different sync to be allowed to manage those users (for example to migrate users from one sync to another), you will need to pause the automatic scheduled syncs on the directory sync which currently manages those users.
If you were to configure both an AD and an Entra ID sync to import a group with the same name — for example, "Duo Users" — then each sync will create a "Duo Users" group in Duo, identified in the group's description by which sync manages it. Each sync populates the group it manages with the members from that source directory, so the "Duo Users" group managed by Entra ID sync would contain only members synced from that Entra ID directory, and the "Duo Users" group managed by AD sync would only contain members synced from that AD directory. There is no support for merging of users from different source directories into a single Duo group.
If you create more than one directory sync with the same source directory, and configure them to sync the same group from that directory, the first sync you create will take over management of the user. Additional syncs will not take over management of the user or group. We do not recommend this.
Why are no Active Directory users imported when Directory Sync runs?
User import via AD sync can fail for a few possible reasons, even when the directory status is "Connected":
-
The base DN used to configure Active Directory sync does not include any user accounts. The base DN specified should be at a level above all the organizational units or containers that hold users and groups you want to synchronize with Duo. You may find it easiest to set this to the top level of your domain.
-
If syncing groups via the global catalog that reside in a child domain of a multi-domain forest, set the child AD group scope to Universal.
-
The Domain Users group (or any group that is set as the primary group for one or more users) cannot be used by directory sync to import users. Please create another domain group that is not any user's primary group to use with the sync.
-
If there are any duplicate values in the attributes that are being synchronized to Duo, usernames and user aliases must be unique. For example, user 'jsmith' is being imported in a sync that has specified Username Alias 1 to be the userPrincipalName attribute (jsmith@example.com) and Username Alias 2 to be the mail attribute (jsmith@example.com). Since the values of these two username aliases are identical, the user will not be included in the sync.
-
If an outdated version of the Duo Authentication Proxy is being used, the minimum Authentication Proxy version for Active Directory synchronization using Integrated authentication is 2.4.9, but we recommend installing or updating to the latest version. The minimum Authentication Proxy version for Active Directory synchronization using NTLMv1/v2 or Plain authentication is 2.6.0.
-
The machine account of the Authentication Proxy server lacks sufficient privileges to query Active Directory and retrieve user attributes. Try changing the "Log on as:" setting of the "Duo Security Authentication Proxy Service" to use a domain service account. You can do this from the Services management console (services.msc).
- View the properties of the "Duo Security Authentication Proxy Service" service and go to the Log on tab.
- Click on This Account
- Click Browse, and search for an AD service account username and select it.
- Enter the password.
- Click OK.
- Restart the service for the new rights to take effect.
-
The account you use typically does not require Domain Admin privileges, but it does need at least the "Log on as a service" right on the Authentication Proxy server and read access to Active Directory.
IMPORTANT: When you upgrade the Duo Security Authentication Proxy software to a newer version the service will revert to running as "Local System." Repeat the process above to change the service back to using a named domain service account.
- The domain service account running the Authentication Proxy service may not have the requisite permissions in Active Directory to find certain users or read their group membership. To resolve this, edit the Active Directory object permissions of the domain (or of the OU under which all synced users would be found), and grant "Read" rights to the domain service account on "This object and all descendant objects". Specifically, ensure that the domain service account has the "Effective Permissions" to read all properties of any user that needs to be synced.
Why are no OpenLDAP users imported when Directory Sync runs?
User import via OpenLDAP sync can fail for a few possible reasons, even when the directory status is "Connected":
-
The base DN used to configure OpenLDAP sync does not include any user accounts. The base DN specified should be at a level above all the organizational units or containers that hold users and groups you want to synchronize with Duo. You may find it easiest to set this to the top level of your domain.
-
The service_account_username specified for NTLMv2 or Plain authentication does not have sufficient privileges to bind to OpenLDAP and lookup user and group information.
How are synced users affected if I change the values of certain user attributes in Entra ID?
