Duo Trusted Endpoints - Duo Mobile Verification
Last updated:
Overview
Duo's Trusted Endpoints feature secures your sensitive applications by ensuring that only known devices can access Duo protected services. When a user authenticates via the Duo Prompt, we'll check for the access device's management status. You can monitor access to your applications from trusted and untrusted devices, and optionally block access from devices not trusted by your organization.
Trusted Endpoints is part of the Duo Essentials, Duo Advantage, and Duo Premier plans.
There's no need to deploy a separate mobile device management (MDM) solution before you can create access policies for mobile device endpoints. The Duo Mobile app already installed and activated for Duo Push on your users' phones can also serve as your Android and iOS managed device verification tool.
Whether the access request from the mobile device browser was approved with Duo Push or with a different authentication factor (like an SMS passcode), Duo prompts the user to open Duo Mobile to perform a device health check during authentication.
If the Duo Mobile check determines that the device satisfies your organization's access policies, such as screen lock enabled, updated OS version, or other configured policy requirements, then that mobile device used to access your Duo-protected application is "trusted".
Mobile Trusted Endpoints and Verified Duo Push: Trusted endpoint verification of iOS and Android devices with Duo Mobile uses the standard Duo Push approval process and will not prompt for a Duo Push verification code, even if the effective authentication methods policy for the user and application has "Verified Duo Push" enabled.
Prerequisites
- Access to the Duo Admin Panel as an administrator with the Owner, Administrator, or Application Manager administrative roles.
- End users must have Duo Mobile installed on their mobile access devices, activated for Duo Push authentication.
- End users of the Trusted Endpoints integration must exist in Duo as users.
- Note that Duo user accounts and administrator accounts are distinct. Be sure to also enroll your Duo administrators as users if they need to log on to Duo protected services.
Android
Create the Duo Mobile Integration
- Log in to the Duo Admin Panel and navigate to Devices → Trusted Endpoints.
- If this is your first management integration, click the Get started button at the bottom of the Trusted Endpoints introduction page. If you're adding another management integration, click the Add Integration button you see at the top of the page instead.
- On the "Add Trusted Endpoint Integrations" page, locate Duo Mobile in the list of integrations.
- Choose Android from the "Select operating system" drop-down, and then click the Add button.
The new Duo Mobile integration is created in the "Disabled" state. You'll turn it on when you're ready to apply your Duo trusted endpoints policy.
On creation the integration is disabled and applies to no users until you finish your deployment.
iOS
Create the Duo Mobile Integration
- Log in to the Duo Admin Panel and navigate to Devices → Trusted Endpoints.
- If this is your first management integration, click the Get started button at the bottom of the Trusted Endpoints introduction page. If you're adding another management integration, click the Add Integration button you see at the top of the page instead.
- On the "Add Trusted Endpoint Integrations" page, locate Duo Mobile in the list of integrations.
- Choose iOS from the "Select operating system" drop-down, and then click the Add button.
The new Duo Mobile integration is created in the "Disabled" state. You'll turn it on when you're ready to apply your Duo trusted endpoints policy.
On creation the integration is disabled and applies to no users until you finish your deployment.
Finish Trusted Endpoints Deployment
After creating the Duo Mobile management integration, set the Trusted Endpoints policy to start checking for managed device status as users authenticate to Duo-protected services and applications.
