Duo Administration - Admin Panel Overview
Last updated:
Action Required: April 15, 2026 Duo CA Bundle Expiration
Duo products that use certificate pinning require a software update for uninterrupted use. Legacy clients could stop working at any time after April 15, 2026.
Please visit Duo Knowledge Base article 9451 for more information and guidance.
Overview
Manage your Duo deployment from the Duo Admin Panel. This includes configuring Duo Single Sign-On, creating and managing applications, enrolling and activating users, issuing and managing SMS passcodes and bypass codes, managing mobile devices, fine-tuning the user experience of your Duo installation, and more.
Accessing the Duo Admin Panel
The browser used to access the Admin Panel must support TLS 1.2, which most modern browsers do by default. If you have issues accessing the site, please update your browser to a recent version of Chrome, Firefox, Edge, Safari, etc. or check your browser’s SSL implementation here: https://www.ssllabs.com.
Duo no longer supports use of Internet Explorer to access the Admin Panel. Microsoft ended Internet Explorer desktop application support on June 15, 2022. Please use one of Duo's supported browsers.
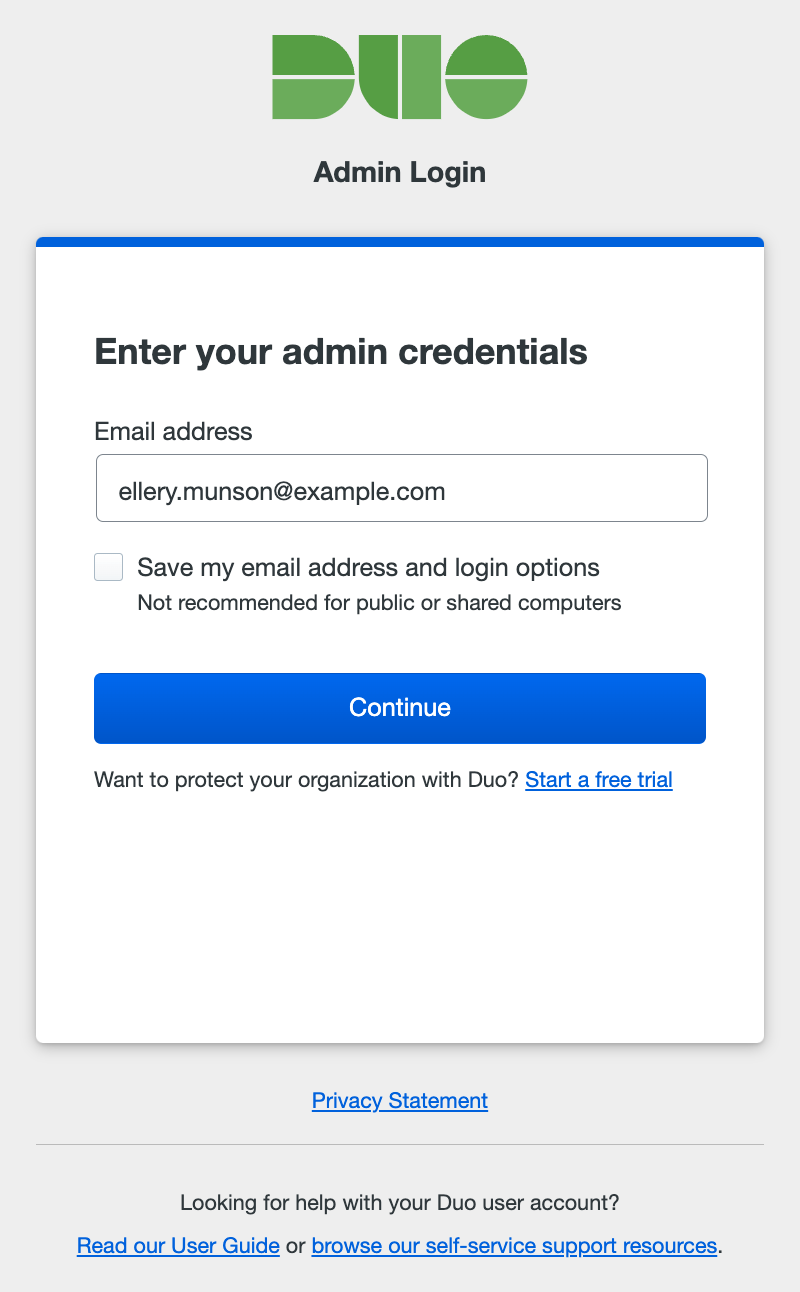
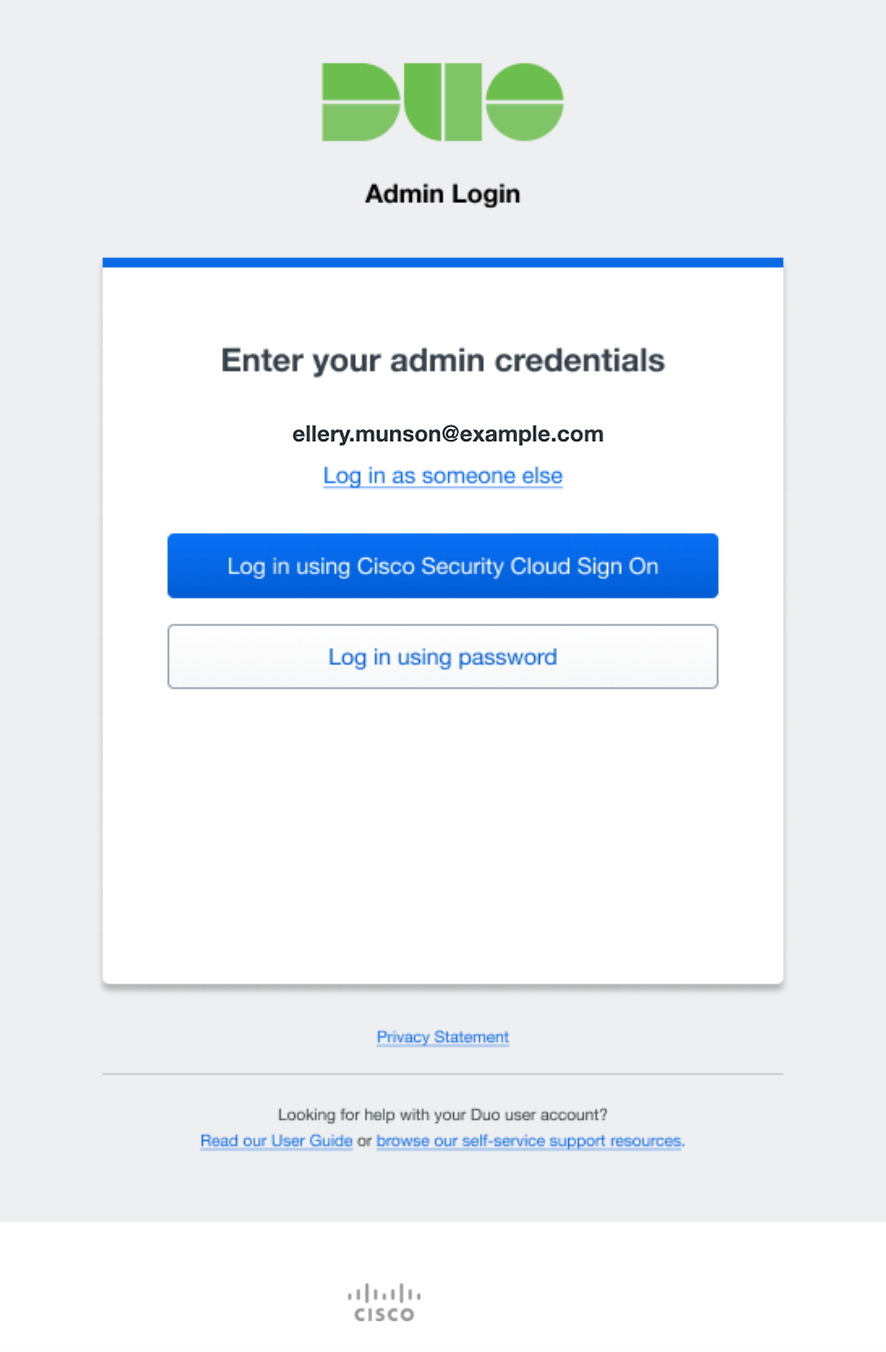
To access the Duo Admin Panel:
-
Navigate to the Duo Admin Panel at https://admin.duosecurity.com.