Changing synced attribute values in Entra ID has the following effects on imported users:
- If you change a user's e-mail address, display name, or telephone numbers, those new values are imported to the Duo user at the next sync.
- If the Entra ID UPN username value imported into Duo changes, the Duo username is updated accordingly (as determined by the "Normalize usernames" option).
- If you customized the username source attribute to specify something other than UPN, and the value for that imported into Duo changes, then a new Duo user is created with that username and the existing Duo user with the previous Entra ID username is marked for deletion. Devices do not automatically transfer from the old Duo username to the new one, so phones and tokens will need to be transferred or re-enrolled.
You may run into issues if you try to swap usernames between two Entra ID users at the same time, such as changing "joe@example.onmicrosoft.com" to "bob@example.microsoft.com" while also changing the original "bob" Entra ID account to "joe". We recommend changing the source Entra ID usernames to something new and unique to avoid a renaming conflict in Duo.
How are synced users affected if I change the values of certain user attributes in Active Directory?
Changing synced attribute values in Active Directory (AD) has the following effects on imported users:
- If you change a user's e-mail address, display name, telephone number, or notes, those new values are imported to the Duo user at the next sync.
- If the AD username value imported into Duo changes (default is sAMAccountName), the Duo username is updated accordingly.
How are synced users affected if I change the values of certain user attributes in OpenLDAP?
Changing synced attribute values in OpenLDAP has the following effects on imported users:
- If you change the value of the attributes you specified for a user's e-mail address, display name, telephone number, or notes, those new values are imported to the Duo user at the next sync.
- If the OpenLDAP username value imported into Duo changes, the Duo username is updated accordingly.
Can I edit attribute values for synced users from Duo?
User information synced from an external Entra ID directory, on-premises Active Directory, or OpenLDAP directory cannot be edited in Duo. This includes username, username aliases (if you imported aliases), full name, email address, phone numbers (if you imported phones), notes (if you imported notes), and group memberships. Changes to these user attributes should be made in the source directory and then synced over to Duo.
Directory sync permits editing values for optional custom attributes not configured in your sync (alias1 to alias4 and notes). If you do configure those attributes in your sync later, then imported values overwrite those you added manually. See Updating Synced User Information (Entra ID), Updating Synced User Information (AD), or Updating Synced User Information (OpenLDAP) for detailed examples.
You can attach hardware tokens and additional phones to synchronized users. These are retained after the next directory sync.
Can I change the name of a group synced into Duo?
To change the name of a group managed by directory sync you must rename the group in the source directory. The group's name will update in Duo when the next scheduled sync runs, or when a Duo admin visits that directory's page in the Duo Admin Panel (whichever happens first).
Can I change the username attribute synced from an external directory after the initial import?
No, the username attribute can only be modified before the first directory synchronization. After the directory has been synced, the username field will be disabled. The only way to change the Duo username source attribute is to create a new directory using the desired username attribute. This may affect your licensed user count and impact or prevent user authentications. Please contact Duo Support for more information and guidance.
Can I change the username alias attribute(s) synced from an external directory after the initial import?
Yes, you may change the source attribute for username aliases one through four at any time. New values imported at the next sync overwrite the previous alias values. Be sure to select source attributes for aliases that have unique values in your directory.
Can I change the format of the UPN username synced from Entra ID after the initial sync?
Yes, if you imported the userPrincipalName from Entra ID as the Duo username then you can enable or disable the "Normalize usernames" option after performing the initial sync. Duo usernames will be updated by adding or removing the domain suffix accordingly.
Can I edit attributes for synced phones?
Yes, you can change the device name, type, and platform, and activate a smartphone for Duo Mobile. However, you cannot change the phone number or extension while the phone is managed by Directory Sync.
If you disable the sync phones option in the directory sync's configuration, then Duo directory sync no longer adds or updates phones with information from the source directory. The previously synced phones become unmanaged by sync, and you may change the phone number or extension, or delete the phone from Duo.