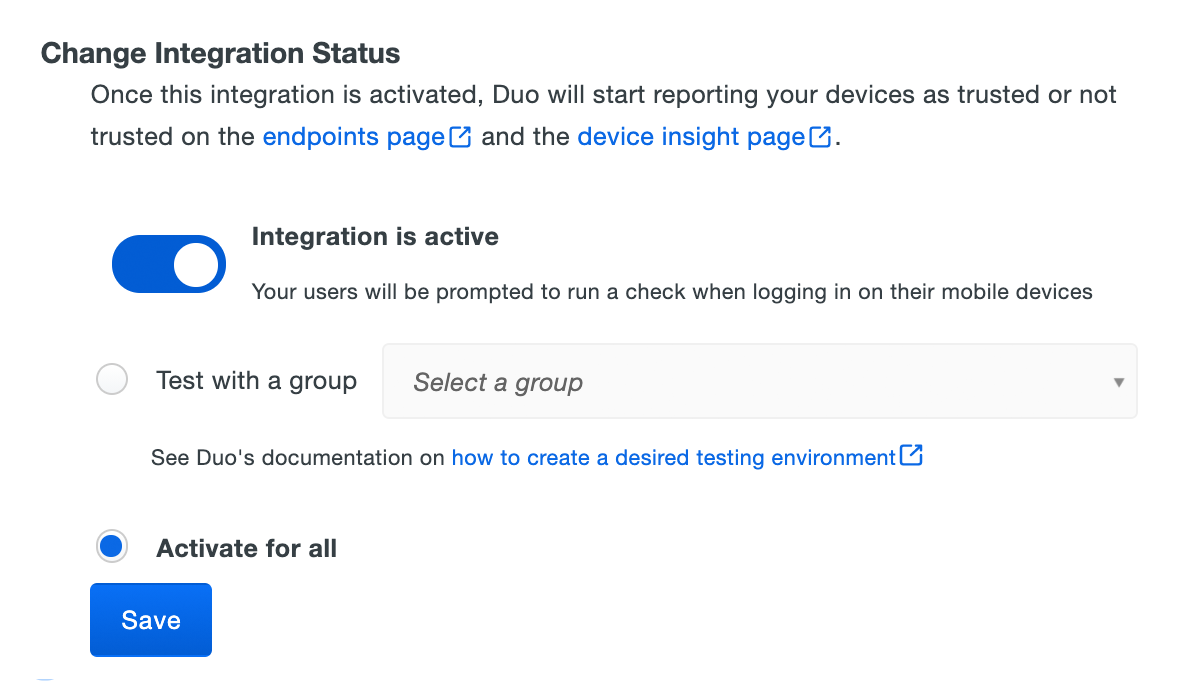
When your trusted endpoints policy is applied to your Duo applications, return to the Duo Mobile trusted endpoint management integration in the Admin Panel. The "Change Integration Status" section of the page shows the current integration status (disabled by default after creation). You can choose to either activate this management integration only for members of a specified test group, or activate for all users. If you created more than one Duo Mobile integration, you must activate each one individually.
If you create the Duo Mobile trusted endpoints management integration alongside another mobile management integration (like Workspace ONE or Ivanti Neurons for MDM) then Duo Mobile acts as the default management integration and Duo no longer uses your other MDM management integrations for device verification.