-
Enter your administrator account email address. If you're logging in from a private computer or device, you can check the Save my email address and login options box. Don't do this if you are on a shared kiosk or public computer.
-
The next step depends on whether your organization uses Cisco Security Provisioning and Administration (formerly Security Cloud Control) or has federated Duo administrator logins with an external single sign-on identity provider (IdP), and whether using SSO login is required or optional.
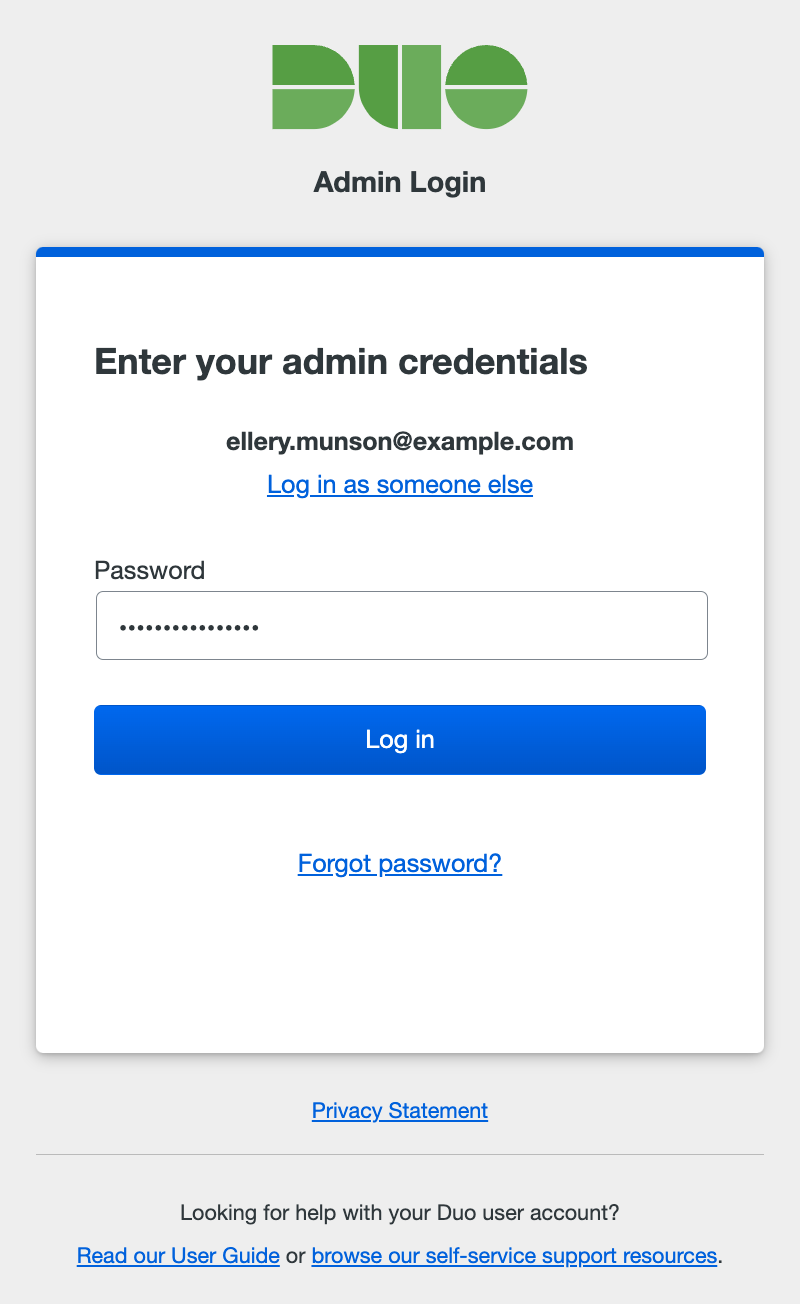
Password Login Only
Your organization has not configured SAML login for admins, so no SSO options are presented. Enter your administrator password, and click Log in.