Can I edit attributes for synced groups?
No, group attributes cannot be edited in Duo once the group is synced. Duo imports the group name as well as the members of each group from the external directory. Duo users cannot be removed from a synced group, and non-synced Duo users cannot be added to a synced group via any means but directory sync. When viewing group information, you'll see from AD Sync "name of sync" appended to the group's name or as the group's description.
To change the name of a synced group, change the name in the source directory. Duo will update the group's name to the new value the next time a sync is run, or when an admin views the directory's details page in the Duo Admin Panel (whichever happens first).
You can set the status of a synced group to Active, Bypass, or Disabled, which changes the status for all members of that group. You can also select which authentication methods are available to members of that group.
For more information on using groups to control status and authentication methods, see Group Settings.
What happens if a synced user is removed from synced groups?
If a synced directory user is removed from all external directory groups that sync to Duo (or if the user account is deleted in the source directory), the next full directory sync or individual sync of that user moves the user to the Trash and marks the account as "Pending Deletion". At this point, the user can no longer authenticate to Duo. The user's properties are read-only and you are no longer billed for that user.
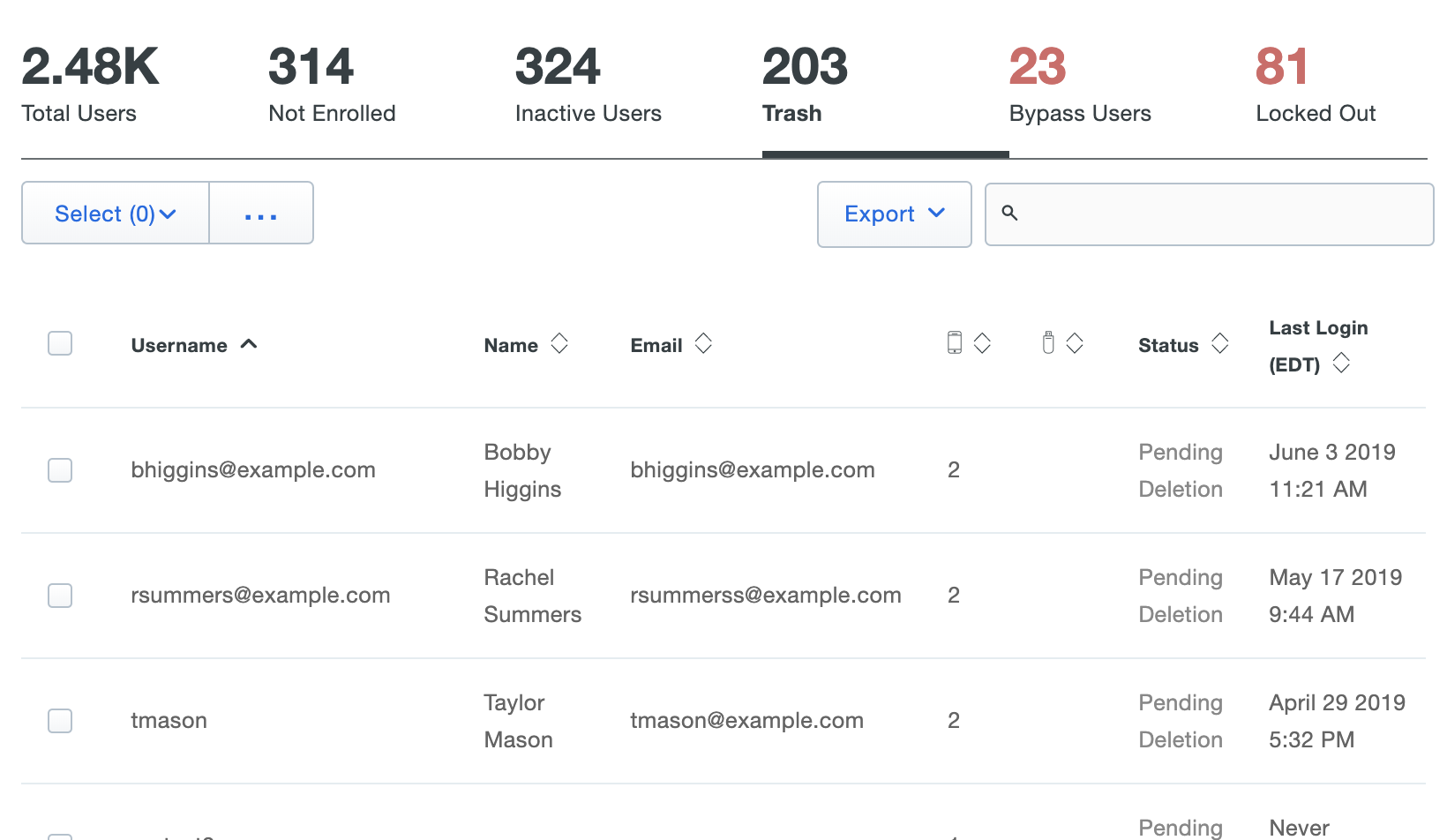
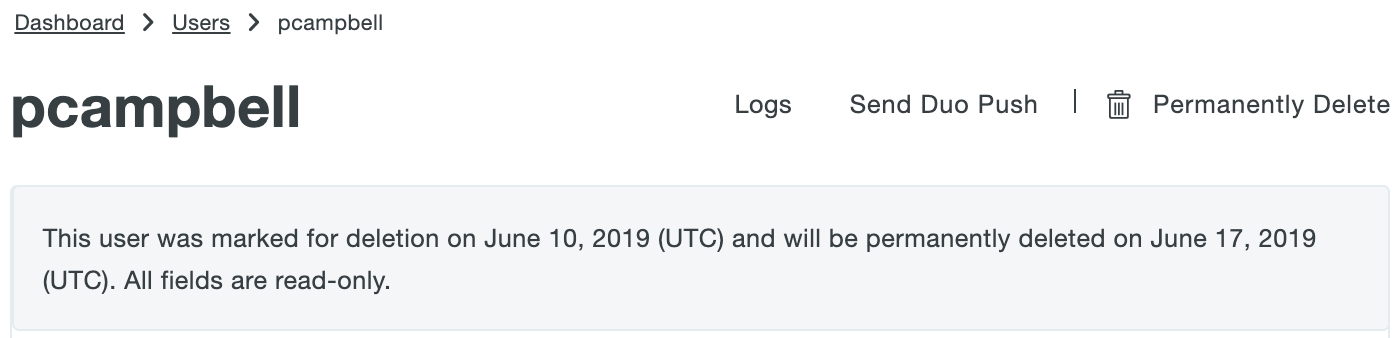
If the user marked for deletion is not reconnected to an external directory account via the sync within the configured Trash duration (default: seven days) the user is automatically deleted from Duo. The user's properties show the target date for deletion.
You can permanently delete a formerly synced user from the Trash at any time during the pending deletion period by clicking into the Trash view from the Users page in the Duo Admin Panel and using the Permanently Delete action. See Permanently Deleting Users for detailed instructions.
What happens if a synced user account is disabled in Active Directory or Entra ID, or suspended in Google?
If a synced directory user account is disabled in Active Directory or Entra ID, or suspended in Google, the user will be disabled in Duo automatically when the next directory sync occurs. The disabled Duo user is still tagged as a directory user, is read-only, and cannot be manually enabled. Disabling a user invalidates existing remembered device sessions.
On the Duo Authentication Proxy server, the authproxy.log file will show a useraccountcontrol value of 514 for a user if they are disabled in Active Directory. This information is only visible when debugging has already been enabled in the Authentication Proxy configuration file.