The Device Insight and Endpoints pages in the Duo Admin Panel show which access devices are trusted/managed and enrolled in Duo Mobile.
Verify Your Setup
Users with Duo Mobile installed and activated for Duo Push on Android and iOS devices see a device trust dialog when authenticating to a protected resource via the Duo Prompt.
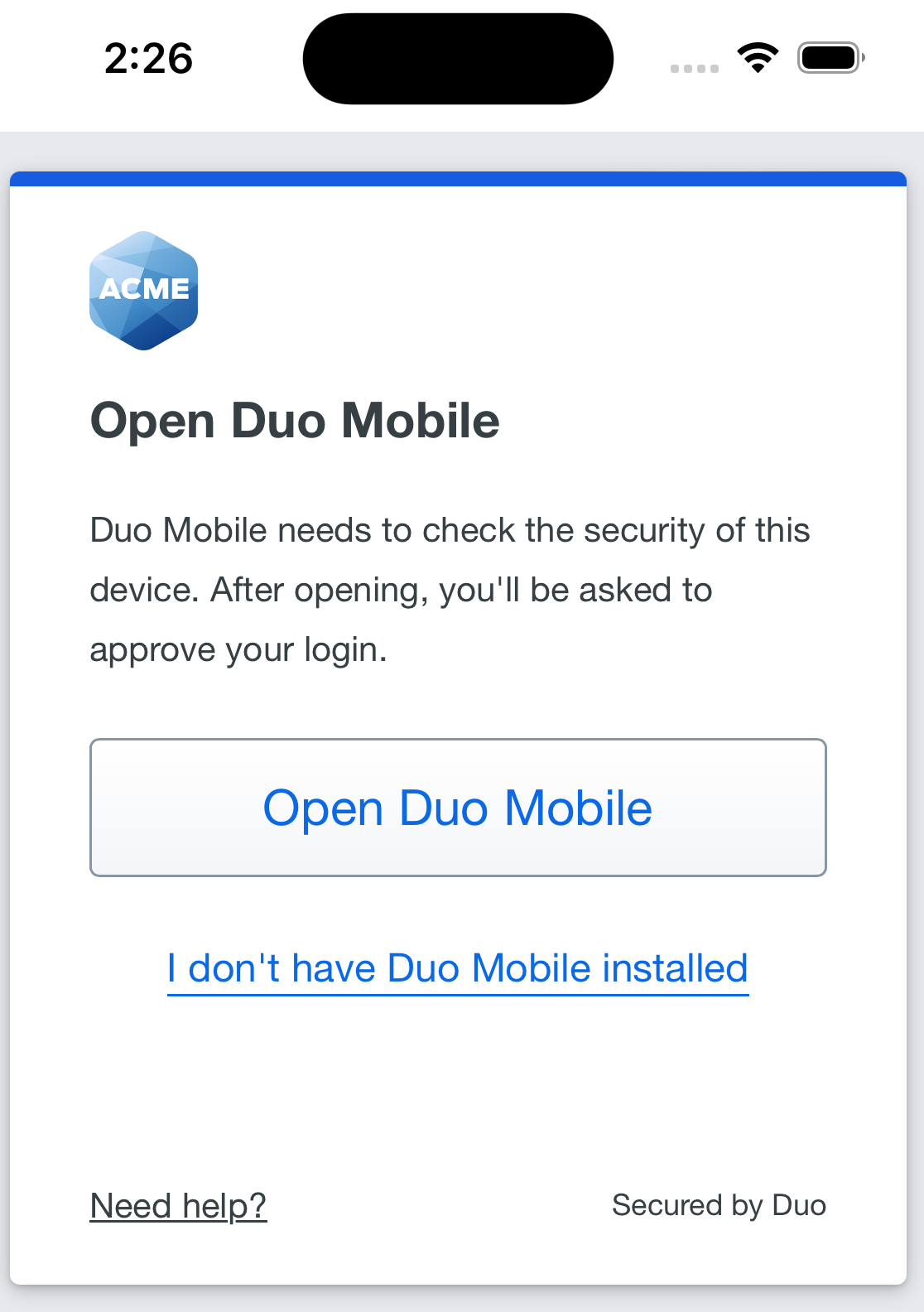
The prompt opens Duo Mobile on the device for verification.
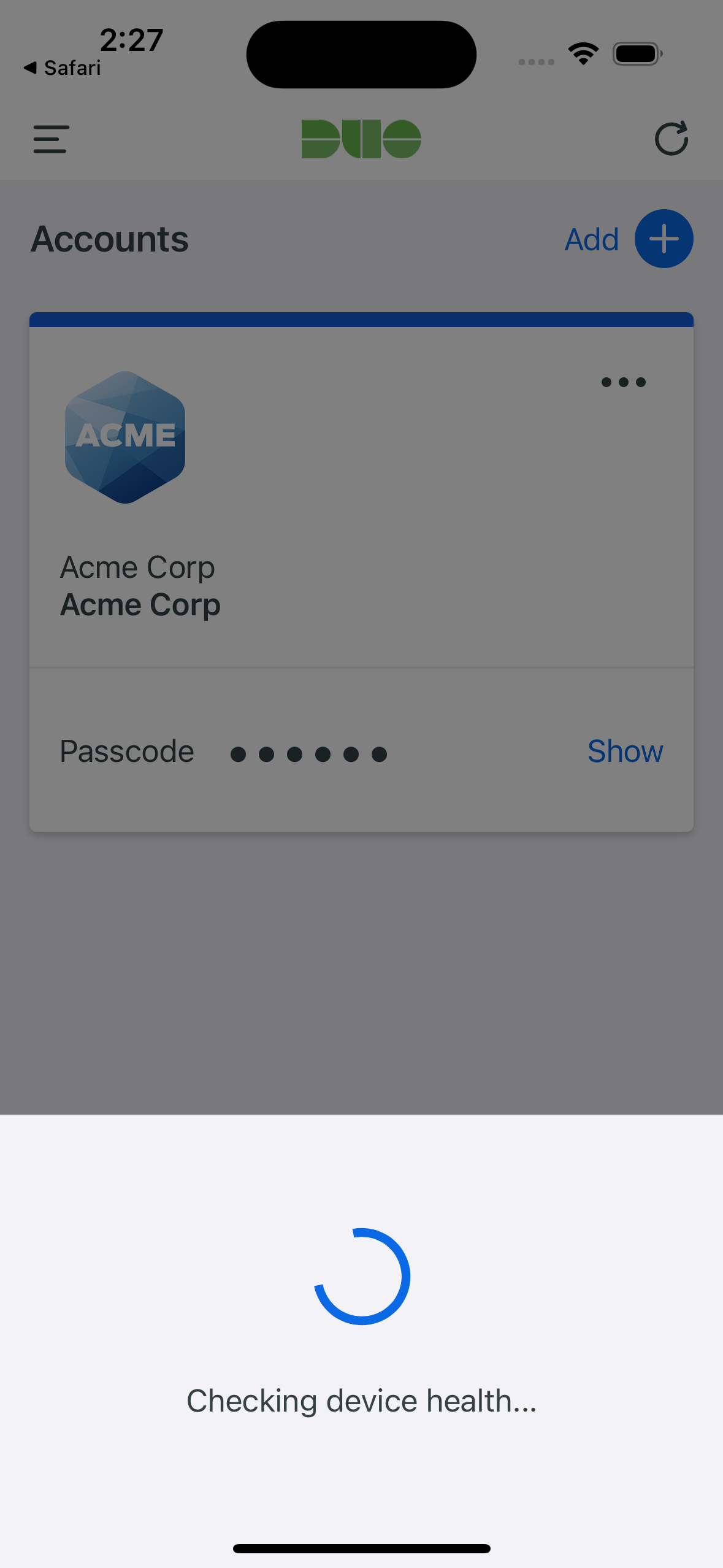
If Duo successfully verifies the device information with Duo Mobile, and the user has Duo Mobile activated for Duo Push, then the user receives a login request on their phone.