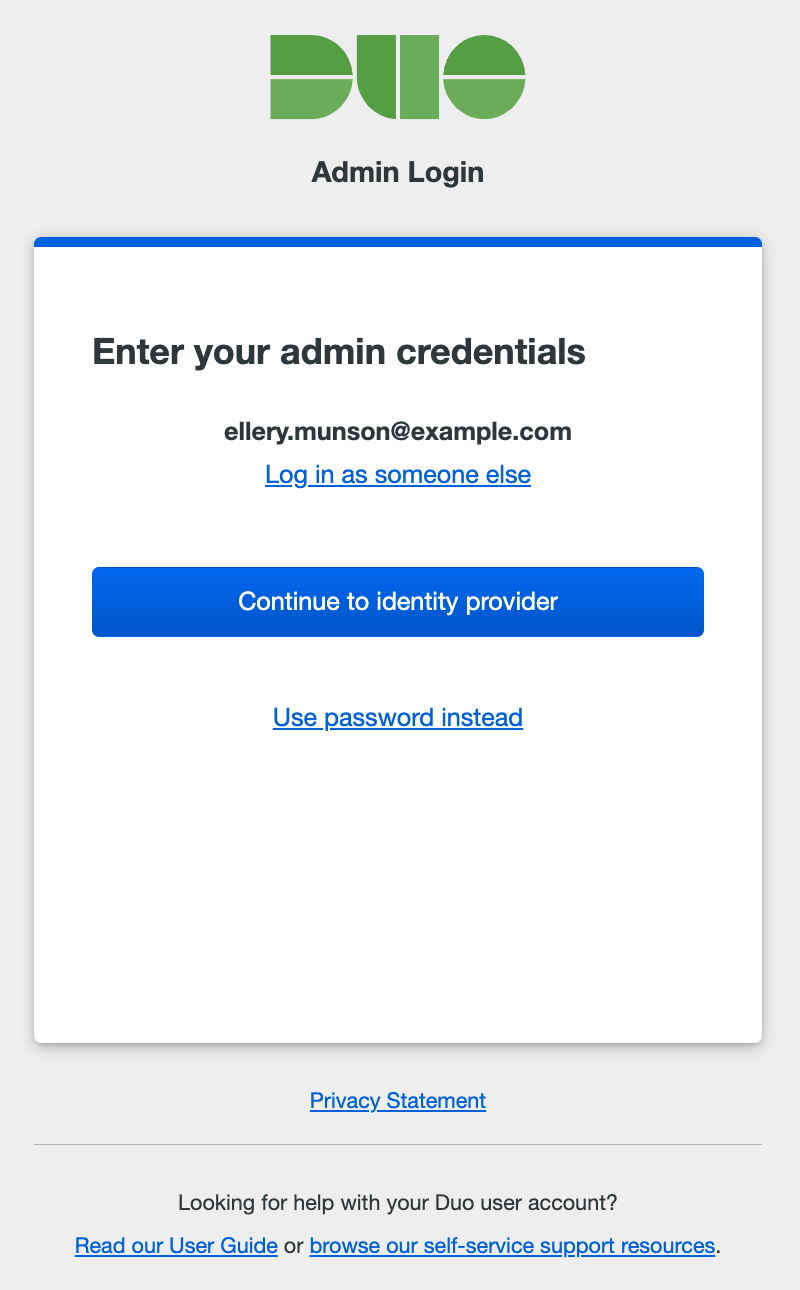
SSO Login Required
Your organization prefers that administrators sign in using SSO. Click the Continue to identity provider button to be taken to your organization's identity provider (IdP) where you'll sign in with your primary user credentials.
SSO Login Optional
You can choose how to sign-in. Clicking the Log in using Single Sign On button takes you to your organization's IdP to complete primary authentication.
If you created a password for the Duo Admin Panel you may use that instead of SSO. Click Log in using password to show the password entry form. Enter your administrator password, and click Log in.
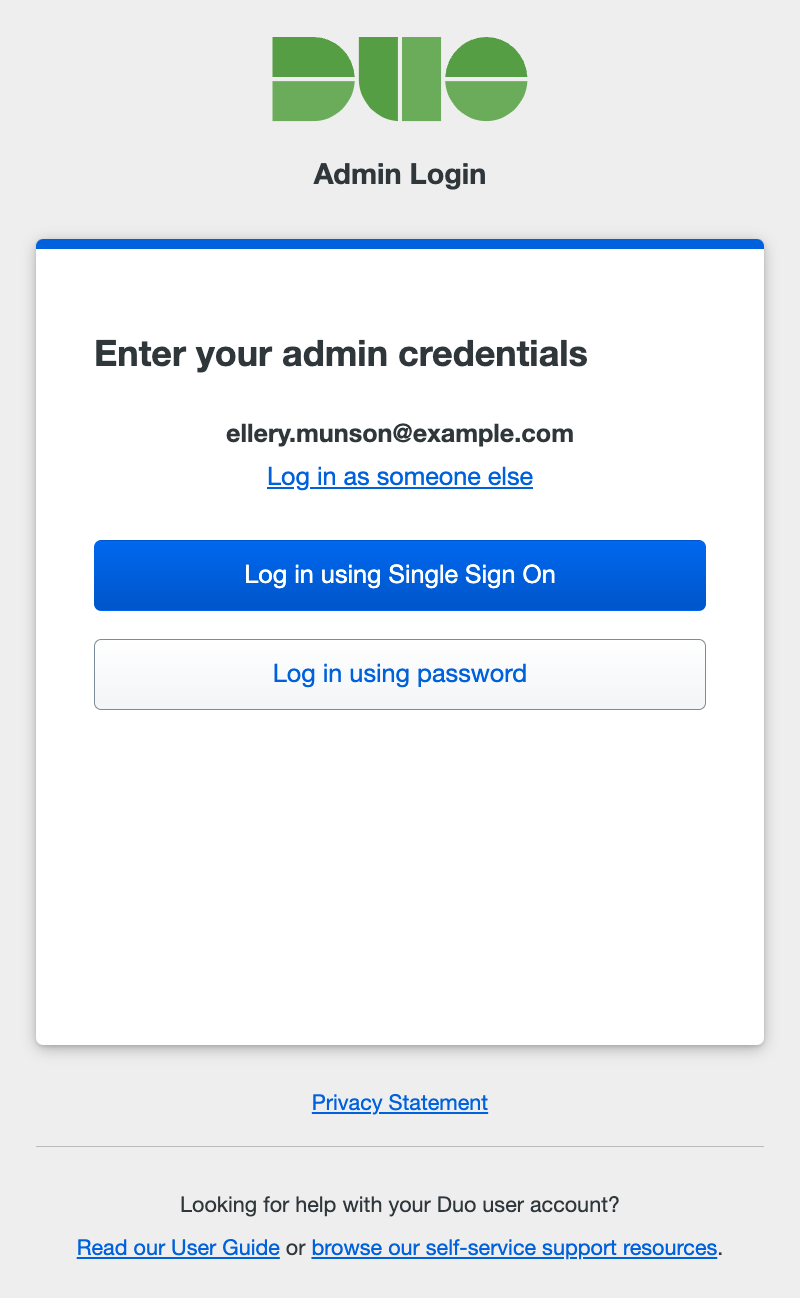
If you checked the Save my email address and login options box when you entered your Duo administrator username, then we'll also save your SSO login preference and won't ask you to choose between single sign-on or password authentication again.