Please see the example below:
2018-12-07T15:39:26-0500 [ADClientProtocol,client] C<-S LDAPMessage(id=172L, value=LDAPSearchResultEntry(objectName='CN=Duo User,OU=Users,DC=domain,DC=com', attributes=[('objectClass', ['top', 'person', 'organizationalPerson', 'user']), ('cn', ['Duo User']), ('sn', ['User']), ('telephoneNumber', ['123-456-7890']), ('givenName', ['Duo']), ('distinguishedName', ['CN=Duo User,OU=Users,DC=domain,DC=com']), ('displayName', ['Duo User']), ('memberOf', ['CN=Duo_VPN,OU=VPN Users,DC=domain,DC=com',']), ('objectGUID', ['\xe6yW&\xb2\x0e\xf6K\x82?\xef2R\x06\f3']), ('userAccountControl', ['514']), ('sAMAccountName', ['duouser']), ('objectCategory', ['CN=Person,CN=Schema,CN=Configuration,DC=domain,DC=com']), ('mail', ['duo.user@example.com'])])Note that having a user in "disabled" status will not cause their account to be deleted.
How are new phone devices created by the Directory Sync?
When a user is synced from an external directory to Duo, new phones will be created using the mobile and telephone numbers present for each user if a phone with that number does not already exist in Duo. These devices cannot be deleted from the Duo interface and their phone numbers can't be changed, but the device name, type, and platform can be modified by Duo administrators.
A synced phone can be attached to another Duo user (thereby having the phone attached to multiple users simultaneously). You can also remove synced phones from AD synchronized users, but if the phone number is still present in the user's external directory properties the phone will be reattached after the next sync.
The Active Directory attribute telephoneNumber and the Entra ID attribute phone maps to Duo attribute phone1 and sets the Duo attributes type and platform to Unknown. The Active Directory attribute mobile maps to Duo attribute phone2, unless telephoneNumber is blank, in which case mobile maps to Duo attribute phone1. If a user already exists in Duo with an attached phone before the sync and that same phone does not exist in the source directory, that pre-existing phone will be phone1 in Duo and additional phones created by the sync will start at phone2.
New phone devices, whether the number is in the telephoneNumber or mobile source directory field, are created in Duo with type set to Mobile and platform set to Generic Smartphone.
Why might international phone numbers not get imported into Duo?
International phone numbers stored in the source directory must be prefixed with + and the country code, e.g. +4401617150105 for a UK number.
What happens when existing Duo phone numbers are synced with a directory?
If a phone number imported by the external directory synchronization already exists in Duo, the external directory information is merged in with the existing Duo phone number information. The Duo device name, type, and platform are retained, and the corresponding user is attached to the phone if that is not already the case. If the existing phone was attached to a different user before the directory sync, that attachment is retained after the sync as well.
What happens if a phone number is deleted from a directory?
If a phone number is deleted from a directory user and is not attached to any other Duo users when it is removed, the phone is deleted from Duo at the next sync. If the phone is attached to more than one user in Duo then the phone will still exist and remain attached to the users from whom the phone was not removed. You can manually delete that phone from the Admin Panel.
How does directory synchronization affect Duo users' hardware tokens?
Hardware tokens can be added to a synchronized Duo user, and the information for these tokens won't be overwritten by the sync process.
How are external directory user statuses related to Duo user statuses?
A Duo user has one of four possible statuses: Active, Bypass, Disabled, and Locked Out. A user's status can be changed in Duo interactively from the Admin Panel, programmatically via Admin API, or by CSV import if the corresponding external directory user is enabled in Active Directory or Entra ID with these additional considerations:
-
If a user is synced from an external AD or Entra ID directory then the user's status cannot be set to "Disabled" in Duo by any means other than the sync process.
-
If a Duo administrator changes an active, synced user's status to "Bypass", that status will not be overwritten by the sync regardless of any change to the user's enabled status in the external AD or Entra ID directory.