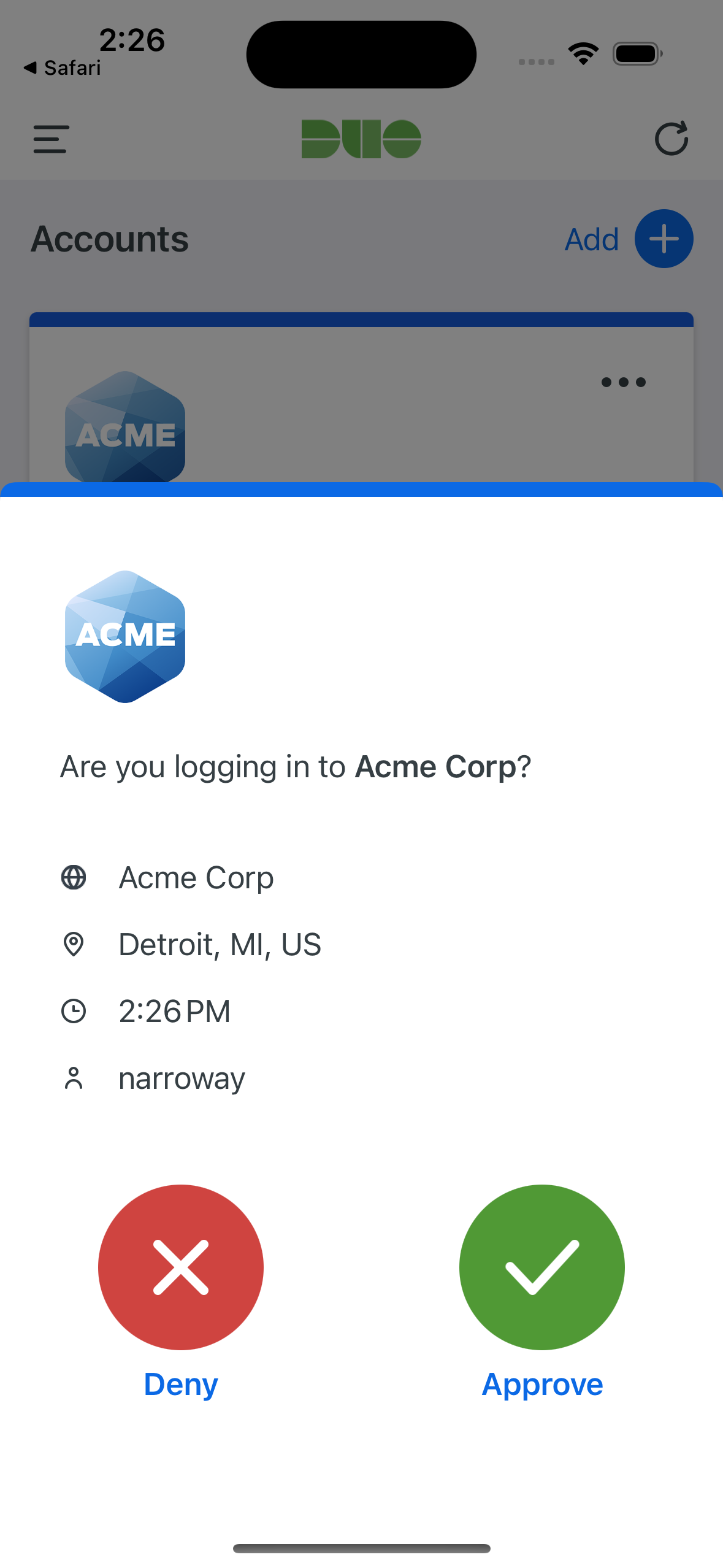
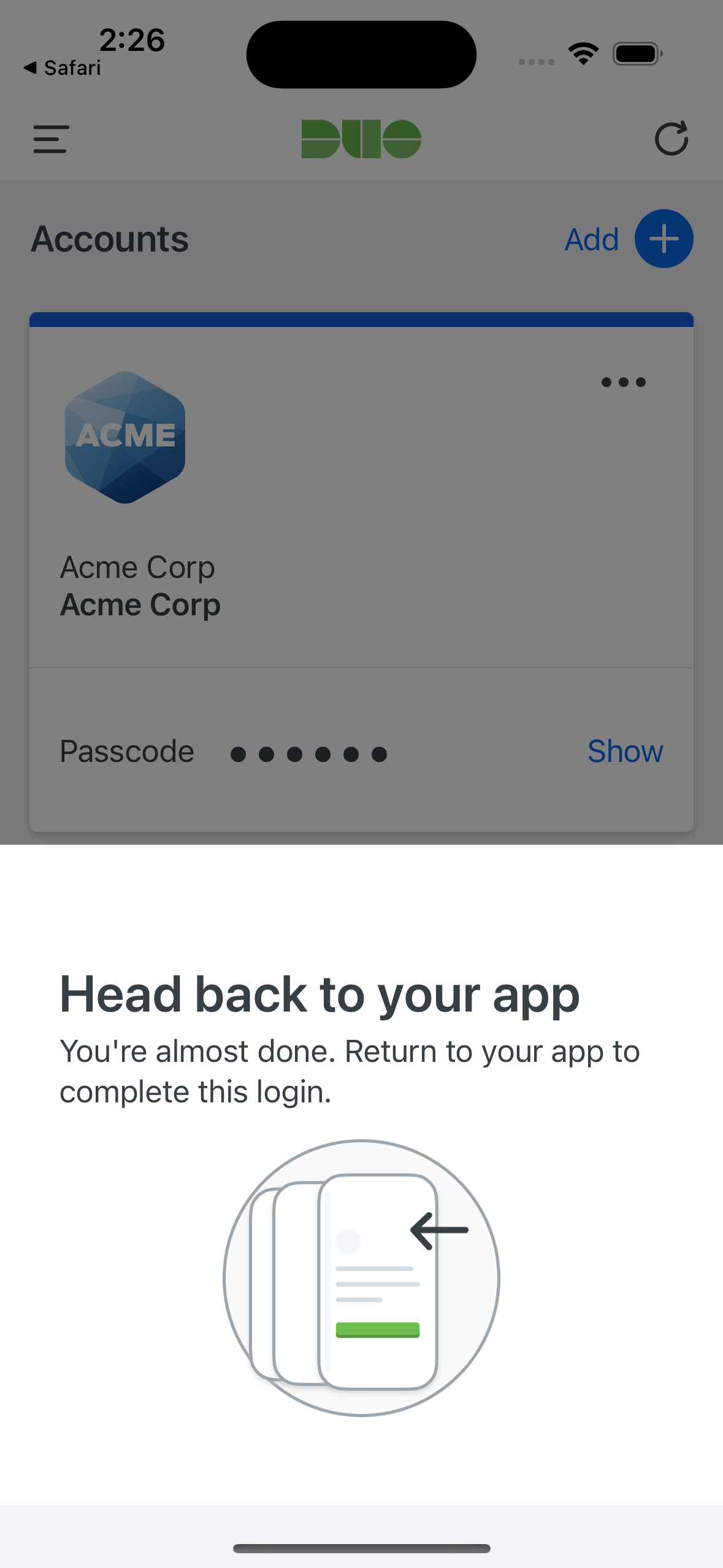
On Android devices, approving the request grants access and returns the user to the protected application. On iOS devices, after approving the Duo authentication request users tap the top-left of the Duo Mobile app to return to the application and complete login.
If the user does not have Duo Mobile activated for push, or does not approve the Duo request before it times out, the user returns to the Duo Prompt, where they may select from the available factors to complete 2FA. The "Second Factor" logged for these approvals is shown as "Duo Mobile Inline Auth" in the Duo authentication log.
When the trusted endpoints policy is set to just check access devices, users receive access to the application (assuming the device passes all other policy verification), and Duo records the trusted or untrusted status of that device.
If the trusted endpoints policy blocks access from unmanaged devices and Duo successfully verifies the device information against the required policy settings then the user receives access to the protected application.
If the mobile device fails the configuration and policy checks then Duo denies application access.
Troubleshooting
Need some help? Take a look at our Trusted Endpoints Knowledge Base articles or Community discussions. For further assistance, contact Support.