Cisco Security Cloud Sign On
If your organization is provisioned through Cisco Security Provisioning and Administration (formerly Security Cloud Control), you will see an option to Log in using Security Cloud Sign On (SCSO). This will take you to SCSO or your organization's IdP for primary and secondary authentication depending on how your enterprise admin has configured your setup.
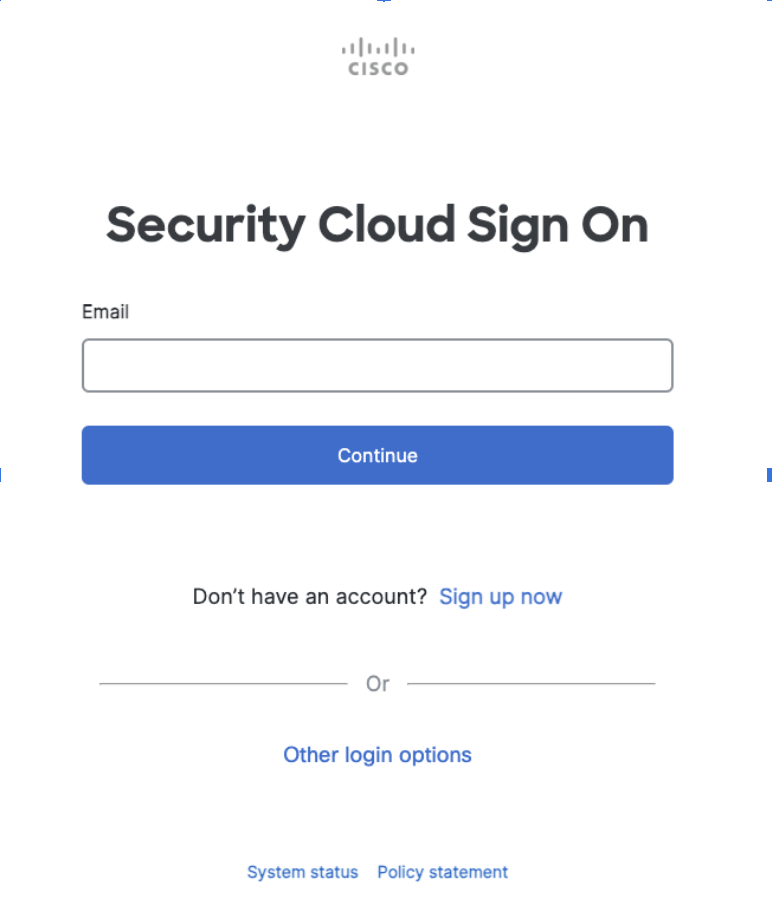
New administrators whose accounts were created through Cisco Security Cloud Control (SCC) after May 11, 2026 should sign on to Cisco’s Security Cloud Control (SCC) to log in to Duo.
-
After successful authentication via SSO or by entering the correct Duo admin password, you then must authenticate using a second factor. Complete login verification by selecting one of the available methods.
-
Duo Push: Approve a login verification request sent to your smartphone with the Duo Mobile app. You must activate your administrator account for Duo Mobile separately from your user account to use Duo's push authentication at the Admin Panel. See Use Duo Push for Administrator Authentication for instructions.
If Verified Duo Push is enabled in Admin Authentication Methods, you must enter a verification code in the Duo Mobile app to approve a login request. See Use Verified Duo Push for Administrator Authentication for instructions.
-
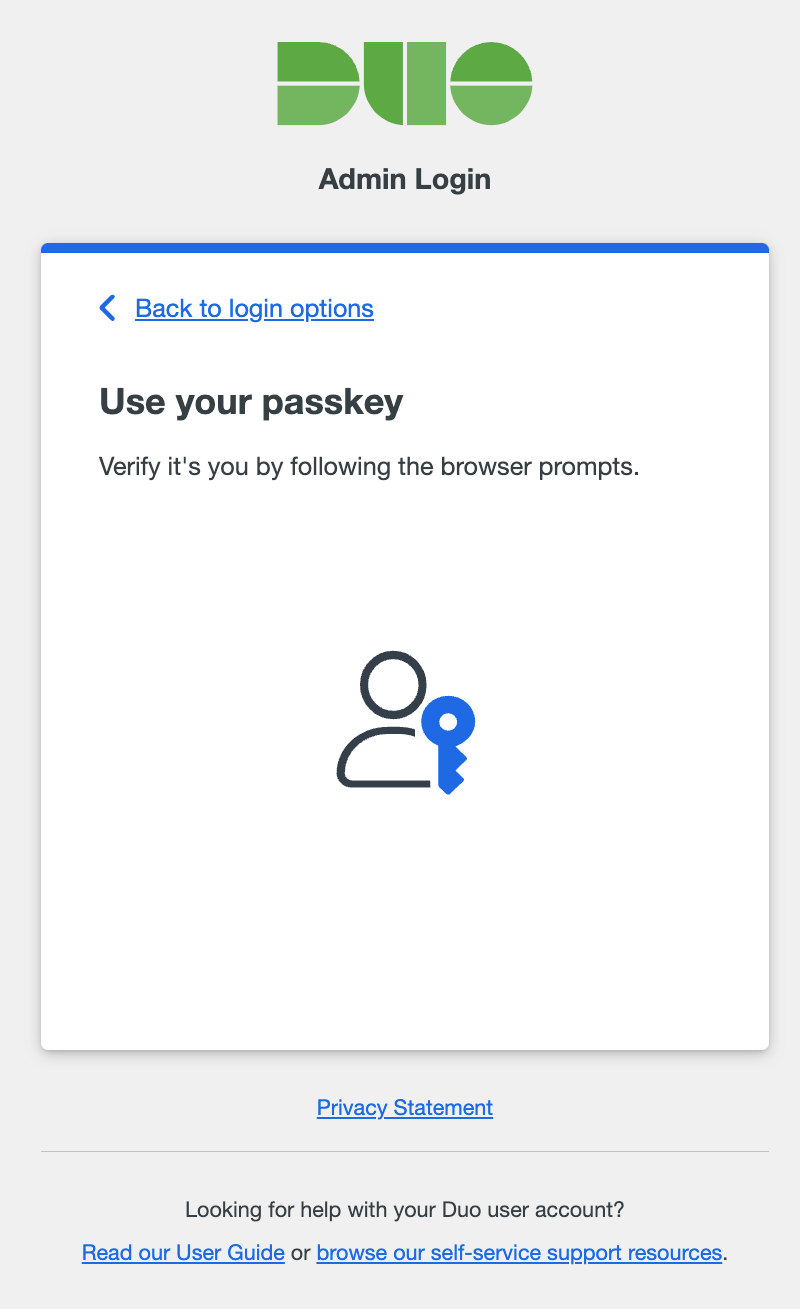
Passkey: Use a passkey including security keys and biometrics. For supported external security key devices, insert it and then touch it. For integrated devices like Touch ID, follow the prompts from your browser that appear to confirm your identity. This method only appears if you have added a passkey to your admin profile.