-
If an external directory user account is disabled in Entra ID or AD, or suspended in Google, but the user is still a member of a group synced to Duo, then the Duo user status is automatically set to "Disabled" and it cannot be changed in the Duo Admin Panel. The external directory's disabled status for an individual user also overrides any status assigned to a synced group in Duo.
- Note: Individual OpenLDAP-synced users and users imported from Okta or other external directories with SCIM cannot be disabled by sync. You can place users in a non-active status in Duo by removing the user from your synced group(s) and running a single-user or full Directory Sync. This disables users removed from the selected synced groups and puts those users in Pending Deletion status. You may disable a group of synced users by changing the status of that group to Disabled. This prevents any user who is a member of that group from logging in with Duo, regardless of that individual user's status. Learn more about Disabled status for OpenLDAP-synced users.
-
If a Duo user is in "Locked Out" status in Duo due to excessive failed login attempts, the Duo administrator can unlock the user. Account lockout in the external directory has no effect on Duo user status.
-
If an external directory user account is removed from all Duo-synchronized groups or is deleted from the directory, then the corresponding Duo user is moved to the "Trash" view and automatically marked as "Pending Deletion". This state can only be cleared by reconnecting the Duo user to a synced directory account (by adding the corresponding Entra ID, AD, or LDAP account to the group used for synchronization).
- Viewing the properties of that user while in the Trash shows the last effective status prior to being marked for deletion (e.g. Active, etc.). Refer to Duo KB article 3692 for more information on restoring users in Pending Deletion.
- Users in Pending Deletion do not consume user licenses and can not complete authentication with Duo regardless of the last effective status shown. You will need to manually adjust the user count in the Billing tab in order to reduce the number of licenses you are billed for.
Duo status settings are not imported or updated by a sync from an OpenLDAP directory, so "Active", "Bypass", or "Disabled" status may be set in Duo as needed.
How does deleting the synchronized group from Duo Directory Sync affect synchronized Duo users, groups, and devices?
If a directory group is deleted from the external directory or removed from the directory configuration in Duo, the Duo users from that group will be marked for deletion if they are not members of another synchronized group. Any phones imported for those users by the sync will also be removed unless they are attached to a remaining user.
Groups that were previously synced from the external directory will still exist in Duo. However, they will be changed to regular groups, whose attributes can all be modified and who can also be deleted from the Duo Admin Panel or Admin API. Duo updates the group's name to indicate it was once managed by directory sync, changing from Group name from type of sync "name of sync" to Group name (formerly from "name of sync"). You cannot delete groups formerly managed by the sync from Duo as long as a Duo Single Sign-On (SSO) routing rule condition uses them.
How does directory deletion affect synchronized Duo users?
If you delete the entire directory sync configuration from Duo, then the previously synced users, phones, and groups get converted to regular Duo objects and can be manually updated. Deleting the directory doesn't delete any of the previously imported objects.
Why am I receiving emails from Duo about my directory sync?
Duo emails admins with privileges to manage directory sync in the event of consecutive failures, pausing the sync, or other issues.
Some reasons an Active Directory and LDAP directory scheduled sync might fail and trigger a notification email include:
- An Authentication Proxy disconnected from Duo's service.
- The Authentication Proxy can't contact the specified directory servers.
- An invalid base DN specified for the directory.
An Entra ID or Google sync might fail and trigger a notification email when the Duo Sync application needs reauthorization.
Okta and generic inbound SCIM integrations will fail and send a notification email when the bearer token expires and needs to be regenerated and updated in Okta or in your external SCIM directory.
Note that a failure to run the scheduled synchronization process is not the same as if the sync completes with success indicators but does not sync your expected users, groups, or attributes. In these situations, double-check your group and synced attribute selections, and the rest of your directory sync configuration to ensure your settings match your expected results.
Additional Troubleshooting
Need more help? Try searching our directory sync Knowledge Base articles or Community discussions. For further assistance, contact Support.