-
Text Message: Receive an SMS message containing a one-time passcode and enter the passcode in the space provided. This passcode is valid for five minutes.
-
Phone Call: Receive a phone call communicating a one-time passcode and enter the passcode in the space provided. This passcode is valid for five minutes.
-
Duo Mobile passcode: Authenticate with a passcode generated in the Duo Mobile app.
-
Hardware Token: Enter a passcode generated by a physical device issued by your organization.
-
Yubikey passcode: Authenticate with a passcode generated by a Yubikey.
The two-factor authentication methods available may differ depending on your organization's Admin Authentication Methods settings. If, for example, your organization disabled the "Phone Callback" method, you won't see the "Phone call" 2FA option when you log in.
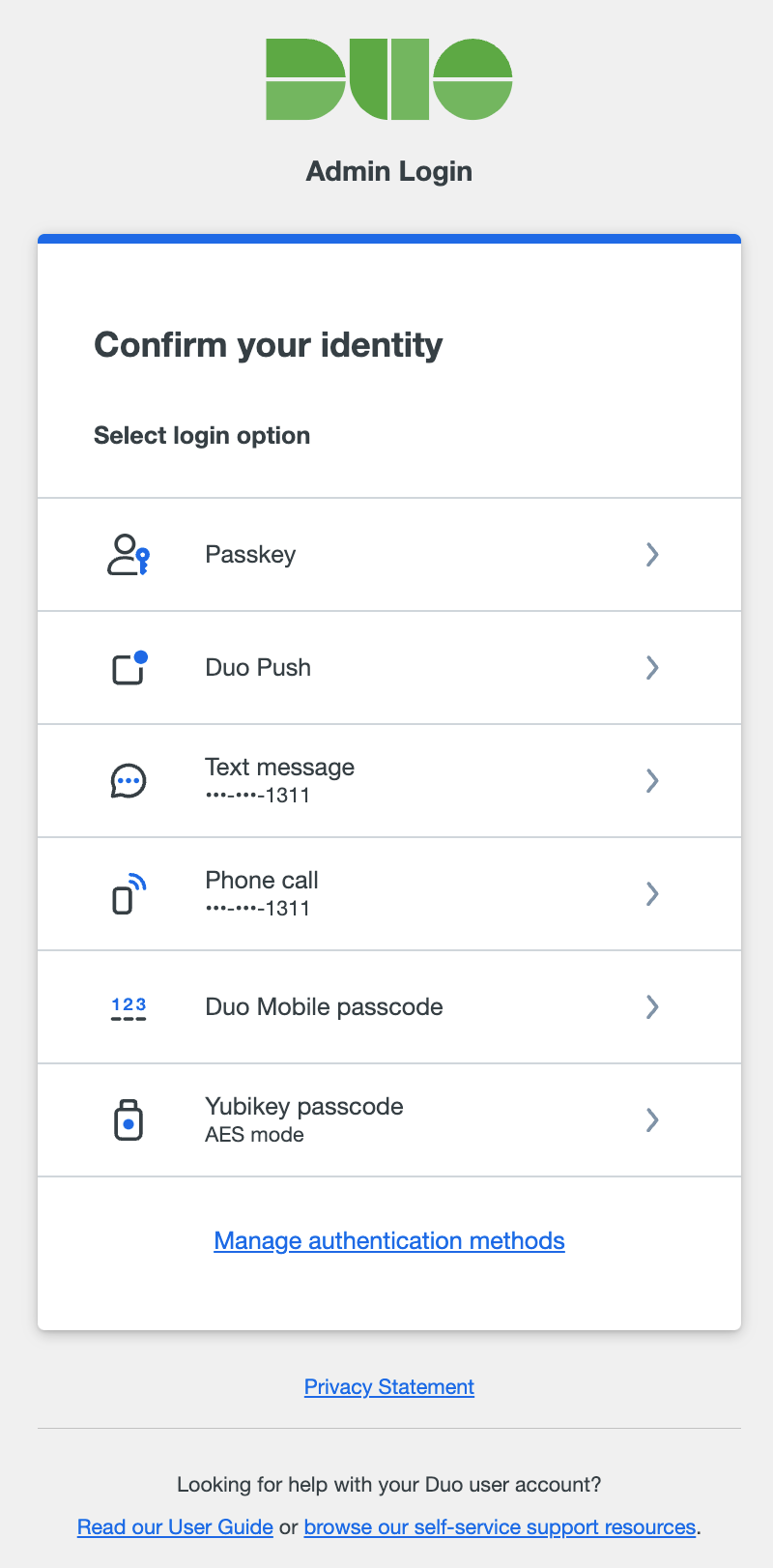
If you want to choose a different way to confirm your identity after your initial choice, click Back to login options to return to the list of all second-factor options and choose again.
If you checked the Save my email address and login options box earlier and also use a passkey or Duo Push as your authentication method, we will save that method as a preference as well and prompt you automatically to use the same verification method the next time you log in. You can always cancel the automatic verification in progress by returning to the list of login options to choose a different method.
-
Forgotten Password
If you've forgotten your password, click the Forgot Password link shown after you enter your email address. Enter the email address that you use to log in to your Duo administrator account and click Submit. Check your email for your password reset link.
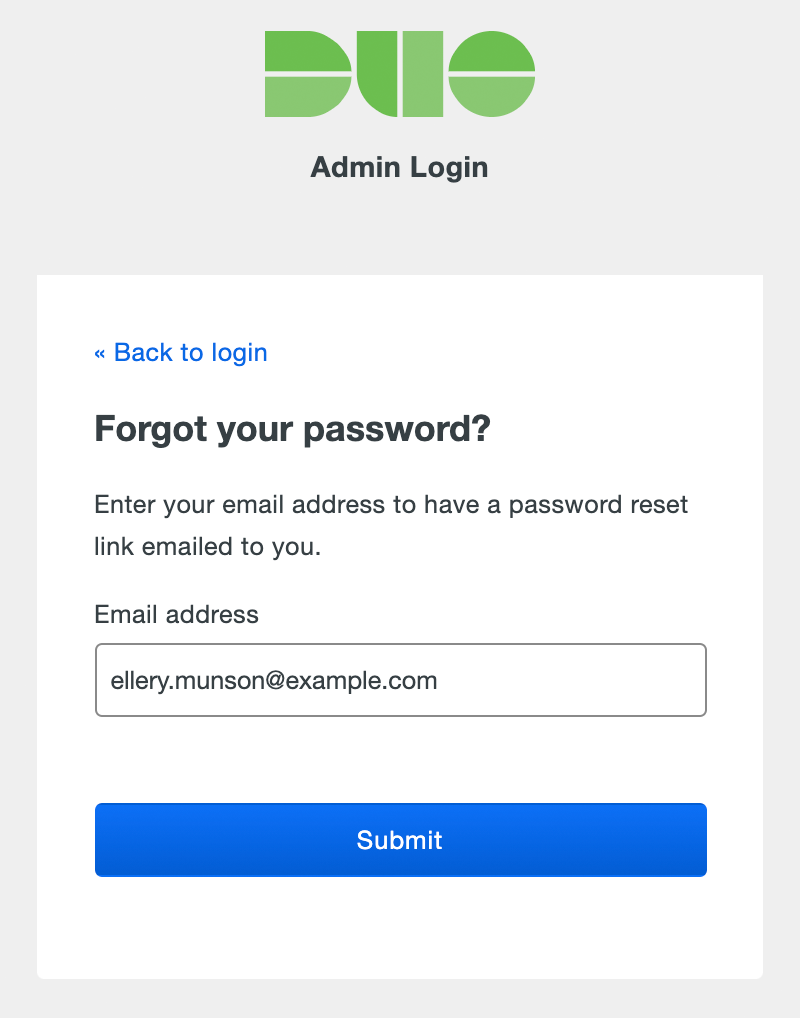
We'll also send you a notification email once you've changed your password. If you receive a password change notification and you didn't initiate this change, contact your organization's Duo owner or Duo Support.
If a Duo Admin forgets their password and doesn't have access to the email address entered, Duo Owner administrators can copy the password reset URL from the Duo Admin Panel. See Reset an Administrator's Forgotten Password for more information.
First-Time Administrator Account Setup
If you're a new Duo administrator for your organization, you likely received an account setup link from your org's Duo owners via email, text message, or another method of communication. Click that link to begin the setup process.
-
If your admin password will be stored in Duo, click Create Password to set your password. Passwords must have at least twelve characters, and may also require a mix of character types depending on your Admin Password Policy settings. New passwords will be checked against common passwords, usernames, and other account information to ensure uniqueness.
If your organization uses single sign-on with its own identity provider (IdP) for Duo Admin Panel logons, then click Create account using Single Sign On and sign in at your IdP with primary username and password.
-
After either setting a password or signing in at an external IdP, you can add a passkey, such as Touch ID or an external security key. Click Add Passkey and follow the prompts from your browser.
If you don't have a passkey device available, click Skip for now. You must add at least one second factor for login verification.
-
Install Duo Mobile on your Android or Apple smartphone and scan the QR code shown on-screen to activate Duo Push two-factor authentication for your Duo administrator account.
If you don't have a smartphone, click Don't have a smartphone? Skip for now.
-
If a phone number was entered for you when your account was created, you can confirm that's the right backup phone number for Duo Admin Panel logins, or enter the correct backup phone number if it is not. You can skip this if you never plan to use phone call or SMS text messages to log into your Duo administrator account (if, for example, you received a hardware token from your organization to use as a backup login verification method).
If no phone number was entered when your account was created, and phone call or SMS text messages are enabled in Admin Authentication Method, then you can enter your phone number.
-
When you've finished with setup, click the Continue to Duo Admin Panel Login button to log into the Duo Admin Panel with the password you just set (or after SSO login), using a passkey, Duo Push, or phone call/SMS, depending on what authentication methods you set up.
Account Lockout
Entering the wrong password or passcode for your admin account or letting the push or phone call 2FA approval request time out increments the failed login count. After ten failed login attempts, your admin account will be locked out. Duo will send you an email containing a link you can click to immediately unlock your account. Otherwise, your admin account will automatically unlock after 24 hours.
If you don't have access to email and you can't wait 24 hours for your account to unlock itself, then you can ask another Duo admin at your organization for help. See Unlocking an Administrator for more info about manually unlocking an admin account.
Admin Panel Overview
Home
The Admin Panel "Home" page is a dashboard that gives you a snapshot of your organization's activity.
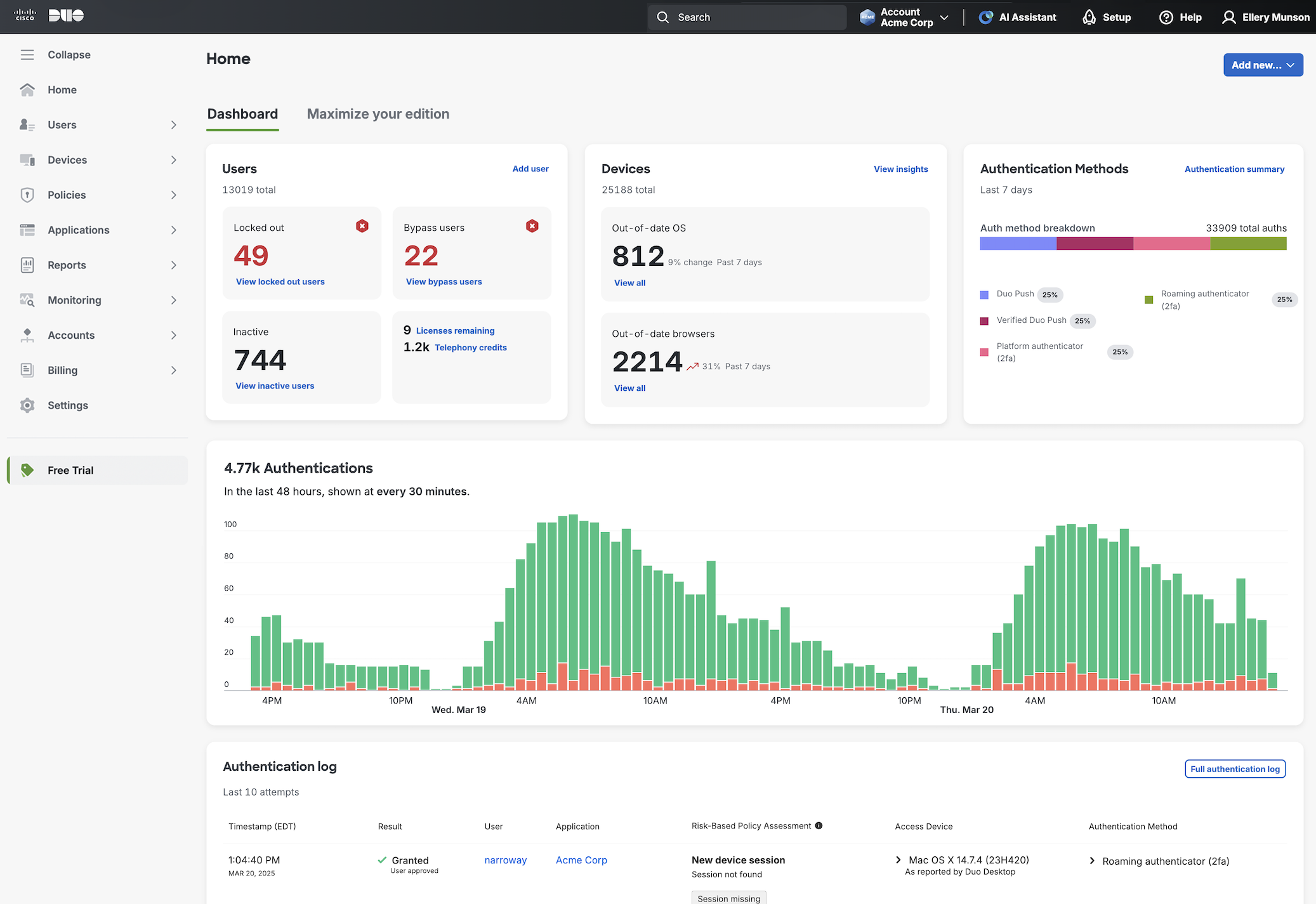
When viewing the dashboard keep in mind that we round very large quantities for the dashboard display, but you can click any of the numbers to see an exact count.
The information shown first on the dashboard provides counts of your total end users, users with bypass or locked out status, and inactive users who haven't logged in using Duo for the last 30 days. Click on the links below this information to view a filtered list of users in those states.
Click the "Licenses Remaining" link to view the Deployment Progress report, which tracks how many end users there are in your Duo deployment, how many applications you've protected with Duo, the average number of 2FA devices per user, and the top authentication method used over the last seven days.
The Telephony Credits information shows you your available credits, and takes you to the page where you can manage your telephony credits balance.
The Devices summary information on the dashboard indicates how many of your user devices have outdated operating systems or browsers and shows how that number has changed over the last week. Click the View all links to view more detailed information on the Device Insight page.
A bar chart on the right shows the your top-five most used authentication methods, and links to the Authentication Summary report. Any authentication methods beyond the top five will be grouped into an "Other" category.
Click anywhere on the interactive graph of your most recent authentication successes and failures to view the Authentication Log, filtered to display the related events.
The Authentication Log lists information about the last ten Duo login attempts, including the following:
- Date and time of the access attempt
- Whether the authentication was successful or not and why
- The Duo username
- Which application was accessed
- Access device information, such as the source IP address and location (if the login originated from a public IP address), the client OS, browser, and plugin information, and trusted status
- Second factor device information, such as the type of Duo factor used, the device's phone number, and source IP address and location (if the Duo Push response originated from a public IP address)
You can click the "Full authentication log" link to view all login events.
Click Maximize your edition on the Admin Panel "Home" page to review suggestions for getting the most out of your Duo subscription. We'll be rolling this feature out gradually to all paid editions.
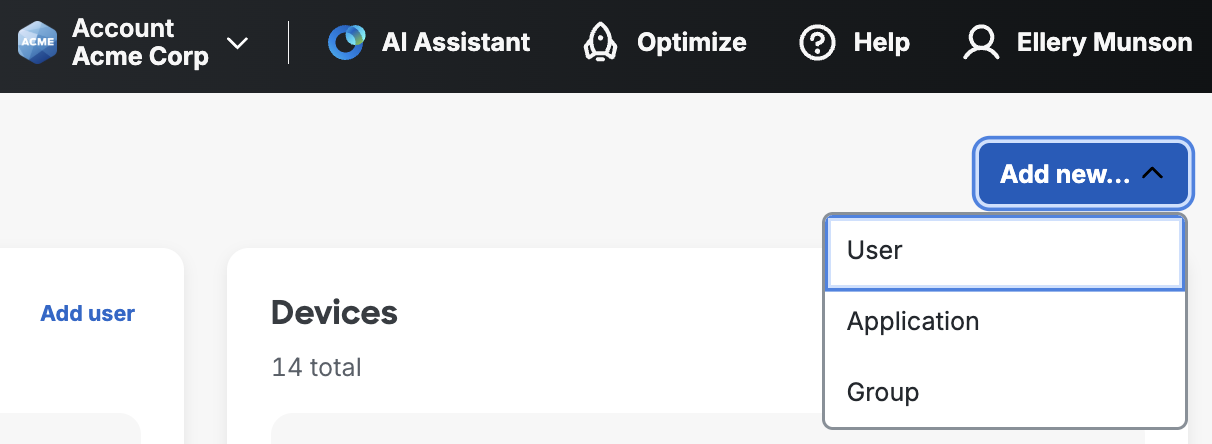
Click the Add New... button in the top right of the dashboard to quickly create a new user, group, or application. You can also click the navigation link on the left for the type of object you want to create.
Click on your name in the upper-right corner to access your administrator account action menu. Click Edit Profile to change the name associated with your administrator login, reset your password for the Admin Panel, update your secondary authentication phone number or add a passkey, and activate Duo Mobile for Admin Panel login. You can also click Log Out on this menu to end your Duo administrator session. You'll be logged out of the Admin Panel automatically after 60 minutes of inactivity.
Navigation
Manage or view different object types by clicking the links on the left side of the Admin Panel. Click on the menu icon in the upper left to collapse the navigation menu. You may be shown a subset of these links, depending on your assigned administrative role.
- Home: Your account overview and summary.
- Users: View, create, and modify users and administrators, and configure external directory sync. See Managing Users and Managing Duo Administrators.
- Devices: View, create, and assign phones, endpoints, hardware tokens, WebAuthn devices, and other authentication and access devices; see Device Insight information; and configure Trusted Endpoints and Duo Desktop Shared Device Authentication. See Managing Devices.
- Policies: Define and assign access policies by user group and per application, and configure Duo Passport. See Policy & Control.
- Applications: View, add, and modify applications and manage Duo Single Sign-On and Duo Passwordless configurations. See Protecting Applications.
- Reports: View authentication events, administrator actions, and other valuable reports. See Logs and Reports. All administrator roles, except Billing, can view reports.
- Monitoring: Manage Cisco Identity Intelligence. Available in Duo Premier and Duo Advantage plans. Trust Monitor remains accessible to customers who created their Duo accounts before September 29, 2025, and will be removed in July 2026.
- Billing: Manage payment methods, change your Duo subscription, view and download your monthly billing history, and purchase telephony credits or Duo hardware tokens. Note that customers who purchased Duo licenses or telephony credits through Cisco Commerce Workspace (CCW) must log in to CCW to manage billing, download invoices, or purchase additional telephony credits.
- Settings: Change global settings for your Duo service. See Global Settings.
- Free Trial: Try a higher edition up to twice a year (available to paid accounts only).
New administrators whose accounts were created through Cisco Security Cloud Control (SCC) after May 11, 2026 will have limited access to features/pages in the Admin Panel.
AI Assistant, Optimize, and What's New
Click the AI Assistant item at the top of the dashboard to use the Cisco AI Assistant for Duo, which interprets your natural language prompts to troubleshoot user access issues and find setup and configuration answers from documentation.

Duo Essentials, Duo Advantage, and Duo Premier plans offer a guided onboarding journey. Launch it with Setup. See the Getting Started page for more information about guided onboarding and optimization of your Duo deployment.
Discover new features and recent changes by clicking Help.
Help
You'll find new features and support information and more under Help on the top right of the dashboard.
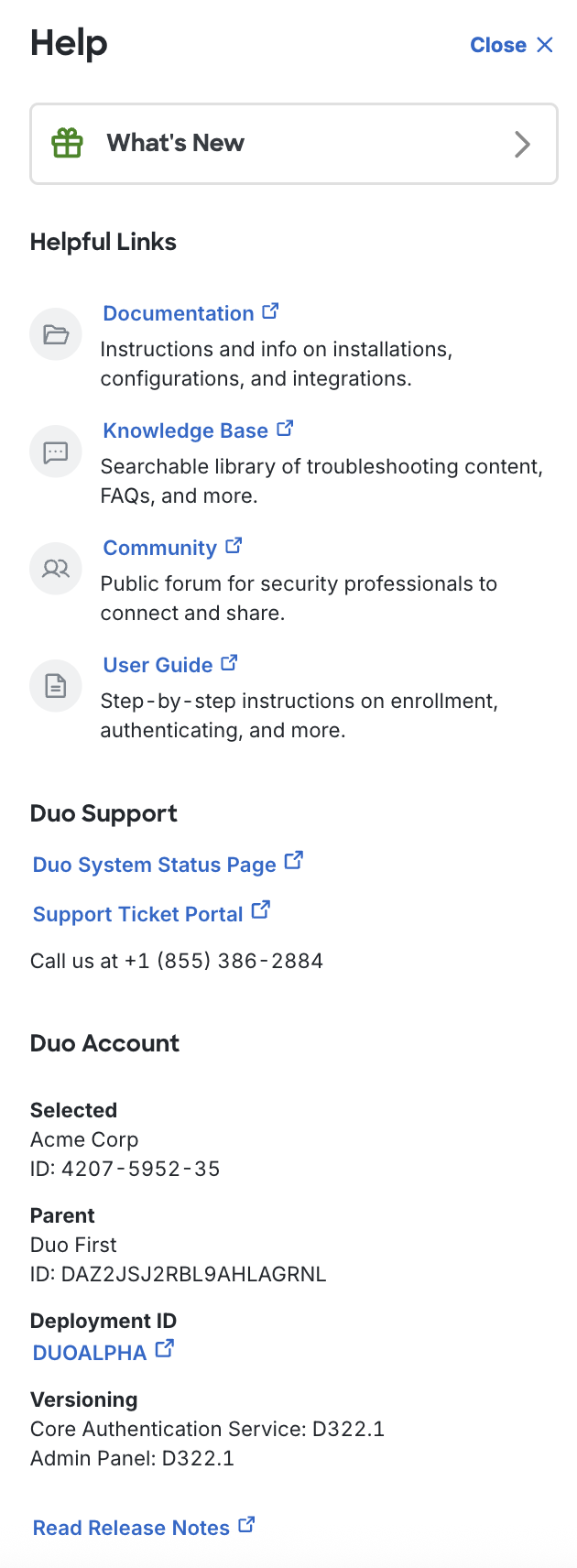
Click on the What’s New button to view descriptions of new features and recent changes.
The "Helpful Links" list different sites with useful information about Duo. The Documentation, Knowledge Base, and User Guide sites contain technical instructions and helpful articles for Duo administrators and end users.
Duo Essentials, Duo Advantage, and Duo Premier customers may click the Support Ticket Portal link to create and manage support cases in the Duo customer portal. User Protection Suite customers will see information about contacting Cisco Worldwide Support.
Both the Duo System Status Page link and Deployment ID information below your account information take you to the Duo Service Status page, where you can see the current operational status of Duo's cloud services.
You'll need your Duo Account information if you contact Duo support via phone or email instead of using the Support Ticket Portal link. You'll find your Deployment ID under your Duo account information as well.
The Versioning information helps you determine what Duo release updates apply to your account. You may need to provide this information if you contact Duo Support. Check our Release Notes to learn more about new features, fixes, and updates to Duo's service and applications.
Viewing Information
Use the search field at the top of the Admin Panel to quickly find a particular user (by username or alias), phone or token device, group, or application.
Clicking most of the navigation items on the left of the Admin Panel window takes you to a table view of those objects (i.e. clicking Users shows you a table of Duo users).
Information tables in Duo are either paginated, where you can change the page size from 10 to 100 items and click forward and back between pages, or the table shows a Load More button at the bottom of the current data view that you can click to show more information. Most tables have a search field in the upper right that you can use to filter records in place.
If the table has an Export button, you can click that to select from the available export options, which may include CSV, JSON, or PDF format, or URL which gives you a direct link to your current view. If you've filtered the information in the table using search, the downloaded information only includes those search results.
Beta Features
As part of our ongoing efforts to bring customers new capabilities we will make features, settings, and applications available ahead of general availability. This is a chance for you to opt into new and important features sooner and validate them in your environment.
Features covered here might be noted by a "Beta" badge or banner in the Admin Panel or referred to as "Beta" features in communications, release notes, and the "What's New" feed.
Beta features and releases are fully supported by Duo technical support. Beta features may enable new behaviors and options by default.
For more information on Duo’s development process and release phases see the article What do Duo’s product release terms like “Alpha release” or "Beta release" mean? in the Duo Knowledge Base.
The "Beta" release phase was previously known as "Early Access" or "Public Preview".
Please contact your Duo representative with any questions or concerns.
Reports
All administrator roles except Billing can view reports. Clicking the Reports link on the left side of the Admin Panel opens a side menu with a list of reports.
See the Logs and Reports page to learn about reporting available in Duo.
Troubleshooting
Need some help? Try searching our Knowledge Base articles or Community discussions. For further assistance, contact Support.
